What is the Gartner SD-WAN SASE security model?
The original framework was detailed in the Gartner report titled The Future of Network Security in the Cloud. This document recognised that users, devices, and applications are no longer contained within a physical office perimeter. Instead, the modern workforce is mobile and relies heavily on Software as a Service (SaaS) and Infrastructure as a Service (IaaS). SASE provides a path to secure these distributed environments without sacrificing network performance.
The convergence of networking and security into a single global service allows for simplified management. Rather than managing separate stacks for routing and threat protection, IT managers can apply unified policies. This transition is essential for organisations supporting hybrid work and global connectivity. The Gartner SASE model serves as the blueprint for this transformation.
The report recognised the shift in how Enterprise business requires a broad set of security technologies to deliver SD WAN access globally from wherever the user is located. The concepts outline the shift to a public cloud-first model where users are demanding access to SaaS and IaaS application resources from any location or device. As users become more mobile, hackers recognise the vulnerabilities which exist when users are no longer mostly based behind the corporate office Firewall. To meet the demands of remote network architecture with public SaaS and IaaS adoption, a comprehensive security stack is required.
Looking to build your SASE RFP? Why not give the Netify free SASE RFP builder a go today?
The Evolution of the SASE Architecture
When Gartner launched SASE in August 2019, the market was fragmented. Most vendors offered either networking or security, but rarely both in a unified manner. The initial adoption was slow, as organisations had to navigate complex legacy contracts and siloed internal teams. However, the shift toward remote work accelerated the demand for more agile architectures.
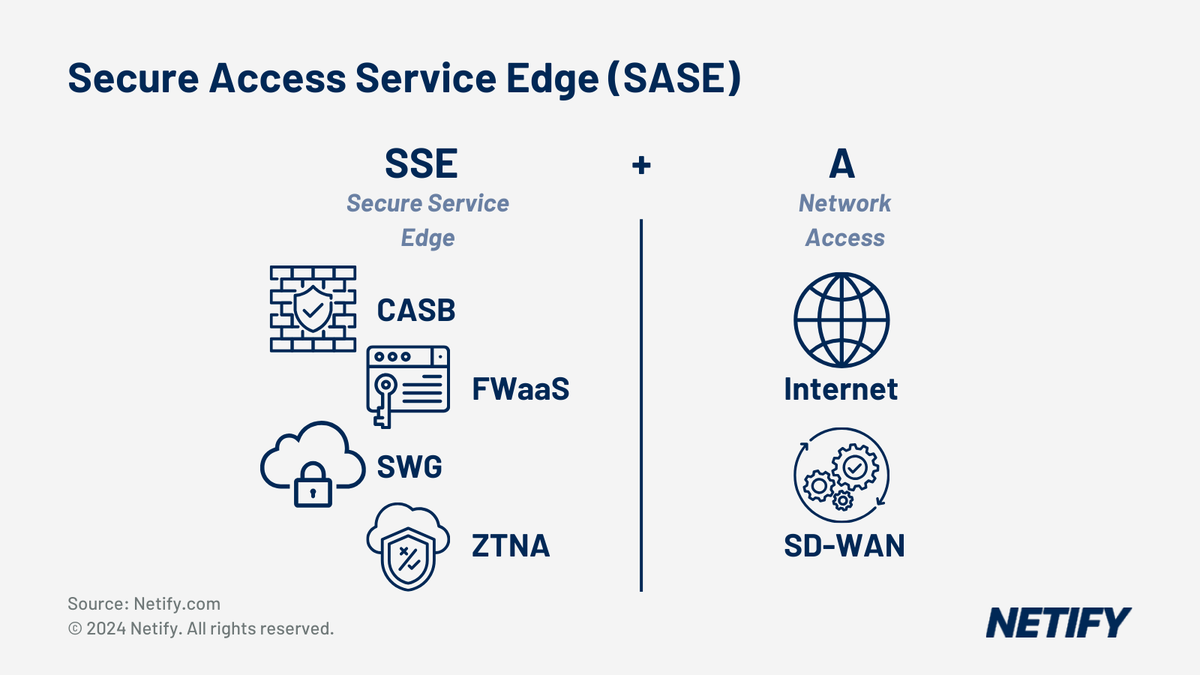
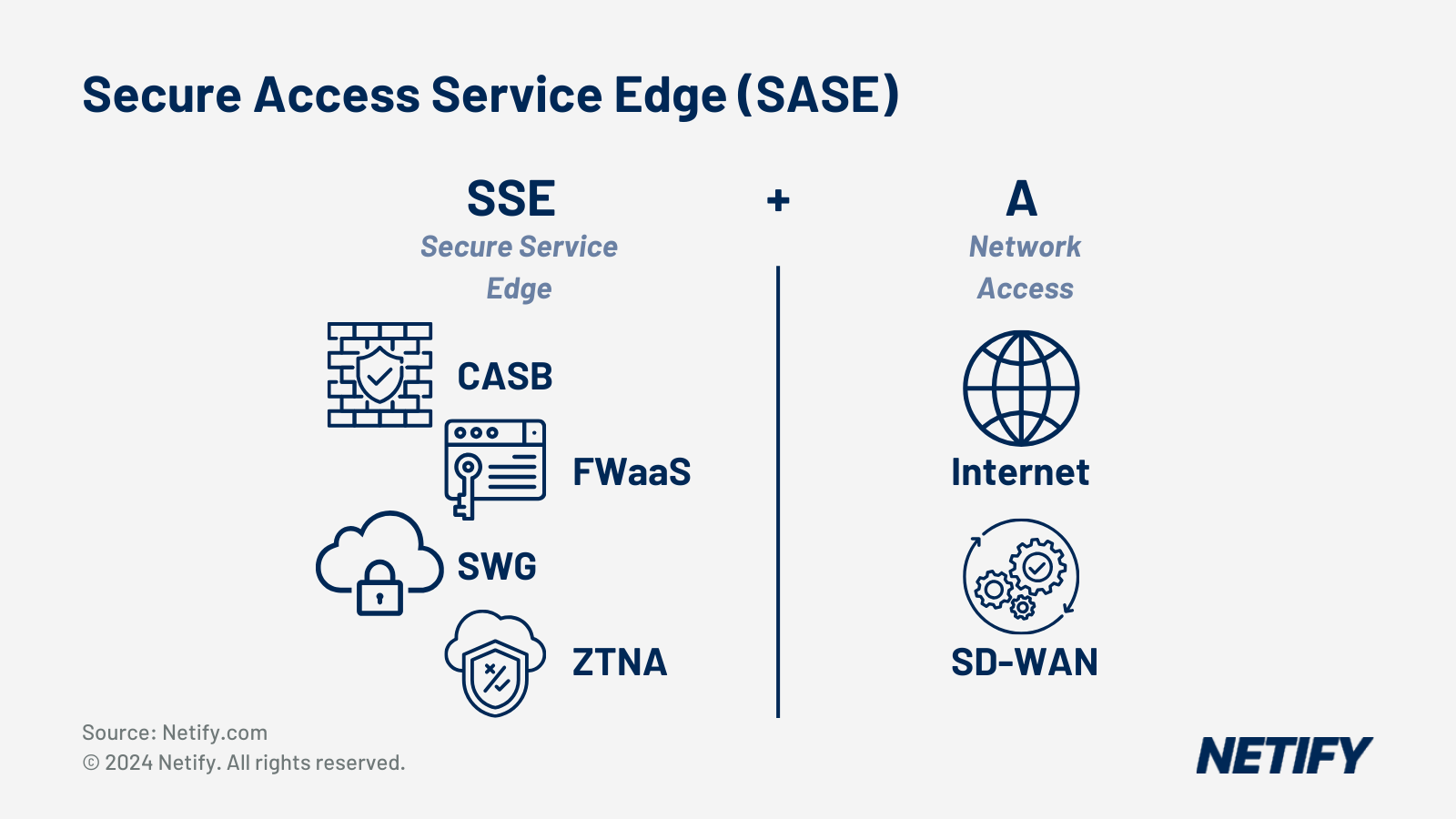
In 2021, Gartner introduced the Secure Service Edge (SSE) as a subset of the SASE framework. SSE focuses specifically on the security components required to protect web, cloud, and private application access. This allowed organisations to begin their SASE journey by modernising security even if they were not yet ready to replace their existing SD-WAN infrastructure. The introduction of SSE clarified the roadmap for technical architects.
By 2025, the market moved toward deeper integration. Gartner renamed the Single-Vendor SASE Magic Quadrant to the SASE Platforms Magic Quadrant. This change reflects the industry move toward unified platforms rather than stitched-together products. The focus is now on how well these services operate as a cohesive system.
While MPLS remains a component of good hybrid architecture, private VPN topology is no longer fit for purpose as users have de-centralized their network activity. In the main, reasons include:
- Network device intelligence is downloaded from pubic cloud security gateways in line with SDN concepts (Software Defined Networks).
- IT teams are being asked to save costs by replacing MPLS with DIA.
- Traffic no longer resides within private data centres with almost all organisations adopting some form of public Cloud from Office 365 to multiple bespoke SaaS and IaaS applications which reside in Azure, AWS or Google Cloud.
- BYOD (Bring your own device) and remote working mean there is no longer a network perimeter as access is practically everywhere.
- Maintaining application performance requires comprehensive reporting insights and features such as QoS (Quality of Service) and FEC (Forward Error Correction).
- Support of SD WAN is more straightforward but requires extensive conceptual knowledge.
- SD WAN works best with DIA (Direct Internet Access) requiring comprehensive and advanced security.
At Netify, we are witnessing fundamental changes across initial vendor comparison conversations due to the complete inversion of the legacy WAN architecture. IT teams are now faced with the challenge of how to deal with security threats on a real-time basis while maintaining consistent and reliable network access. The further challenge is to not only understand SASE concepts but also to evaluate implementation across each vendor. Reporting on false security positives are one example of how the Enterprise is challenged to maintain network uptime based on risks.
As businesses continue to adopt SASE, the market will mature into SDP (Software Defined Perimeter) from SD WAN. The concepts behind SDP are based around remote WAN connectivity which may originate from multiple user types across any connection from 4G/5G to Broadband and Ethernet DIA circuits.

The Five Core Components of SASE
A true SASE solution must include five primary technologies. These components work together to provide secure, high-performance connectivity to any resource.
SD-WAN
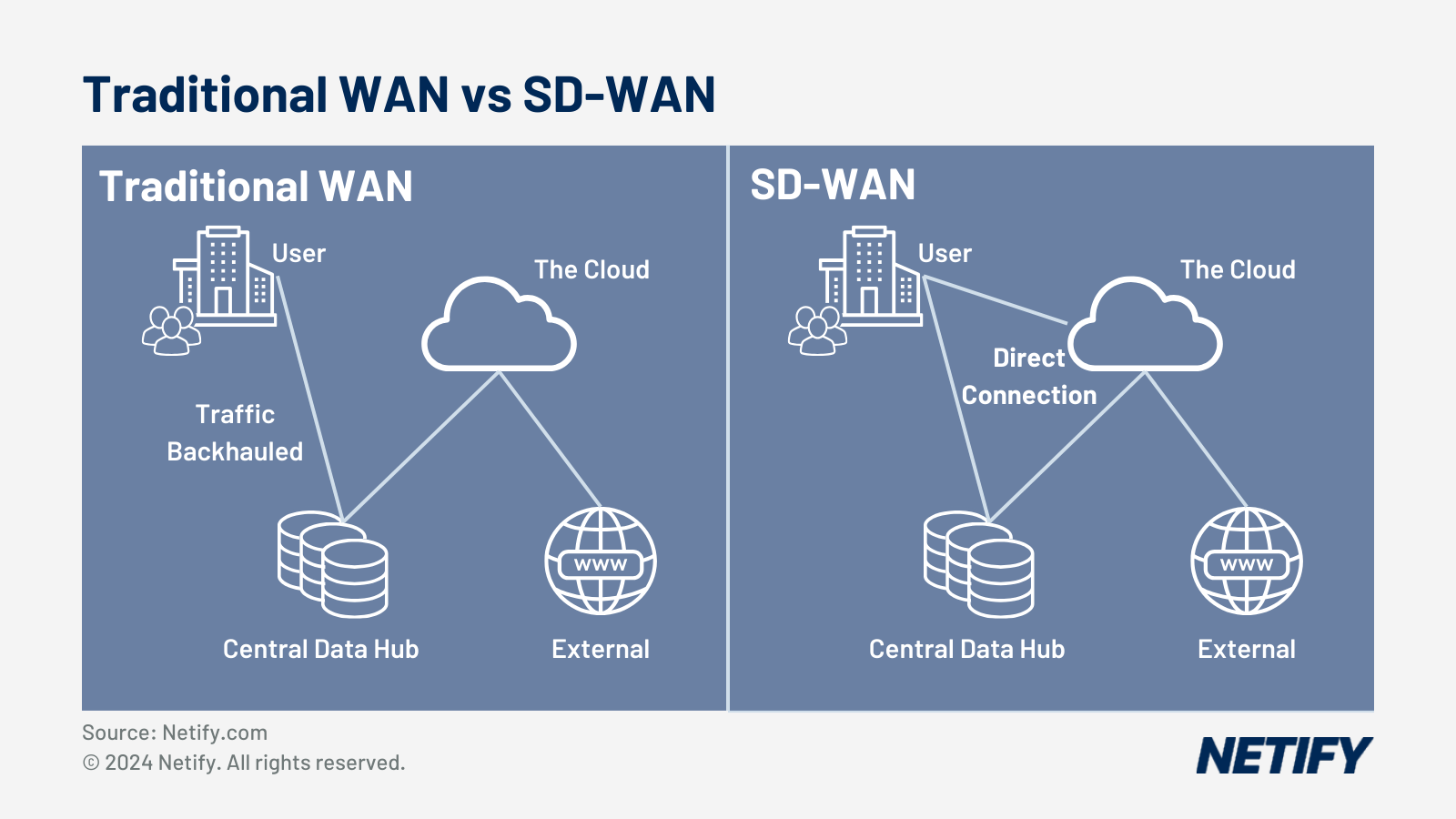
SD-WAN provides dynamic path selection and application-aware routing across multiple connection types. It forms the networking foundation of the SASE architecture. Without SD-WAN, the security components have no intelligent transport layer to work with.
Firewall-as-a-Service (FWaaS)
FWaaS moves traditional firewall functionality to the cloud. It ensures that security policies are consistent regardless of where the user is located. This allows UK mid-market organisations to scale their security without deploying expensive hardware at every branch.
Secure Web Gateway (SWG)
SWG protects users from web-based threats and enforces corporate acceptable use policies. It performs deep packet inspection and URL filtering in the cloud. This is critical for protecting remote employees who access the internet directly.
Cloud Access Security Broker (CASB)
CASB provides visibility and control over SaaS applications such as Microsoft 365 and Salesforce. It prevents data leakage and ensures that cloud accounts are not compromised. For organisations with a heavy cloud footprint, CASB is a vital layer of data protection.
Zero Trust Network Access (ZTNA)
ZTNA replaces traditional VPNs by providing secure access to internal applications based on identity and context. It operates on the principle of least privilege, meaning users only see the specific applications they are authorised to use. This significantly reduces the attack surface of the organisation.
Understanding Secure Service Edge (SSE)
Secure Service Edge (SSE) represents the security half of the SASE equation. It combines FWaaS, SWG, CASB, and ZTNA into a unified cloud service. Gartner introduced this category to help organisations that want to consolidate their security vendors separately from their networking providers. This approach is often preferred by security teams who want to maintain control over policy.
The first Gartner Magic Quadrant for SSE was published in February 2022. It provided a clear way to evaluate vendors based on their ability to deliver these four security services from the cloud. SSE is designed to secure the on-ramp to the internet and private applications. It ensures that every connection is inspected and authorised before traffic reaches its destination.
Organisations often adopt SSE when they have a functional SD-WAN but need to replace legacy security appliances. By moving these functions to an SSE provider, they reduce latency and improve the user experience. The convergence of these services into a single cloud edge is the primary goal of the SSE framework.
Architectural Benefits of SASE
The implementation of a SASE architecture provides several technical advantages. One of the most significant is the reduction in backhauling. In older models, internet traffic had to travel to a central data centre for inspection before reaching the web. SASE allows traffic to be inspected at the nearest cloud edge, which significantly reduces latency. This is particularly important for latency-sensitive applications such as video conferencing and VoIP.
Another benefit is the implementation of a Zero Trust posture. Unlike traditional networks that trust anyone inside the perimeter, SASE assumes no user is inherently safe. Every access request is verified based on identity, device health, and location. This granular control prevents lateral movement by attackers within the network. It ensures that a compromised device in a branch office cannot easily access sensitive data in the cloud.
The scalability of cloud-delivered security is also a major factor. As an organisation grows, it can add new sites and users without worrying about the capacity of physical firewall appliances. The SASE provider manages the underlying infrastructure, ensuring that security processing power scales automatically. This allows IT teams to focus on policy definition rather than hardware lifecycle management.
Why SASE is Essential for UK Enterprises
The UK business landscape is characterised by a high degree of digital transformation and hybrid work adoption. Many organisations have moved their primary workloads to Azure, AWS, or Google Cloud. In this environment, the traditional wide area network is no longer fit for purpose. SASE provides the modern architecture required to support these cloud-first initiatives.
Security is another major driver for SASE adoption in the UK. With the rise of sophisticated cyber threats, businesses need a security model that follows the user. SASE ensures that the same level of protection is applied whether a user is in a London office or working from home. This consistency is vital for maintaining compliance and protecting sensitive corporate data.
Finally, SASE helps organisations control costs by eliminating the need for expensive MPLS circuits and branch hardware. By leveraging the public internet and cloud-delivered security, businesses can build a more resilient network at a lower price point. The Gartner SASE model provides the framework to achieve these goals while maintaining high levels of security and performance.
What else is there to consider when buying SASE solutions?
While the SASE network security architecture model is fundamentally applied to any vendor supporting the technologies we have mentioned in this article (ZTNA, SWG, CASB, FWaaS), there are differences in their approach to management and delivery.
False positives remain one of the most frustrating aspects of security logs and statistics. These flags require IT teams to identify whether the threat (intrusion) is valid or has been created by an unknown aspect of a SaaS application. As with all aspects of complex telecoms, there are vendors leading the way with AI to and integration with 3rd party databases to combat this issue. The question is, how do you know if the vendors you are selecting are leading the field within the area of false positives.
The SASE Platforms Magic Quadrant in 2026
The 2026 SASE Platforms Magic Quadrant marks a significant milestone in the maturity of the market. This report evaluates vendors that can provide both the networking and the security components of SASE as a unified offering. Gartner has shifted its focus to the platform experience, looking for integrated management and shared data sets.
For UK enterprise organisations, a platform approach reduces the complexity of managing multiple vendors. It provides a single dashboard for both network performance and security threats. This visibility is crucial for troubleshooting issues in a distributed environment. The platform model also ensures that security policies can be automatically applied to new network branches.
Gartner's 2026 evaluation prioritises vendors that offer a consistent experience across all global points of presence. A high-quality SASE platform should deliver low-latency connections to major cloud providers. It must also demonstrate high availability and robust service level agreements. This ensures that the business remains productive and secure.
Convergence Trends and Projections
Gartner continues to refine its strategic roadmap for SASE convergence. One of the most significant projections involves the consolidation of networking and security buying decisions. By 2028, Gartner predicts that 30% of new SASE deployments will be consolidated into a single-vendor platform.
The shift toward consolidation is driven by the desire for operational efficiency. Managing separate SD-WAN and SSE vendors often leads to policy gaps and increased overhead. A single-vendor approach allows for single-pass inspection, where traffic is decrypted and analysed once for all security services. This reduces latency and improves application performance for the end user.
UK mid-market organisations are increasingly looking for managed SASE offerings. These services combine the technology platform with professional management and monitoring. This allows lean IT teams to focus on strategic initiatives rather than day-to-day firewall maintenance.
Conclusion
When evaluating SASE solutions, network architects must look beyond simple feature checklists. The quality of the vendor's global backbone is a critical factor. A provider with a large number of local points of presence in the UK and Europe will offer better performance for local users. Architects should also examine the depth of integration between the SD-WAN and security components. A truly unified platform should offer a single policy engine for both networking and security.
Interoperability with existing legacy systems is another important consideration. Most organisations cannot move to a full SASE model overnight. The chosen solution should support a phased migration, allowing legacy sites to coexist with new SASE-enabled locations. This ensures business continuity during the transition. Detailed testing and a clear proof of concept are essential steps in the selection process.
The Gartner SASE model continues to evolve as new threats and technologies emerge. By following this framework, UK enterprises can build a flexible and secure foundation for their digital future. Consolidation toward unified platforms will be the defining characteristic of the market over the next several years.

Robert Sturt is a leading expert in SD-WAN and enterprise network solutions with extensive experience in telecommunications and network infrastructure. As a Forbes Business Council member and contributor to TechTarget, he provides strategic insights on network transformation and digital connectivity solutions. His expertise spans SD-WAN implementation, network security, and enterprise digital transformation initiatives.
Fact-checked by: Harry Yelland - Cybersecurity Writer, Netify
Frequently Asked Questions
What are the main components of the Gartner SASE model?
The SASE model is built on the convergence of five primary technologies. These include SD-WAN for networking and four security services. The security components are Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), Firewall as a Service (FWaaS), and Zero Trust Network Access (ZTNA). Together, these five elements provide a comprehensive framework for secure cloud connectivity.
Who are the current Leaders in the Gartner SSE Magic Quadrant?
According to the Gartner Magic Quadrant for Security Service Edge published in May 2025, the Leaders are Zscaler, Netskope, and Palo Alto Networks. Gartner evaluates these vendors based on their ability to execute and their completeness of vision within the SSE space. Magic Quadrant positions change with each annual update - verify current placement against the most recent Gartner publication before making procurement decisions.
What is the difference between SSE and SASE?
SSE and SASE are related but distinct concepts within the Gartner framework. SASE is the overarching architecture that combines networking (SD-WAN) with security services. SSE is a specific subset of SASE that focuses exclusively on the security components — SWG, CASB, ZTNA, and FWaaS - and does not include SD-WAN. Gartner publishes separate Magic Quadrant reports for SSE and SASE Platforms to help organisations evaluate vendors based on their specific architectural needs.
Does Gartner recommend a single-vendor approach for SASE?
Gartner increasingly recommends a single-vendor approach for SASE to achieve better integration and simplified management. A unified platform allows for consistent policy enforcement and improved visibility across the entire network. Gartner projects that by 2028, 30% of new SASE deployments will be consolidated into a single vendor, as part of the Gartner Strategic Roadmap for SASE Convergence. While some organisations still prefer a multi-vendor strategy, the market is moving toward consolidated platforms.