Market Guide to Next-generation Firewall-as-a-service (FWaaS)
The migration of enterprise workloads to the cloud has fundamentally altered the requirements for network security. Traditional security models, which relied on a protected physical perimeter and hardware firewalls to control traffic, are no longer sufficient in an era of distributed applications and remote work. As organisations shift from internal systems to SaaS products and host custom applications on cloud infrastructure, the need for software-defined security services has become clear.
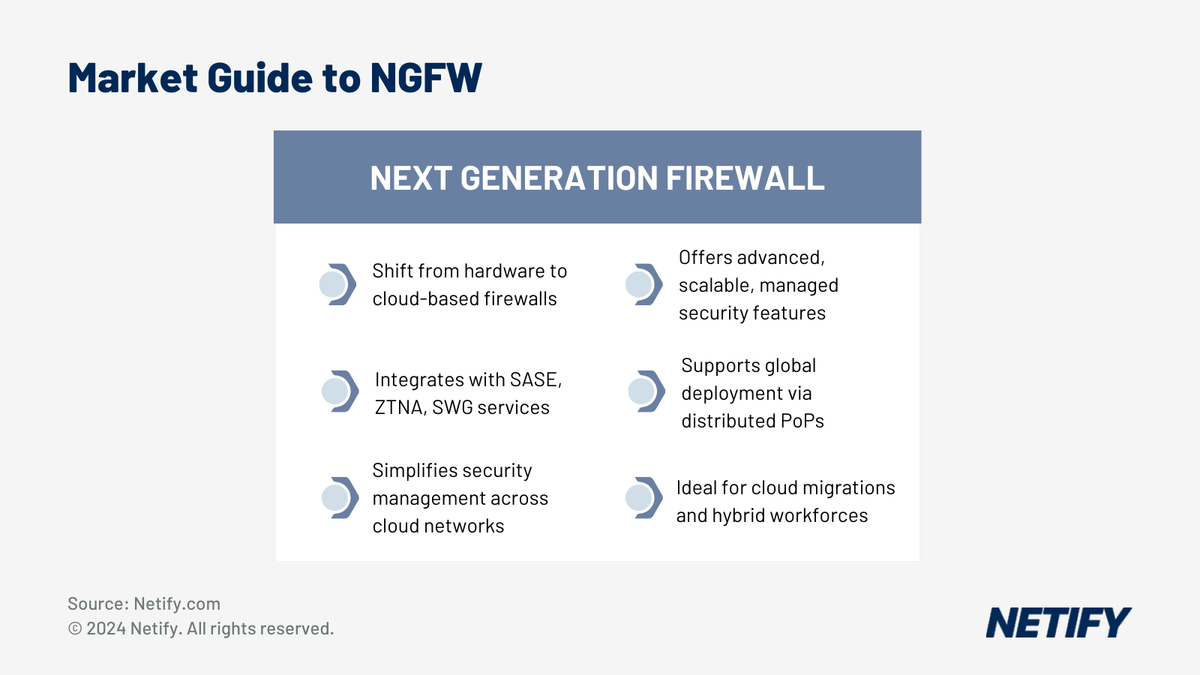
Firewall-as-a-service (FWaaS) has emerged as the cloud-native alternative to physical appliances. By delivering next-generation firewall capabilities as a hosted, managed service, FWaaS allows organisations to secure users and data regardless of their location. This shift mirrors the broader “cloud-ification” of enterprise infrastructure, where hardware-based controls are replaced by virtualised services that manage traffic across global networks. While FWaaS provides the foundational security features of a next-generation firewall, it is increasingly delivered as part of a broader framework.
Modern security architectures now focus on the convergence of networking and security into a single platform. This evolution ensures that FWaaS does not operate in isolation but works alongside other cloud-delivered services to provide a comprehensive security posture for the modern enterprise.
Core Features
While individual vendor implementations vary, a standard FWaaS platform includes several core next-generation firewall features:
- Stateful and deep packet inspection (SPI/DPI): Analysing traffic at the application layer to identify and block threats.
- Intrusion detection and protection (IDS/IPS): Monitoring network traffic for signs of malicious activity and taking action to prevent attacks.
- Layer 7 application awareness: Identifying and controlling traffic for specific applications and protocols, including those delivered over HTTPS.
- TLS 1.3 inspection: The ability to decrypt and inspect encrypted traffic, which is now a standard requirement for cloud security.
- Identity and access management (IAM) integration: Connecting with platforms like Okta or Azure AD to apply security policies based on user identity and group membership.
- Centralised management console: A single web-based interface for policy configuration, deployment, and reporting across the global network.
Feature parity between leading vendors is high, meaning that technical checklists often look similar. Differentiation in the market now tends to come from the underlying architecture, the number and location of PoPs, the depth of SASE integration, and the specific pricing models offered.
Benefits and Use Cases
Traditional firewalls, whether implemented as a hardware device or virtual appliance running on a multi-NIC server, were designed for enterprise networks using perimeter-based security with little internal network segmentation. However, the rise of cloud infrastructure (IaaS), SaaS applications and home-office employees has broken this moat-and-castle security model and left users vulnerable without cloud-based security systems. FWaaS fixes the limitations of perimeter firewalls via a cloud control plane and virtual edge architecture that can deploy firewall instances on any enterprise network segment, including cloud VPCs.
FWaaS is appropriate for any organisation migrating workloads and applications to the cloud and can be used on any network including enterprise data centres, public cloud environment, branch and home offices, distribution centres and remote manufacturing and retail locations. FWaaS typically supplements existing data centre firewalls that are still used for internal network segmentation, although smaller companies with minimal internal infrastructure might choose to go all-in with cloud security services like FWaaS.
Aside from the flexibility to be deployed at any location worldwide, FWaaS has several other benefits:
- Scalable infrastructure to handle seasonal and other workload variations.
- A distributed network topology that doesn't require backhauling traffic to data centre chokepoints to perform firewall inspection, causing large increases in latency.
- Facilitates micro-segmented network designs that create tight controls around individual applications or systems to limit the propagation of APTs and provide additional access controls for sensitive applications and data.
- Significant reduction in the overhead of managing firewall infrastructure and software.
- Easily integrated with public cloud environments which enables applying consistent security policies and configurations across multi-cloud deployments.
- Rapid scalability to handle temporary capacity spikes and long-term growth without requiring new hardware or software licenses.
- Tight integration with a vendor's other connectivity and security services such as SD-WAN, ZTNA, SWG and CASB.
As the last point implies, most vendors offer FWaaS as part of a broader suite of security services, however, our focus here is solely on their firewall products.
Many firewall vendors now have a FWaaS product, while others are cloud-native startups without a legacy product line. Additionally, many carriers, CDNs and ISPs offer a FWaaS based on one of the commercial NGFWs.
FWaaS and Cloud
The spread of cloud services throughout the enterprise has long threatened traditional security designs based on a protected perimeter with hardware firewalls to control traffic flows. As organizations increasingly use cloud infrastructure (IaaS) to host custom applications and migrate commodified software from internal systems to SaaS products, securing clients, data, systems and applications has become impossible without replacing hardware-based controls over physical network segments with software-defined services managing virtual networks. Just as every other form of enterprise infrastructure and software has been cloud-ified, network security products have followed the cloud migration, with a thriving market in security-as-a-service offerings including:
- Next-generation firewall (NG-FWaaS)
- Zero-trust network access (ZTNA)
- Secure Web Gateway (SWG)
- Cloud Access Security Broker (CASB)
- Extended Detection and Response (XDR)
FWaaS and NGFW
Firewall-as-a-service (FWaaS) provides the features of a next-generation firewall as a managed, hosted, shared service available from both traditional firewall providers like Palo Alto Networks or a new breed of cloud-native security companies like Cato Networks or Zscaler. As such, they provide all the features of an NGFW including:
- Stateful and deep packet inspection (SPI/DPI)
- Intrusion detection and protection (IDS/IPS)
- Layer 7 application awareness to protect software delivered over HTTPS, SMTP or other protocols (for example, these are the dozens used by Apple software)
- Support for encrypted traffic (TLS, DTLS)
- Access to threat intelligence platforms that aggregate, correlate, and analyse anonymised data from thousands of networks and customers to proactively update security policies to counter new threats. According to Cisco, it takes most enterprises between 100 to 200 days to detect a threat, ample time for professional attackers to scan a network, find security gaps and infiltrate weak systems. Updating NGFWs with data from a threat intelligence service can reduce the detection time to minutes.
- Integration with identity and access management (IAM) platforms and federated identity and SSO protocols like OAuth, OpenID Connect (OIDC) and SAML to enable customised policies for users and groups.
- Network visibility and reporting of traffic statistics, events, anomalies and network performance.
- Web-based management console that consolidates policy configuration, deployment and reporting under a unified interface.
- Programmable APIs and integrations to third-party products and services that enable automating routine tasks like policy management, risk assessments, and compliance audits. These also facilitate sharing alerts and data with other security tools.
FWaaS providers typically offer other network security services like ZTNA and SWG that are delivered from a worldwide set of POPs positioned within a few milliseconds of most users. For example, Cato Networks has 60 POPs providing localised access on every continent. POPs are connected to multiple data carriers like AT&T, BT, NTT, Telia and others to onboard traffic and provide reliable, secure, high-bandwidth connectivity to the FWaaS infrastructure and other cloud providers. For example, Zscaler can sustain more than 700Gbps to many cloud providers.

FWaaS and other security service providers increasingly use AI machine learning (ML) and deep learning (DL) models to analyse network telemetry, event logs and packet flows to identify and flag anomalous behaviour. Vendors often aggregate anonymised data from all customers to better train AI models and find new and unusual threats before they become widespread. Many combine AI analysis with a cloud-based application sandbox that will contain and test suspicious files or code, but not positively identified threats, for malicious behaviour in an isolated virtual environment before passing the code or packet stream onto its destination.
Aside from providing regularly updated NGFW features, running on shared cloud infrastructure allows FWaaS products to dynamically scale firewall capacity to meet changing needs. Such scalability is particularly important for companies like retailers or online entertainment and gaming providers with highly variable and seasonal traffic or anytime an organisation’s network is under DDoS attack.
FWaaS and SASE
The most significant shift in the market is the convergence of FWaaS into the Secure Access Service Edge (SASE) model. Defined by Gartner in 2019, SASE is an architecture that combines wide area networking with a cloud-delivered security stack. In this model, FWaaS is not a standalone product but one of the five core components of a SASE platform, alongside SD-WAN, Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), and Zero Trust Network Access (ZTNA).
In practice, this means that most major vendors now deliver their firewall capabilities as part of a broader SASE subscription. When evaluating providers, buyers are typically looking at the full security stack rather than just the firewall features. The depth of integration between these services is a critical factor, as a platform with a strong FWaaS but a weak SWG may not meet the needs of an organisation with a heavy reliance on web-based applications.
This convergence has changed the procurement process for IT teams. Instead of managing separate contracts and consoles for firewalls and gateways, organisations can now manage their entire security and networking environment through a single vendor. This simplifies administration and ensures that security policies are applied consistently across all types of traffic, whether it is destined for the internet, a SaaS application, or a private data centre.
Standalone FWaaS deployments remain a valid option for organisations that have already invested in an SD-WAN solution and do not wish to replace it. However, the market trend is moving towards unified platforms that provide a more cohesive approach to security. Understanding this context is essential for buyers to ensure they are selecting a solution that aligns with their long-term network transformation strategy.
FWaaS Implementation
FWaaS implementations are typically segmented into several logical components, namely:
- A centralised, highly available control plane for enforcing policy across all firewall instances.
- Edge nodes for onboarding and inspecting traffic and enforcing security policies via localised firewall nodes. The control plane usually uses geolocation of the client IP address to automatically direct traffic to the nearest edge node. Should users move and get redirected to another node, the control plane ensures that user- and location-specific security policies follow along.
- Logging and telemetry collection and analysis. Log servers can also stream data aggregated from an organisation's fleet of firewalls to enterprise SIEM or data analysis systems.
- Sandbox servers to store and analyse suspicious files or code segments.
Other than the edge access nodes, the backend components are invisible to the user with traffic and data automatically flowing within the provider's cloud environment to the appropriate subsystem.
Who are the top FWaaS (Firewall-as-a-service) providers?
The top FWaaS (Firewall-as-a-Service) providers are Cato Networks, Open Systems, Palo Alto, Versa and Zscaler. Comparison requires understanding stateful packet inspection, intrusion detection and protection, Layer 7 app awareness, encrypted traffic, threat intelligence, identity and access management, statistics and cloud-based management.
| Vendor | Product | Standalone FWaaS | Part of SASE | IPS/IDS | URL Filtering | App Control | DLP | UK PoPs | Indicative Cost / User / Month |
|---|---|---|---|---|---|---|---|---|---|
| Zscaler | Zscaler Cloud Firewall | ✓ | ✓ (ZIA) | ✓ | ✓ | ✓ | ✓ | Yes | Included in ZIA bundle |
| Fortinet | FortiSASE FWaaS | ✓ | ✓ (FortiSASE) | ✓ | ✓ | ✓ | ✓ | Yes | £8–£15 |
| Palo Alto Networks | Prisma Access FWaaS | ✓ | ✓ (Prisma Access) | ✓ | ✓ | ✓ | ✓ | Yes | £10–£20 |
| Cato Networks | Cato FWaaS | ✓ | ✓ (Cato SASE) | ✓ | ✓ | ✓ | ✓ | Yes | Included in Cato bundle |
| Versa Networks | Versa SASE FWaaS | ✓ | ✓ (Versa SASE) | ✓ | ✓ | ✓ | ✓ | Yes | £7–£14 |
| Cisco | Cisco+ Secure Connect FWaaS | Partial | ✓ (Cisco+ SASE) | ✓ | ✓ | ✓ | Partial | Yes | £9–£18 |
| Check Point | CloudGuard Network Security | ✓ | ✓ (Harmony SASE) | ✓ | ✓ | ✓ | ✓ | Yes | £8–£16 |
| Open Systems | Open Systems FWaaS | ✓ | ✓ (Enterprise+ SASE) | ✓ | ✓ | ✓ | Partial | Yes | Contact vendor |
Cato Networks
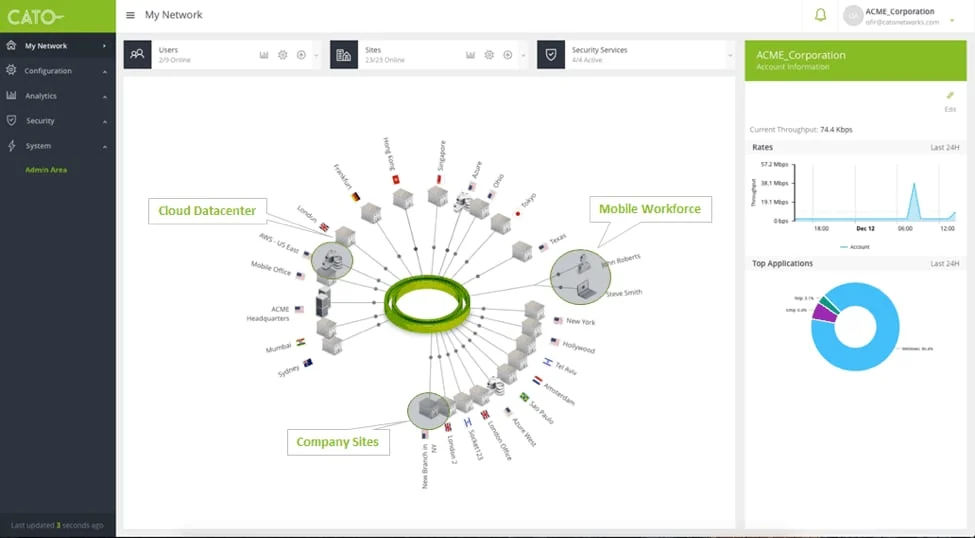
Founded in 2015, Cato Networks was one of the first cloud-native network security companies that sought to solve "network security complexity, which opens up organisations to attacks as hackers can slip through the cracks of misconfigurations and software vulnerabilities by moving software-defined network and security controls to the cloud." The intervening years have seen its technology mature into the Cato SASE cloud, which uses globally distributed POPs and private backbone to onboard traffic to Cato's converged network and security system.
Cato’s NGFW is integrated with its SASE suite and provides a single, logical, globally distributed firewall with a unified application-aware security policy. It provides the standard features of a conventional hardware firewall, including:
- Stateful DPI and ACL filtering including rules based on network entities, time restrictions, and type of traffic. The DPI engine can classify applications or services by their headers without having to decrypt the payload.
- L7 application awareness with a complete list of signatures and parsers to identify common applications that can be extended with custom application definitions identified by port, IP address or domain.
- URL filtering
- Managed signature database updates as Cato evaluates emerging threats and develops and tests firewall rules to stop them.
- An Event Discovery feature that organises more than 100 network and security events into a single, queryable timeline.
- Event and traffic analytics
Open Systems
Open Systems firewall is available as a standalone product, but typically sold as part of its Enterprise and Enterprise+ SASE services. The firewall segments traffic into different security zones across the network to facilitate consistent policies worldwide. It also supports site-specific ACLs for more granular control of particular applications or users. In a typical implementation, IT would define global policies for each security zone — for example, remote worker WAN, data centre LAN, production cloud, public Internet, SaaS Internet — with local firewall rules and zones/network segments to accommodate particular security requirements. Open Systems' firewall also includes typical NGFW features, including L7 packet inspection and application identification including the ability to filter SaaS applications by IP protocol, port and address.
Palo Alto
Palo Alto Prisma Access consolidates its networking and security capabilities, including FWaaS, into a single cloud-delivered SASE platform. The FWaaS includes all the features of its successful Next-Generation Firewalls (NGFWs), including:
- A single-pass inspection architecture
- L3-7 packet inspection and URL filtering with TLS support and IPS.
- User authentication and access control with a proprietary User-ID technology that uniquely identifies users across locations, regardless of their device type or OS.
- MFA (multi-factor authentication) for any application, including those built without innate MFA support, with integrations for popular IAM services such as Duo, Okta, Ping Identity and RSA.
- The Wildfire shared threat intelligence system with AI-based zero-day prevention to automatically block unknown threats and malware.
- DNS security with ML-based predictive analytics to block DNS-based attacks.
- Log aggregation data lake and reporting.
Palo Alto has more than 100 POPs in 77 countries and promises five-nines availability per month (26 seconds of down time).
Versa
Like all of the vendors in this list, Versa incorporates a FWaaS into a comprehensive SASE product that can be internally deployed in a data centre (self-managed), hosted by a service provider, delivered as a Versa-managed cloud service or as a hybrid combination of internal and managed services. Its VOS software supports multiple tenants and uses a single-pass architecture that parallelises packet processing and security components to improve performance and scalability. Versa's NGFW has a similar feature set to the other firewalls in this article, namely:
- L3-L7 SPI with zone-based protection with standard address-port ACLs and rules based on geo-location or the time-of-day.
- Application awareness and filtering with built-in rules for more than 3000 applications and protocols.
- URL categorisation and filtering.
- IDS/IPS with default and custom signatures and profiles.
- Anti-virus scanning with automatic signature updates and support for more than 35 file types.
- DDoS protection.
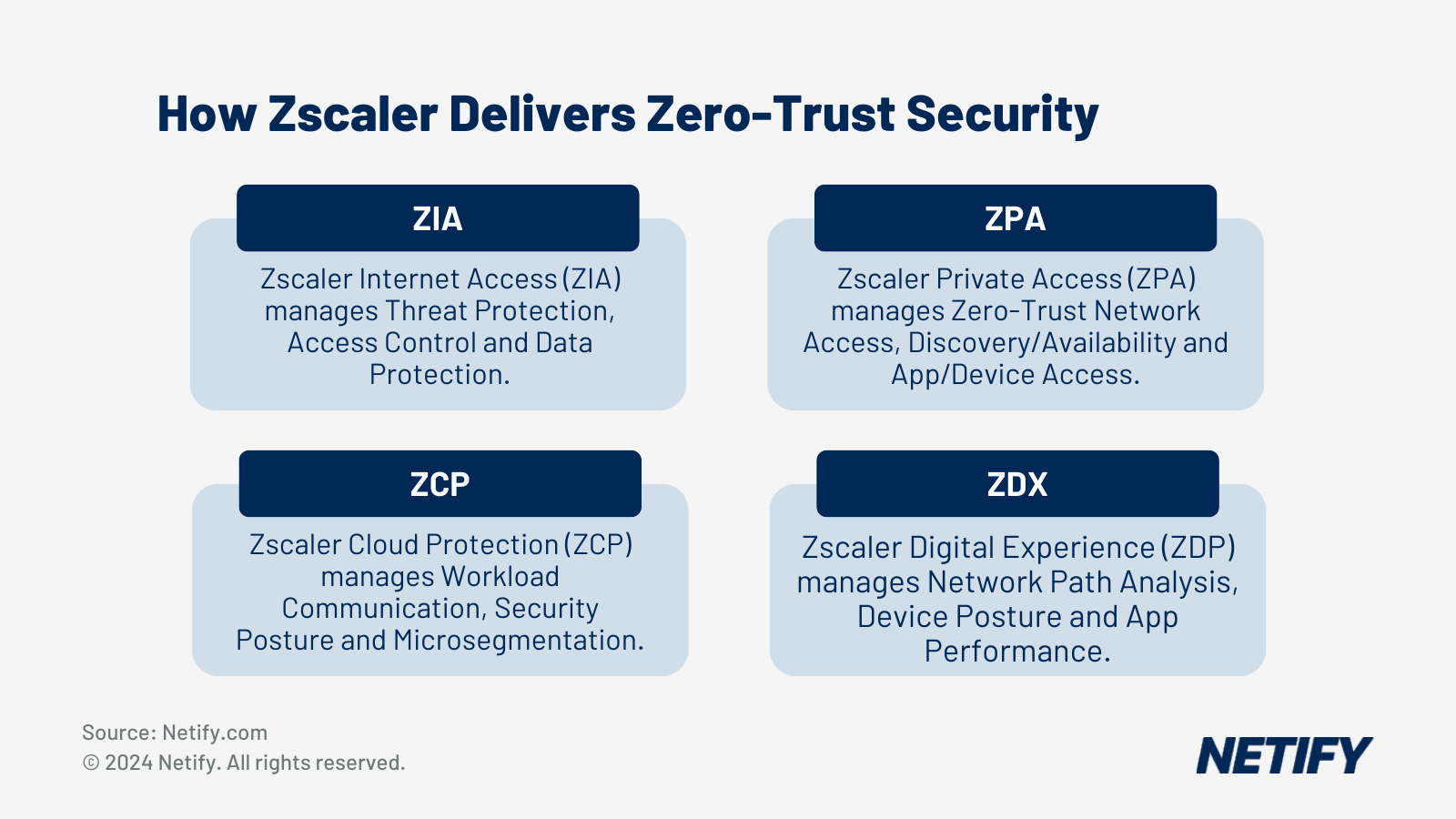
Zscaler
Zscaler's Zero Trust Exchange is a four-pronged cloud-based approach to user, application and cloud security that uses FWaaS in several areas and allows contextual information to be shared between the firewall and other security services. Zscaler runs on 150 data centres around the world that process more than 160 billion transactions per day. Like all FWaaS products, Zscaler uses a unified, distributed control plane that provides policy consistency across all firewall instances. The Zscaler Cloud Firewall feature set is consistent with its competitors in this article and includes:
- Standard IP, port and domain name policies (aka ACLs).
- DPI with TLS support.
- Integrated IPS.
- DNS security and control that can block malicious domains, detect and prevent DNS tunnelling, and enable policies based on user, app, and geo-location.
- Log aggregation of data from all firewall instances with analytics to predict trends, expose anomalous behaviour and facilitate troubleshooting.
- Managed threat database that identifies new exploits from the billions of pooled requests in the Zscaler cloud and automatically updates blocking policies for all customers.
Trends and recommendations
The market for FWaaS is expanding rapidly, with Gartner projecting that the SASE sector will grow at a compound annual growth rate of approximately 26% through 2028. This growth is driven by the urgent need for organisations to modernise their security infrastructure to keep pace with digital transformation. Many enterprises are currently reaching the end of a hardware lifecycle for firewalls purchased before 2022, and are choosing to move to cloud-delivered services rather than refreshing their physical appliances.
AI-native threat detection has become a primary differentiator in the 2026 market. Vendors are moving beyond simple signature-based detection to models that use machine learning to analyse behavioural patterns in real time. This allows the system to identify new and unknown threats based on how traffic behaves, rather than waiting for a known attack signature to be identified. When evaluating vendors, organisations should ask for details on how these detection models are trained and how quickly updates are pushed to the network edge.
The alignment of FWaaS with zero trust principles is another critical trend. By pairing firewall capabilities with ZTNA, organisations can create a security model that is aware of both the identity of the user and the context of the connection. This ensures that access is only granted to the specific resources a user needs, rather than providing broad access to a network segment. This approach is essential for securing a hybrid workforce where users are connecting from varied locations and devices.
When selecting a FWaaS provider, organisations should prioritise PoP coverage in the regions where their employees and offices are located. Low latency is vital for maintaining a good user experience, especially for real-time applications. The depth of SASE integration and the quality of the management console will determine how much operational overhead is truly reduced. A solution that fits the organisation’s current user count while providing a clear path for growth will offer the best long-term value.

Robert Sturt is a leading expert in SD-WAN and enterprise network solutions with extensive experience in telecommunications and network infrastructure. As a Forbes Business Council member and contributor to TechTarget, he provides strategic insights on network transformation and digital connectivity solutions. His expertise spans SD-WAN implementation, network security, and enterprise digital transformation initiatives.
Fact-checked by: Harry Yelland - Cybersecurity Writer, Netify
Frequently Asked Questions
What is Firewall-as-a-Service (FWaaS)?
FWaaS delivers next-generation firewall capabilities from the cloud instead of on-premise hardware. It inspects traffic at cloud PoPs and applies security policies without requiring physical firewall appliances at each location. This allows organisations to enforce consistent security policies across all sites, remote users, and cloud environments from a single management console.
Is FWaaS part of SASE?
Yes. FWaaS is one of the five core components of SASE alongside SD-WAN, SWG, CASB, and ZTNA.
How much does FWaaS cost in the UK?
UK pricing for FWaaS varies considerably by vendor and the scope of the SASE bundle it is sold within. Where FWaaS is priced as a standalone service, indicative costs range from approximately £7 to £20 per user per month depending on the vendor, feature tier, and contract volume. For vendors such as Zscaler and Cato Networks, FWaaS is included within the SASE subscription and is not priced separately. Organisations should request a formal quote for accurate pricing based on their specific user count and requirements.
Who are the best FWaaS providers?
The leading FWaaS providers for UK and enterprise deployments are Zscaler, Palo Alto Networks, Cato Networks, and Fortinet.
Zscaler is widely regarded as the category leader in cloud-native SASE with FWaaS included in its ZIA platform.
Palo Alto Prisma Access delivers a comprehensive NGFW feature set with strong threat intelligence through the WildFire platform.
Cato Networks is a strong choice for organisations wanting a fully converged SASE with simple pricing.
Fortinet FortiSASE is particularly relevant for organisations already invested in the Fortinet ecosystem.