SASE Solutions Supporting Legacy Financial Application Protocols
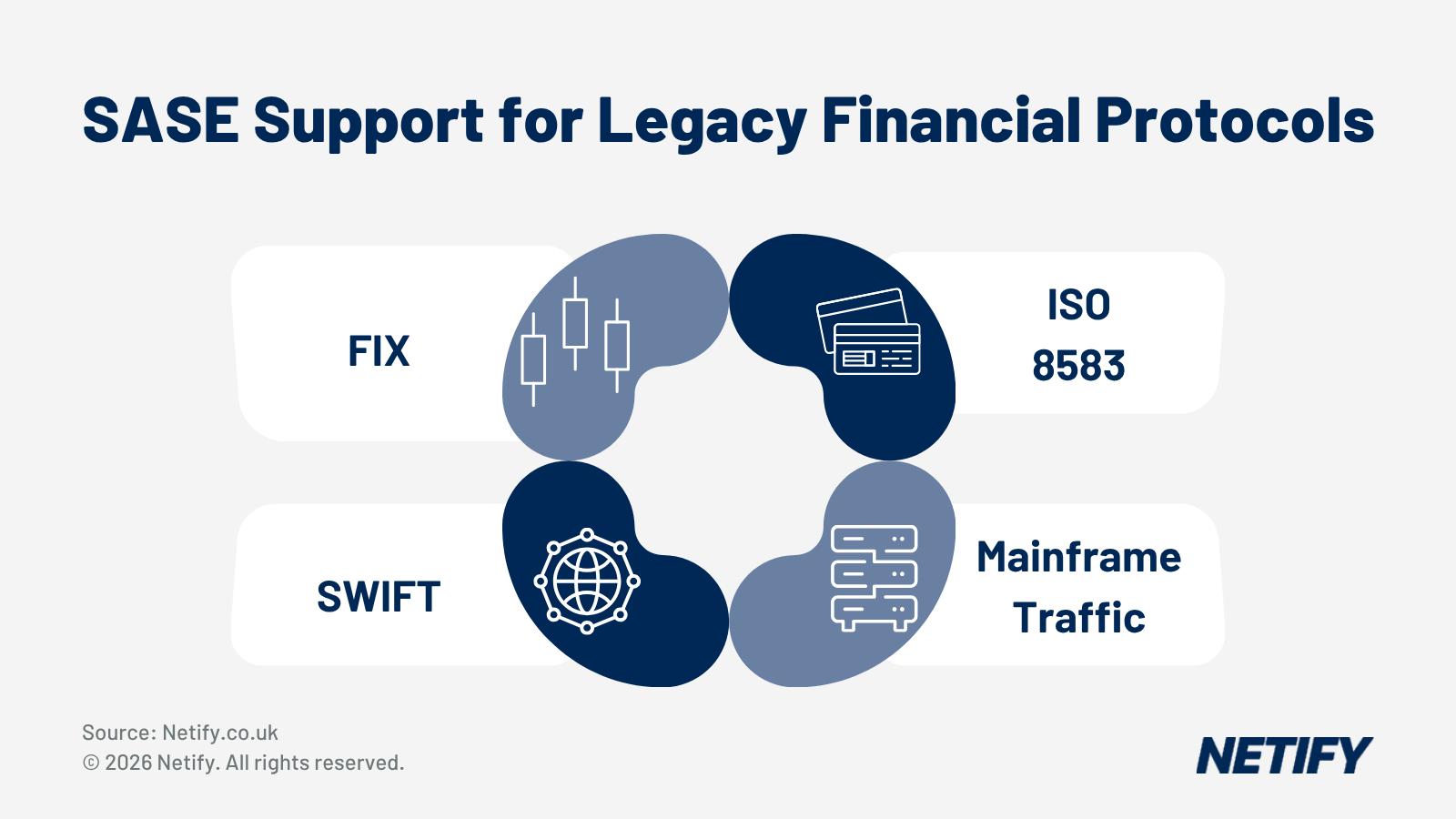
According to Dell'Oro Group, the global SASE market grew 21 per cent year-on-year in Q3 2025 to nearly $3 billion in quarterly revenue, whilst spending on legacy access routers fell by 25 per cent over the same period - representing a shift that shows that network teams are actively replacing their hardware (that has traditionally carried FIX, SWIFT, ISO 8583 and mainframe traffic). At the same time though, industry data continues to show that the majority of large enterprises still depend on mainframes for critical workloads, with many of the largest users maintaining or increasing mainframe capacity rather than shrinking it. Further to this, since January 2025, the Digital Operational Resilience Act (DORA) has applied across the European Union, whilst NIS2 and national frameworks such as the FCA's operational resilience regime in the UK are tightening expectations around secure, resilient network connectivity for critical systems and these regulations push firms towards modern, observable, policy-driven networks without granting any tolerance for downtime on the likes of payment, trading or core banking applications.
SASE is therefore not simply a way to optimise SaaS and remote access, it has to carry and protect legacy financial protocols with the same or better service levels than MPLS, leased lines and mainframe gateways.
In this article, we'll cover how SASE can assist with key legacy financial protocols, focusing on how traffic is classified, routed, secured and monitored, as well as providing a practical, protocol-level view of what to ask SASE vendors and how to plan migrations without putting critical transaction flows at risk.
For teams planning or running RFPs, Netify's SASE and SD-WAN RFP builder tools provide a structured way to embed these protocol-level requirements into vendor comparison frameworks.
Legacy Financial Protocols Still In Production
The following protocols remain widely used across banks, payment processors and trading, each with their own transport characteristics that need to be considered when moving from private WAN and mainframe-centric networks to SASE overlays.
| Protocol | Function | Transport | Typical ports | Latency sensitivity | Encryption | Status 2026 |
|---|---|---|---|---|---|---|
| FIX (5.0 SP2) | Electronic trading | TCP | 9878 / custom | Ultra-high | TLS optional | Active |
| SWIFTNet (FIN) | Interbank messaging | TCP/IP (managed) | Proprietary | Moderate | SWIFT PKI | Active |
| ISO 8583 | Card payment | TCP | Custom (varies) | High | TLS / VPN | Active |
| TN3270 / TN5250 | Mainframe / terminal | TCP (Telnet) | 23, 992 (TLS) | Low to moderate | TLS optional | Active |
| SNA / APPN | Legacy mainframe | SNA over IP | TCP 2065, UDP | Moderate | None native | Declining |
| AS2 | EDI document transfer | HTTP/S | 80, 443 | Low | S/MIME | Active |
| IBM MQ | Application messaging | TCP | 1414 | Moderate to high | TLS | Active |
| EBICS | Corporate-to-bank | HTTPS | 443 | Low | TLS & XML sig | Active |
Legacy Financial Protocols in Depth
FIX (Financial Information eXchange) is the standard for electronic trading between buy-side, sell-side and exchanges, used for order submission, execution reports and market data. It runs over TCP and, for the most latency-sensitive environments, often over dedicated private lines where congestion and packet loss are tightly controlled. FIX persists because the ecosystem of trading venues and counterparties is deeply integrated around it, with no single replacement protocol offering comparable usage, tooling or regulatory acceptance. From a network perspective, FIX flows are long-lived TCP sessions with strict jitter and loss tolerances, sensitive to packet reordering and to any buffering or encryption step that introduces additional latency.
How SASE Platforms Handle Legacy Protocol Traffic
Some of the key benefits of SASE are application-aware routing, DPI limitations, ZTNA models, loss-mitigation techniques and encryption - all of which can be applied for traffic under regulatory constraints.
Application-Aware Routing and SLA Enforcement
One of the core features of SD-WAN (and SASE) overlays is Application-Aware routing, a combination of dynamic path selection and link aggregation for traffic steering based on loss, latency and jitter across tunnels using mechanisms such as Bidirectional Forwarding Detection (BFD) to ensure that traffic takes the path that best matches defined SLA thresholds.
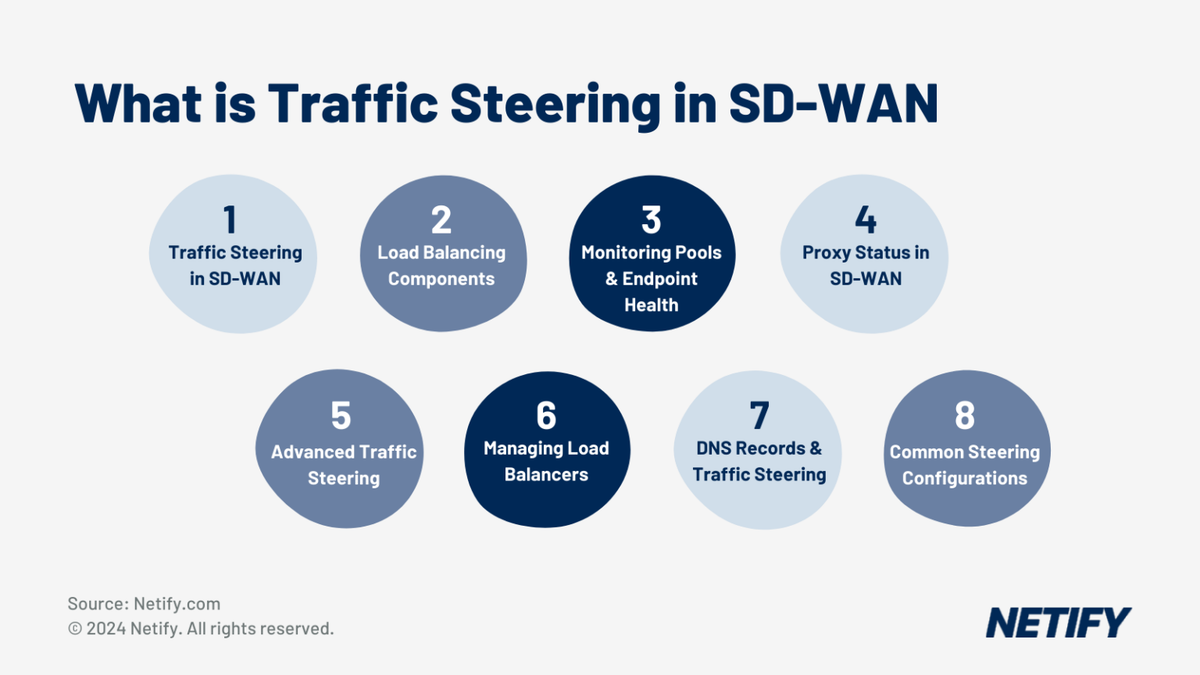
Further Reading: How Traffic Steering Works
The challenge is that most SD-WAN and SASE platforms ship with signature libraries focused on SaaS applications, web protocols, VoIP and common enterprise services - rather than focusing on financial protocols (FIX, ISO 8583, EBICS and MQ).
Financial institutions must therefore consider financially-focused solutions or define custom signatures based on TCP ports, IP ranges and where possible, protocol fingerprints. Once these are in place, SASE policies can ensure that trading and card traffic remains on low-latency paths whilst less sensitive flows (such as AS2 and EBICS) use higher-latency links or internet breakouts.
Deep Packet Inspection Limitations
DPI engines in SASE are typically optimised for HTTP/HTTPS, SaaS and widely deployed enterprise protocols - meaning that legacy financial protocols often require proprietary framing, non-standard headers and encryption schemes that DPI engines do not recognise. Even where signatures exist, they may only identify a fraction of deployments, particularly where organisations customise ports or wrap traffic inside VPN tunnels.
Where legacy traffic is encrypted at the application layer, DPI visibility is limited to IP and port metadata unless TLS inspection is enabled, however, many financial flows use certificates and strict trust stores (or have compliance requirements) that prevent decryption by intermediate proxies (this is particularly true for SWIFT connections and card scheme links). As a result, SASE deployments in financial services must rely on metadata-based classification and routing whilst ensuring that security policies still meet regulatory expectations.
ZTNA and Legacy Protocols
Zero Trust Network Access in most SASE platforms is designed first for web and cloud applications, rather than legacy financial protocols. Without a HTTP-centric approach, ZTNA is more difficult to implement due to the reliance on custom clients and long-lived TCP sessions. To support these, SASE vendors often expose Layer 3 and Layer 4 ZTNA capabilities that control access based on IP addresses, ports and identities tied to device agents rather than browser sessions. Furthermore, some SASE offerings add clientless or proxy-based access modes that can encapsulate TCP connections, presenting them through a cloud access point.
Whilst this extends zero-trust controls to legacy protocols, it introduces additional hops and potential latency, and it must be tested carefully for session persistence. We'd recommend that network administrators verify how ZTNA components handle reconnects, failovers and idle timeouts for the likes of TN3270 or MQ sessions, which may be open for many hours at a time.
Forward Error Correction and Packet Replication
Protocols such as FIX and ISO 8583 are extremely sensitive to packet loss and retransmission delays, therefore SD-WAN features such as packet duplication and forward error correction (FEC) can be rather beneficial by addressing this through sending multiple copies of key packets across different links or by transmitting redundant information that allows lost packets to be reconstructed without TCP retransmission.
By duplicating FIX packets over two independent underlays, the SD-WAN fabric can mask brief loss spikes or micro-outages on one circuit, ensuring that orders reach the exchange without retransmission delay. For ISO 8583, FEC can prevent timeouts that would otherwise cause authorisation declines at the point of sale, though it's worth noting that these techniques consume additional bandwidth, so they are typically reserved for the most critical workflows.
Encryption and Compliance
SASE overlays almost always use IPsec or comparable schemes to encrypt traffic between edges and cloud enforcement points and this provides both confidentiality and integrity for legacy protocols that lack native encryption. From a regulatory perspective, this helps financial entities meet requirements such as DORA Article 11, which expects encryption of data in transit for critical services, as well as similar expectations from both NIS2 and FCA guidance.
However, double encryption can create performance challenges and when a protocol already uses TLS, adding an IPsec overlay introduces extra processing and potential path overhead, which can push latency beyond acceptable thresholds for FIX or ISO 8583 flows. Network administrators must therefore balance security and performance, potentially using hardware acceleration, local SASE enforcement points or selective relaxation of overlay encryption on trusted private circuits to mitigate this issue.

Deep Dive: What CyberSecurity Requirements does the Financial Services Sector Face?
Vendor Considerations for Legacy Protocol Support
SASE and SD-WAN platforms vary significantly in their ability to handle legacy financial protocols. This table offers a vendor-neutral checklist that network teams can adapt into RFP and RFI documents.
| Capability | Why it matters | RFP question |
|---|---|---|
| Custom application awareness | Standard DPI can miss proprietary protocols | Can you identify and prioritise FIX, ISO 8583, and SWIFTNet traffic natively? |
| Layer 3/4 ZTNA | Legacy protocols need network-layer access, not app proxies | Does your ZTNA support non-HTTP protocols including TN3270 and IBM MQ? |
| SLA class granularity | FIX, ISO 8583 need microsecond-aware queuing | How many SLA classes can be defined and what is the minimum latency guarantee? |
| Packet replay critical for FIX | Does the SD-WAN provide lossless failover for TCP sessions? | Does the SD-WAN provide lossless failover for TCP sessions? |
| TLS inspection | SWIFT, card networks require careful inspection scoping | Can specific traffic flows be excluded from TLS inspection? |
| On-premises sovereign | Some rooms do not allow cloud key management | Do you offer on-premises or private cloud deployment with local key management? |
| Session persistence | TN3270, FIX, IBM MQ require stateful long-lived connections | How are long-lived TCP sessions handled during path failover? |
| Sovereign and compliance | DORA, NIS2, FCA require audit trails and data residency | Can inspection logs be stored on-premises and scoped by regulation? |
Each of these capabilities directly affects how safely and effectively a SASE platform can carry legacy protocol traffic. For example, limited data residency controls may prevent you from routing SWIFT-related monitoring data through certain regions, creating obstacles during regulatory reviews.
When engaging vendors, network teams should ask for protocol-specific reference architectures (including configurations for FIX, SWIFTNet, ISO 8583 and mainframe access). For this, many providers have internal best-practice guides that can often be shared (under NDA) and these documents can help to explain whether the platform has genuinely been tested with legacy financial workloads and if it's a suitable fit for your use case.

Explained: Netify's Guide on How to Deal with Compliance for Financial Services
Migration approach for legacy protocols onto SASE
Moving legacy financial protocols onto a SASE platform is ideally done as a phased programme rather than a complete switch-over. Given this, we've detailed our four phased approach below to provide you with a practical framework.
Phase 1: Discovery and Classification
We'd first recommend that you build a complete picture of existing legacy protocol flows (including source and destination addresses, ports and current paths). For each flow, document key attributes:
- Typical and peak bandwidth
- Latency budgets
- Encryption status
- Session duration
- Regulatory constraints
Map which transport types are currently in use, including MPLS, private leased lines, data centre cross-connects and internet VPNs. This allows you to segment flows by criticality and by suitability for early migration.
Phase 2: SD-WAN Underlay Preparation
With a clear inventory, deploy SD-WAN edges alongside existing routers in a parallel-run model, integrating SD-WAN overlays with underlay circuits and validating reachability.
For each legacy protocol, create custom application signatures based on the discovery data, then define SLA classes in line with the tolerances identified:
- Loss thresholds
- Latency ceilings
- Jitter limits
You should then test application-aware routing using lab or non-production traffic, simulating link failures, brownouts and congestion to tune failover thresholds and path-selection policies. We'd also recommend validating packet replication and FEC settings for flows that will later carry FIX or ISO 8583 in production.
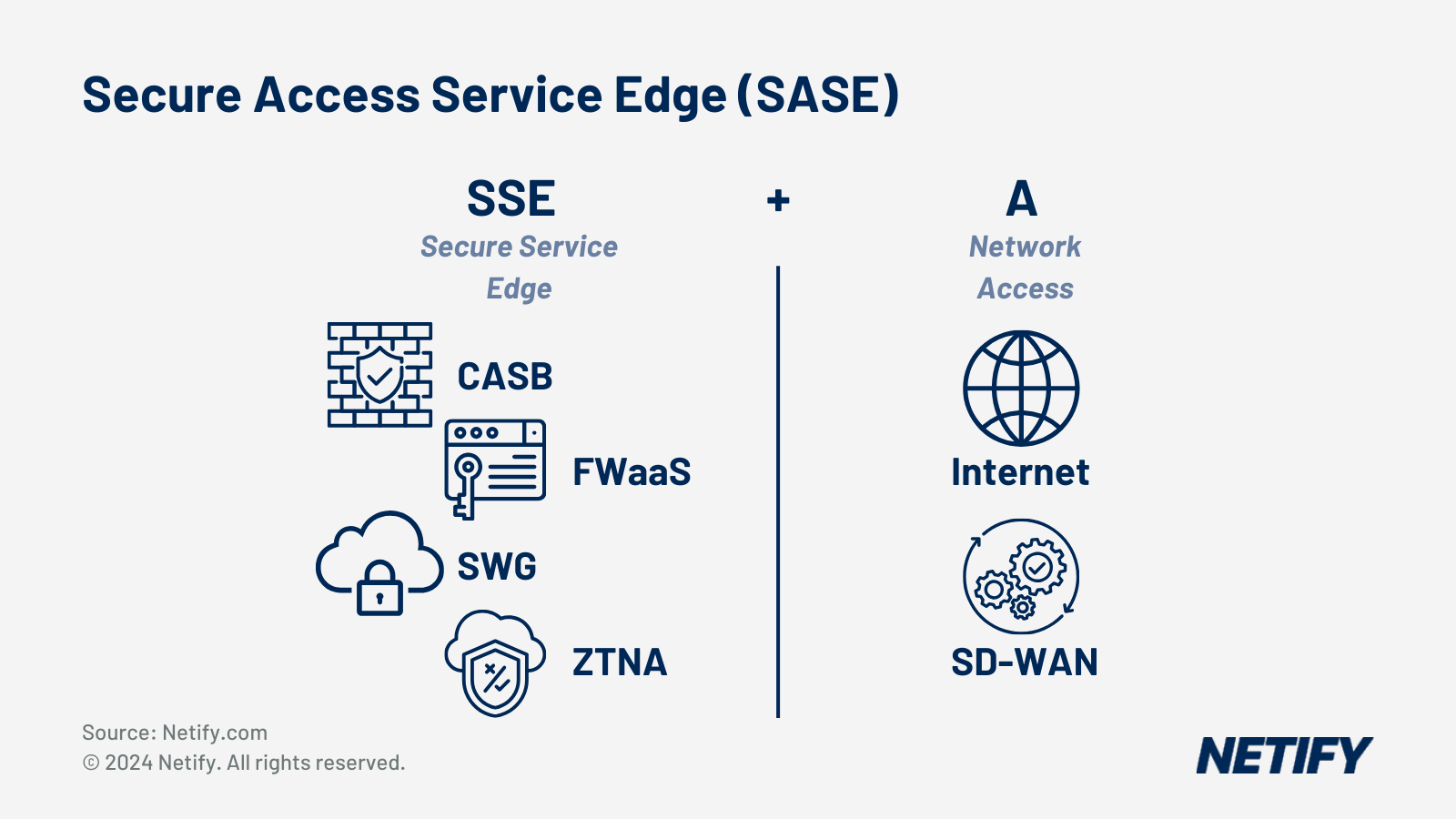
Phase 3: Security Service Onboarding
Once the SD-WAN fabric is stable, begin enabling SASE security services. A common pattern is to start with the following for internet-bound and SaaS traffic, keeping legacy financial protocols on existing paths during early stages:
- Secure Web Gateway (SWG)
- Cloud Access Security Broker (CASB)
- Firewall-as-a-Service (FWaaS)
This builds confidence in the cloud enforcement model without putting critical protocols at risk.
As familiarity grows, add Layer 3/4 ZTNA controls for legacy protocol access, using device and user identity to restrict which endpoints can initiate TN3270, MQ, or FIX connections.
You should then configure TLS inspection bypass lists for flows that must not be decrypted (such as SWIFT connections and card scheme links) and validate that overlay encryption does not breach latency thresholds for time-sensitive flows (using synthetic tests).
Phase 4: MPLS Offload and Optimisation
The final phase shifts legacy protocol traffic from MPLS and private circuits onto the SASE overlay, starting with the least sensitive flows. We'd recommend the following to be the first you migrate:
- AS2 and EBICS traffic (batch-oriented and latency-tolerant, provided that S/MIME and TLS requirements are met)
- TN3270/TN5250 and MQ once early migrations are stable
- ISO 8583, then FIX as the final workloads, retaining MPLS as a backup throughout
For the most critical flows, enable packet replication or FEC and verify behaviour under real-world conditions, including partial outages and brownouts. You should monitor performance and error rates closely, correlating them with SASE and SD-WAN telemetry to fine-tune policies. Only once all stakeholders agree that performance, stability and compliance obligations are fully met, should you consider decommissioning legacy access routers and circuits for those protocols.
Conclusion
SASE in financial services is often considered primarily in terms of compliance checklists, zero-trust maturity models and enabling remote access, however often don't consider legacy protocols (such as FIX, SWIFTNet, ISO 8583, TN3270, SNA, AS2, MQ and EBICS).
By tailoring your SASE RFI to insist on the capabilities outlined in this article, you can align modern, cloud-centric network security with these much older application stacks, whilst also still satisfying regulatory needs for DORA, NIS2 and FCA.
For teams planning or running RFPs, Netify's SASE and SD-WAN RFP builder tools provide a structured way to embed these protocol-level requirements into vendor comparison frameworks.

Harry holds a BSc (Hons) in Computer Science from the University of East Anglia and is ISC2 Certified in Cybersecurity (CC). He serves as a Cybersecurity Writer here at Netify, where he specialises in enterprise networking technologies. With expertise in Software-Defined Wide Area Networks (SD-WAN) and Secure Access Service Edge (SASE) architectures, Harry provides in-depth analysis of leading vendors and network solutions.
Fact checked by: Robert Sturt - Managing Director, Netify
Frequently Asked Questions
Can SASE fully replace MPLS for legacy financial protocol traffic?
In most cases, yes, but not immediately and not without careful preparation. MPLS provides deterministic routing, strict SLAs, and no shared-medium contention. Modern SD-WAN overlays can match or exceed those characteristics for many workloads using BFD-based path monitoring, SLA class steering, and packet replication across dual underlays. The challenge is that legacy financial protocols such as FIX and ISO 8583 have very tight latency and loss budgets that leave little room for error during the transition. A phased approach that keeps MPLS as a fallback while progressively migrating lower-sensitivity flows is the safest route. Full replacement of MPLS for the highest-criticality flows such as FIX and SWIFTNet is achievable, but it requires thorough testing and performance validation under real-world conditions before cutover.
Does DORA require financial institutions to encrypt all legacy protocol traffic?
DORA Article 11 sets expectations around encryption of data in transit for critical ICT services, and the associated regulatory technical standards reinforce the principle that all sensitive data exchanged across networks should be protected. In practice, this means that legacy protocols which transmit data in plain text, such as unencrypted TN3270 or SNA, need to be wrapped in a secure transport layer. SASE overlays using IPsec can satisfy this requirement without changing the application itself. For protocols that already use application-layer encryption, such as MQ over TLS or EBICS over HTTPS, the SASE overlay provides an additional network-level layer. Firms should document their encryption approach for each protocol flow as part of their ICT risk management framework and be prepared to demonstrate this to regulators on request.
Why can't SASE simply use TLS inspection to gain visibility into legacy financial traffic?
TLS inspection works by acting as a man-in-the-middle, decrypting traffic, inspecting the payload, and re-encrypting it before forwarding. For many web and SaaS applications this is acceptable, but several legacy financial protocols explicitly prevent it. SWIFTNet connections use SWIFT's own PKI with certificate pinning, meaning that any attempt to substitute the certificate during inspection causes the connection to fail. Card scheme links frequently have similar restrictions. Beyond technical constraints, there are regulatory and contractual reasons to avoid inspection of these flows: SWIFT's Customer Security Programme (CSP) and card network security standards impose strict controls on how traffic may be handled. The practical approach is to configure explicit TLS inspection bypass rules for these flows, classify them using IP, port, and certificate metadata instead, and apply compensating controls such as strict access policies and network segmentation.
How does ZTNA work for a FIX trading session or a TN3270 mainframe connection?
Traditional ZTNA was designed for web applications accessed through a browser, where identity is checked at the application layer before a session is established. FIX and TN3270 do not work this way; they rely on custom clients, fixed TCP connections, and session persistence that HTTP-centric access proxies can disrupt. To support these protocols, SASE platforms expose Layer 3 and Layer 4 ZTNA modes, where access control is enforced based on the identity of the device or user making the connection, tied to an agent running on the endpoint. The agent verifies identity and device posture before the network-level TCP connection is permitted to reach the target server. This means only authorised and healthy devices can initiate FIX sessions to a trading engine or TN3270 sessions to a mainframe, without any HTTP proxy in the path. The trade-off is that this approach provides less granular application-layer inspection than Layer 7 ZTNA, so it needs to be complemented by strong network segmentation and logging.
What happens to a long-lived TCP session if the SASE overlay path fails mid-session?
This is one of the most operationally significant questions for financial services SASE deployments. Protocols such as TN3270, IBM MQ, and FIX maintain TCP sessions that may run for hours or even days. If the SD-WAN fabric performs a failover to a secondary path, the behaviour depends on how the platform handles stateful session continuity. Some SD-WAN solutions perform hitless failover by maintaining a shared session state across tunnels, allowing the TCP connection to survive a path change transparently. Others perform a hard failover that resets the TCP session, forcing the application to reconnect. For trading systems and mainframe applications, a forced reconnect can cause significant disruption, and some applications have reconnect logic that is not designed for frequent re-establishment. When evaluating vendors, you should specifically ask for documented failover behaviour for stateful TCP sessions and request test evidence, not just marketing claims. The answer should include the failover time, whether sessions are preserved or reset, and how this changes under different failure scenarios such as link loss versus edge device failure.
Is it possible to apply quality of service prioritisation to FIX traffic over a shared internet underlay?
QoS markings such as DSCP can be applied within your own network and within the SD-WAN overlay tunnels, but once traffic exits onto the public internet those markings are typically ignored or overwritten by ISPs. This is one of the fundamental limitations of internet-based transport compared to MPLS, where QoS is honoured end-to-end. SD-WAN addresses this in two ways. First, by using multiple underlay circuits and intelligently steering FIX traffic to the circuit with the best current performance metrics rather than relying on QoS. Second, by using packet replication and FEC to compensate for loss rather than trying to prevent it through queuing. For the most latency-sensitive FIX environments, some organisations use dedicated low-latency internet or private connectivity options as the primary underlay for trading traffic, with the SD-WAN overlay providing the intelligence and failover capabilities. This preserves the performance characteristics of a private circuit while gaining the flexibility and cost benefits of SASE management.
How should we handle ISO 8583 traffic where the payment switch is hosted in a third-party data centre?
Third-party hosted payment switches are common in the acquiring and processing space, and they introduce a specific routing challenge: you need low-latency, reliable connectivity to an endpoint you do not control. The preferred approach is to use a SASE platform with a point of presence close to the third-party data centre, or to establish a private connect or cross-connect arrangement where available. The SD-WAN edge at your premises then steers ISO 8583 traffic to the nearest PoP using SLA-based routing, and the platform manages the last-mile path to the payment switch. Where PoP proximity is not possible, packet replication across dual internet paths can significantly reduce the effective packet loss rate seen by the application. You should also confirm with your payment switch provider whether they have specific network requirements or approved connectivity methods, as card scheme certification and PCI DSS compliance can impose constraints on how the connection is established and monitored.