Where to Buy Managed SASE Services with Global Coverage
Traditional models built on multi-vendor stacks, regional MPLS contracts and bolt-on security appliances tend to come with greater operational complexity, inconsistent policy enforcement and coverage gaps, therefore the choice to move to SASE has become increasingly popular.
Traditional models built on multi-vendor stacks, regional MPLS contracts and bolt-on security appliances tend to come with greater operational complexity, inconsistent policy enforcement and coverage gaps, therefore the choice to move to SASE has become increasingly popular.
In this article we'll provide you with a structured, vendor-neutral guide to which providers offer managed SASE (with global reach) and how to navigate the procurement process with our question set designed to get you comparable, decision-ready vendor responses.
What Defines Managed SASE with Global Coverage?
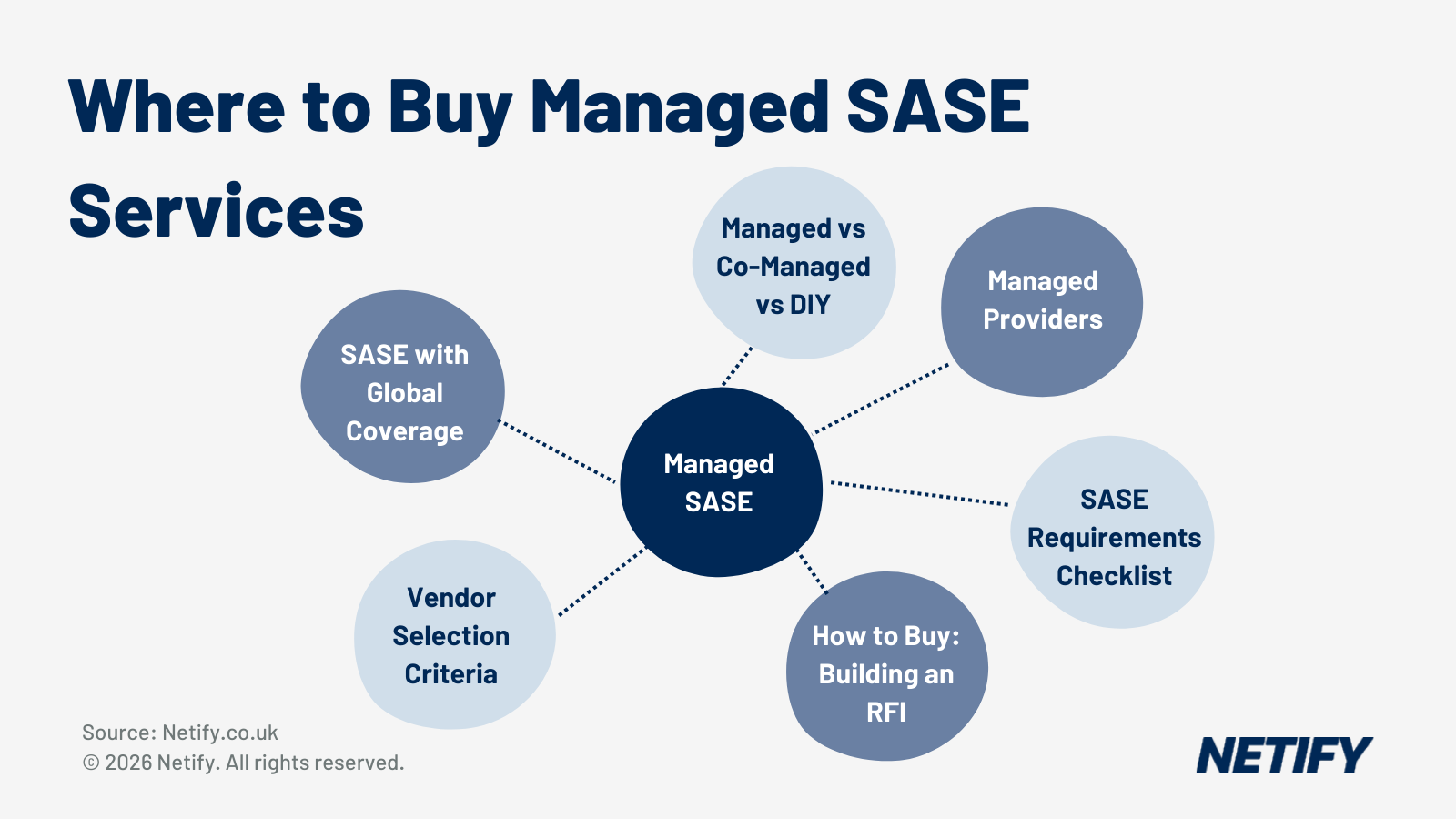
SASE services are delivered in three primary models, each with distinct operational responsibilities - we'd recommend understanding the difference between each and their responsibilities prior to any procurement process.
DIY SASE means the organisation contracts directly with a SASE vendor, deploys its own edge hardware or software and operates policy configuration, monitoring and incident response using internal network and security teams.
Co-Managed SASE introduces a shared responsibility model, where an MSP or MSSP handles day-to-day monitoring and first-line response whilst the customer retains control of strategic policies and change operations.
Fully managed SASE moves design, deployment, monitoring and lifecycle management to the provider (with the customer focused on outcomes) high-level policies and governance.
| Criteria | DIY SASE | Co-Managed SASE | Fully Managed SASE |
| Policy configuration | Customer-owned | Shared responsibility | Provider-owned with customer approval |
| Monitoring & incident response | Customer SOC | Shared SOC / escalation | Provider 24/7 SOC |
| Hardware lifecycle | Customer manages | Varies | Provider manages refresh cycles |
| Vendor relationship | Direct with vendor | Divided | Single contract with MSP/MSSP |
| Best suited for | Large in-house NetSec teams | Mid-market with partial in-house capability | Organisations prioritising OpEx and outsourced expertise |
It's worth noting, however, that choosing a deployment model is only part of the consideration for many organisation - for a managed SASE solution to deliver beneficial multi-national capabilities, these organisations should consider which providers meet the following criteria as these can have a significant impact on ROI.
- PoP density and regional distribution - providers must demonstrate sufficient edge locations across EMEA, APAC and the Americas to serve users without backhauling traffic. A minimum threshold of PoPs in each major region should be confirmed, not assumed.
- Private backbone vs public internet transit - Providers operating private Layer 2 or Tier 1 backbones offer more predictable latency and packet delivery than those relying entirely on public internet paths, providing you with a greater guarantee of maintained performance improvements.
- Data residency and sovereignty controls - Traffic inspection and logging must align with your organisations regulatory and jurisdictional requirements (such as GDPR in Europe, data localisation laws in specific APAC markets and sector-specific regimes).
- Regional NOC and SOC capabilities - Local-language support and regional escalation paths can be critical elements for effective incident response, particularly outside standard business hours.
- Latency SLAs - Leading providers commit to less than 50 ms latency between the user and the nearest PoP in major regions - this should therefore be a contractual commitment (not a marketing estimate) and, even better still, should be backed by significant compensation in the event of failure to meet agreements..
- Compliance certifications - If you're in a regulated industry, ensuring compliance with ISO 27001, SOC 2, PCI DSS, HIPAA, NHS DSPT or GDPR are all required to be demonstrable per hosting region, with audit evidence available on request.
Managed SASE Providers with Global Coverage
To help get you started with procurement, we've identified the primary providers capable of delivering managed SASE across a wide range of international territories, each with documented global infrastructure or backbone presence.
| Provider | SASE Vendor(s) | Global PoPs | Managed Model | Private Backbone | Key Sectors | HQ Region |
| Lumen | Fortinet, Versa | 100 | Pro-managed, self-managed | Yes (Tier 1 IP backbone) | Enterprise, public sector | US |
| BT | VMware, Palo Alto, Zscaler | 180 | Fully managed | Yes (Global MPLS/IP backbone) | Financial services, healthcare | UK |
| Hughes | Fortinet, Prisma, Cato, Netskope | 100 | Fully managed | Hybrid (satellite terrestrial) | Enterprise, government | US |
| Orange Business | Fortinet, Netskope, Palo Alto | 220 | Fully managed | Yes | Multinational enterprise | France |
| Verizon | Palo Alto, Zscaler, Versa, Fortinet | 200 | Fully managed | Yes (global IP backbone) | Enterprise | US |
| Aryaka | Aryaka (native) | 40 | Fully managed as-a-service | Yes (owned L2 backbone) | Manufacturing, finance | US |
| Open Systems | Open Systems (native) | 35 | Fully managed | Yes | Manufacturing, logistics | Switzerland |
| GTT | Fortinet, Versa | 600 | Fully managed | Yes (Tier 1 backbone) | Multinational enterprise | US |
| Cato Networks | Cato (native) | 85 | Self-managed, partner-managed | Yes (global private backbone) | Mid-market, enterprise | Israel / US |
| Vodafone Business | Cisco, Fortinet, Zscaler | 130 | Fully managed | Yes | Enterprise, public sector | UK |
| Tata Communications | Versa, Palo Alto, Cisco (Izo SASE) | 400 | Fully managed | Yes (Tier 1) | Finance, manufacturing | India |
| NTT | Palo Alto, Cisco, Fortinet, Netskope | 190 countries | Fully managed | Yes | Enterprise, government | Japan |
| Deutsche Telekom | Fortinet, Palo Alto | 100 | Fully managed | Yes | Enterprise, automotive | Germany |
| Wipro | Palo Alto, Zscaler, Netskope (multi-vendor) | Vendor-led | Fully managed MSSP | No (partner networks) | Healthcare, finance, BFSI | India |
| IBM | Cisco, Zscaler, Palo Alto, Netskope (multi-vendor) | Vendor-led | Fully managed, co-managed | No (partner networks) | Regulated sectors, global enterprise | US |
| Accenture | Multi-vendor | Vendor-led | Fully managed | No (partner networks) | Enterprise, public sector | Ireland |
The providers above fall into three broad categories, each with a different approach to backbone ownership, SASE stack design and how much of the operational burden they take on (understanding the distinction will help you narrow your shortlist before issuing an RFI). Should you wish to read more about SASE vendors, we'd recommend the below article where we've gone into detail on each one.

Deeper Dive: We've compared the top SASE vendors
However, we've found that one of the best ways to quickly categorise vendors is how they offer their coverage - often falling into one of global network providers, cloud-native SASE platforms or system integrators/managed security service providers.
Managed SASE Requirements Checklist
Before engaging with providers though, we'd strongly recommend that IT decision makers document a structured requirements set and the associated questions around them - undefined requirements produce incomparable proposals and can slow down your procurement process massively.
We've curated the checklist below to cover what we believe to be the eight most important categories that consistently determine whether a managed SASE solution is viable for a given organisation.
| Requirement Category | Key Questions | Why It Matters |
| Global PoP coverage | Which regions require sub-50 ms latency to the nearest SASE PoP? Are there jurisdictions with data residency restrictions? | Ensures local security inspection without backhauling traffic across borders, which can breach both performance SLAs and compliance requirements. |
| Security stack convergence | Is the SASE stack natively integrated (single-pass inspection) or composed of separate products bundled together? | Bundled products introduce additional latency, policy gaps and multiple management consoles, increasing operational overhead. |
| Managed service scope | Who owns policy configuration, day-to-day changes, monitoring and incident response? What is the escalation path to L3 engineers? | Clarifies the division of responsibility between in-house teams and the provider, avoiding gaps during incidents. |
| Compliance and certification | Which certifications are held per hosting region? ISO 27001, SOC 2, PCI DSS, HIPAA, NHS DSPT, GDPR alignment. | Regulated industries require documented controls and audit evidence, not marketing assertions. |
| SLA structure | Which metrics are SLA-backed: per-PoP availability, end-to-end latency, packet loss, mean time to resolution? How are service credits calculated? | Provides objective measures to assess provider performance and financial accountability for outages or degradation. |
| Integration and migration | How will the platform integrate with existing firewalls, SIEM and identity providers? What is the migration plan from MPLS or legacy VPN? | Reduces parallel operations and ensures a controlled transition away from legacy infrastructure with minimal business disruption. |
| Commercial model | Per-user, per-site or bandwidth-based pricing? What contract terms and exit provisions are available? | Pricing models vary significantly and affect total cost of ownership over three to five years. |
| Sector-specific requirements | Does the provider have documented deployments and references in your specific sector (healthcare, manufacturing, retail, finance)? | Sector experience reduces implementation risk and ensures regulatory and operational requirements are understood from the outset. |
The checklist above is designed to be taken directly into a procurement process - if any category is left undefined before you approach vendors, this may lend itself to proposals that are difficult to compare.
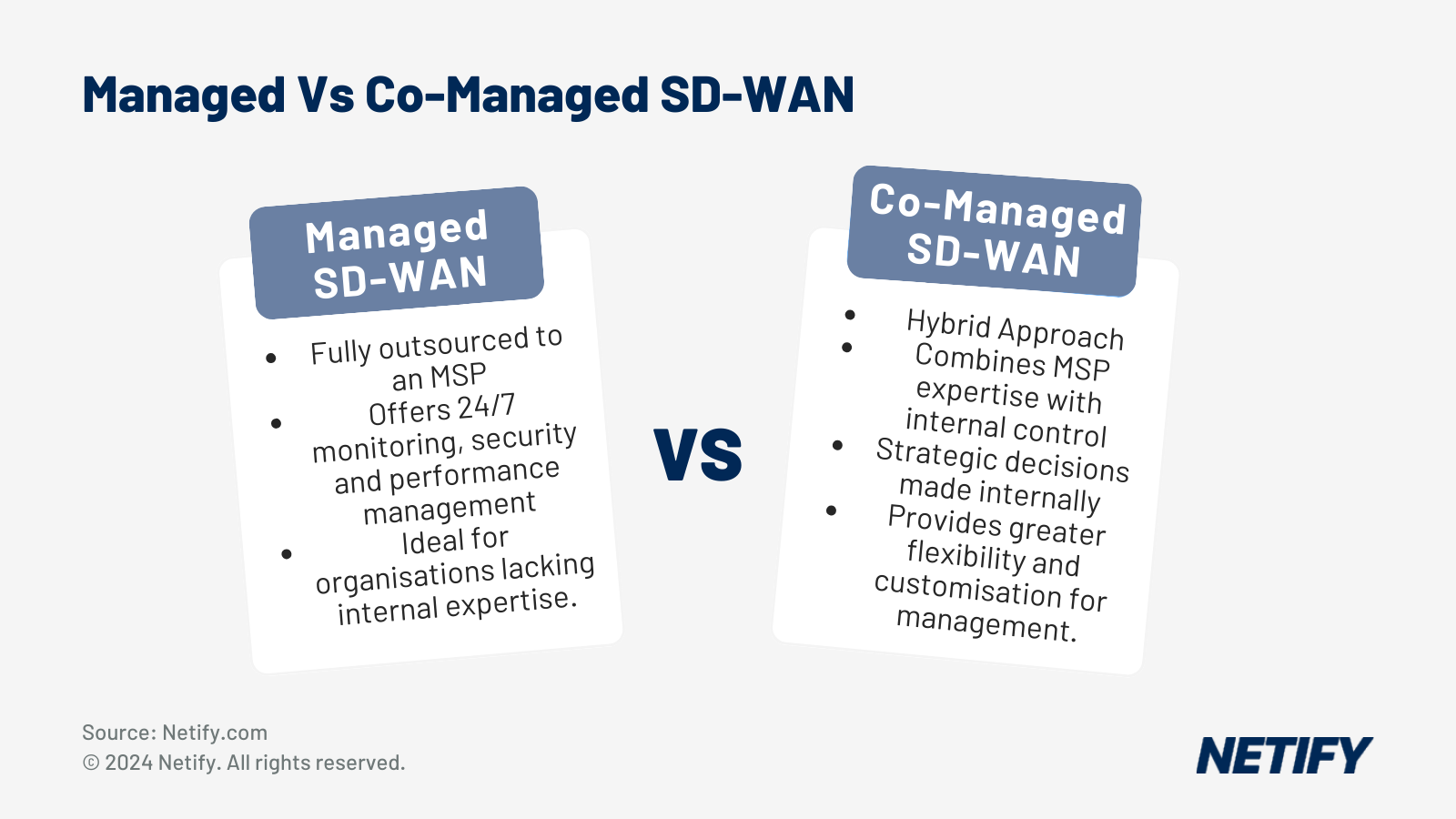
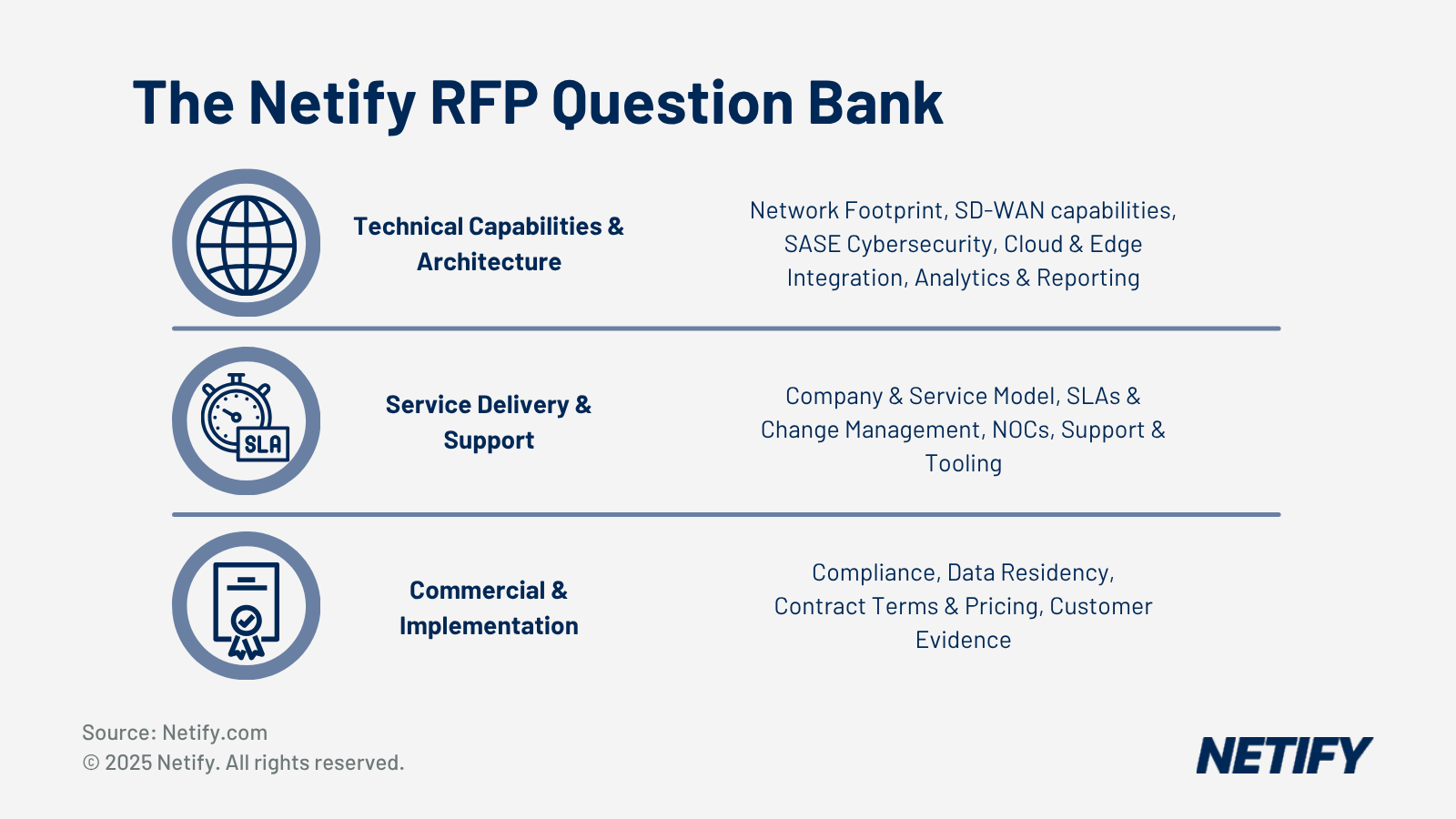
The Netify SASE RFI Quick Builder mirrors these requirement categories directly, converting them into structured RFP question sets that ensure all providers answer the same questions across global PoP coverage, stack design, compliance and commercial model.
How to Buy Managed SASE - The RFI Process
Once you've created your Managed SASE Requirements Checklist (see the above section), rather than sending this as an ad-hoc questionnaire to a short list of vendors, we'd advise that you utilise a structured RFI process, as this will enable you to garner a broader and more objective market comparison. That's why we've built the Netify SASE RFI Builder, which offers a free way to achieve this far more quickly than traditional methods.
- Step 1: Define requirements: Use the checklist in Section 4 to document site locations, remote user counts, target regions, latency expectations, compliance obligations, preferred security functions (ZTNA, SWG, CASB, FWaaS) and internal operating model.
- Step 2: Generate an RFI: We'd strongly recommend that you use the Netify SASE RFI Builder - it's the simplest way to generate an RFI. The builder applies AI-assisted question generation across 12 procurement categories, including company credentials, SD-WAN capabilities, SASE security features, SLAs, compliance and implementation methodology and you'll instantly get a structured RFI tailored to your specific needs, all of which is assembled in minutes (rather than weeks with other methods).
- Step 3: Publish to the Netify marketplace: Once you submit it, the RFI is then distributed to more than 30 curated vendors and managed service providers with UK, North American and multinational coverage, saving you the task of researching vendors and individually sending them your requirements.
- Step 4: Receive capability statements: Providers respond with structured answers mapped directly to requirement categories, enabling direct comparison of their responses, such as their PoP coverage, managed service models, compliance posture and commercial terms.
- Step 5: Shortlist and evaluate: Use Netify's scoring framework to rank providers, request demonstrations and proofs of concept and gather detailed global connectivity pricing through the same workspace.
Further Reading: Our 87 Vendor-Neutral Questions that you MUST ask SASE vendors.
Why Netify for SASE RFIs
Most managed SASE procurement processes start the same way, a shortlist of familiar vendor names, a set of ad-hoc questions sent out individually and proposals that arrive in different formats and answer different things.
With Netify, our SASE RFI Quick Builder was built specifically to address the structural problem with ad-hoc procurement. As a vendor-neutral marketplace, our focus is helping you to generate a consistent, structured question set across the full range of procurement categories and getting that RFI simultaneously distributed to a curated list of more than 30 vendors and MSPs.
Managed SASE Vendor Selection Criteria
And once vendors have replied with their capabilities, we'd then recommend a weighted scoring model to help with your objective comparison across shortlisted providers and helps align IT, security and procurement stakeholders on a shared evaluation framework.
Why Weighted Over Average Scoring?
Given that every business is different, the features that you'll get the most value from will likely differ from other businesses - therefore placing a weight on the score of each criterion allows you to gain a more accurate picture of how vendor solutions will best benefit your specific use case.
| Evaluation Criterion | Weight | Vendor A | Vendor B | Vendor C |
| Global PoP coverage and latency SLA | 0.2 | /10 | /10 | /10 |
| Security stack convergence (native vs bundled) | 0.15 | /10 | /10 | /10 |
| Managed service depth (L1-L3 support) | 0.15 | /10 | /10 | /10 |
| Compliance certifications per region | 0.15 | /10 | /10 | /10 |
| Migration pathway and integration | 0.1 | /10 | /10 | /10 |
| Commercial flexibility (pricing, terms, exit) | 0.1 | /10 | /10 | /10 |
| Sector experience and customer references | 0.1 | /10 | /10 | /10 |
| Platform visibility and reporting | 0.05 | /10 | /10 | /10 |
| Weighted Total | 1 | /10 | /10 | /10 |
To use this matrix, score each provider from 1 to 10 for every criterion based on RFI responses and supporting documentation, then multiply each score by the corresponding weight and sum the results to produce a weighted total out of 10. This approach best supports structured debate between stakeholders, provides a documented basis for down-selection decisions.
Conclusion
Managed SASE with global coverage can be sourced from global network service providers, cloud-native SASE platforms and systems integrators, each offering different balances of backbone ownership, platform integration and operational delivery model.
The key aspect of procurement is not necessarily the vendor selection process, but the process(es) you take to evaluate your business' specific needs and how solutions can support your potential growth. A structured RFI produces comparable responses, reduces procurement timelines and surfaces requirements that ad-hoc conversations miss and that's why we'd strongly advise businesses utilise the Netify RFI Builder, which provides a vendor-neutral mechanism to define requirements, distribute to a curated pool of more than 30 global providers and evaluate responses within a single workspace.
The Netify SASE RFI Quick Builder mirrors these requirement categories directly, converting them into structured RFP question sets that ensure all providers answer the same questions across global PoP coverage, stack design, compliance and commercial model.

Harry holds a BSc (Hons) in Computer Science from the University of East Anglia and is ISC2 Certified in Cybersecurity (CC). He serves as a Cybersecurity Writer here at Netify, where he specialises in enterprise networking technologies. With expertise in Software-Defined Wide Area Networks (SD-WAN) and Secure Access Service Edge (SASE) architectures, Harry provides in-depth analysis of leading vendors and network solutions.
Fact checked by: Robert Sturt - Managing Director, Netify
Frequently Asked Questions
What is the difference between managed SASE and co-managed SASE?
With fully managed SASE, the provider takes ownership of policy design, deployment, monitoring, incident response and hardware lifecycle. The customer defines outcomes and approves high-level policy changes, but day-to-day operations sit entirely with the provider.
Co-managed SASE splits responsibility: the customer retains control of strategic policies and some change operations, while the MSP or MSSP handles monitoring and first-line incident response. Co-managed models suit organisations with partial in-house network or security capability that want to retain visibility without running a full internal SOC.
How many PoPs does a managed SASE provider need to offer genuine global coverage?
There is no universal minimum, but the practical threshold for consistent less than 50 ms latency across EMEA, APAC and the Americas is generally considered to be 40 or more PoPs, provided they are geographically distributed rather than concentrated in a single region.
Cloud-native providers such as Aryaka operate effectively with around 40 owned PoPs by supplementing coverage with optimised transit.
Global carriers such as GTT and Orange Business operate hundreds of PoPs, but raw PoP count is less important than regional spread and whether each PoP performs local traffic inspection.
Buyers should request per-region latency data rather than relying on headline PoP totals.
What security functions should a managed SASE platform include?
A complete SASE platform should converge SD-WAN with a full security service edge (SSE) stack.
The core SSE components are:
- Zero Trust Network Access (ZTNA),
- Secure Web Gateway (SWG),
- Cloud Access Security Broker (CASB)
- Firewall-as-a-Service (FWaaS)
Mature platforms also often include DNS security, data loss prevention (DLP) and sandboxing for unknown file analysis.
The critical distinction is whether these functions are delivered through a natively integrated, single-pass inspection engine or assembled from separate acquired products. Bundled stacks introduce latency, policy inconsistencies and additional management overhead that undermine the operational case for SASE.
How does managed SASE handle data residency requirements?
Data residency compliance depends on where traffic is inspected, where logs and policy data are stored and how the provider handles cross-border data flows.
Under GDPR, for example, personal data must not be processed in jurisdictions without adequate protection unless specific contractual mechanisms are in place.
Credible managed SASE providers publish a data processing addendum (DPA), document the countries in which each PoP performs traffic inspection and offer regional data storage options. Buyers in regulated sectors should request a detailed data flow map for each operating region and verify that the provider holds relevant certifications (ISO 27001, SOC 2 and region-specific frameworks, such as NHS DSPT in the UK) per hosting location rather than at a corporate level only.
What pricing models are used for managed SASE services?
Managed SASE is priced under three broad models. Per-user pricing is common with cloud-native platforms and suits organisations with a high proportion of remote or mobile workers relative to fixed sites. Per-site pricing is more typical of global carriers and suits branch-heavy organisations with predictable site counts. Bandwidth-based pricing is used by some providers and can become expensive as traffic volumes grow. Most enterprise contracts blend elements of all three, with a base commitment covering a defined user count and site list and consumption charges for overages and contract terms typically run three to five years.
Buyers should scrutinise exit provisions carefully, as switching costs in managed SASE (including hardware retrieval, configuration migration and re-onboarding) can be significant.
How long does a managed SASE migration typically take?
Migration timelines depend on the size of the existing estate, the complexity of the architecture and the provider’s deployment methodology:
- A mid-market organisation migrating from a regional MPLS network with a single security stack can typically complete a phased deployment within three to six months.
- A multinational migrating from a multi-vendor, multi-carrier architecture with legacy VPN infrastructure and complex compliance requirements may take 12 to 18 months.
Providers should be asked to detail their standard onboarding methodology, the number of sites they can bring live per month and how they manage parallel running of legacy and SASE environments during the transition period.
Which managed SASE providers are best suited to UK and European organisations?
UK-headquartered carriers (such as BT and Vodafone Business) offer strong EMEA PoP density and documented GDPR and NHS DSPT compliance posture, making them a natural starting point for UK public sector and regulated-industry buyers.
Orange Business and Deutsche Telekom are well positioned for European multinationals, particularly where data sovereignty across EU member states is a concern.
For organisations requiring a single global provider across EMEA and APAC, NTT and Tata Communications both operate extensive backbone infrastructure in both regions.
Cloud-native platforms such as Cato Networks and Aryaka are viable for UK and European mid-market organisations that prefer a unified stack over a carrier-led multi-vendor approach.