How AES Encryption Protects SD-WAN and SASE Traffic

What encryption does SD-WAN use?
SD-WAN architecture relies on encryption because traffic frequently moves across public internet connections, including commodity broadband and 4G/5G cellular links. To secure this data, platforms create virtual overlay tunnels that encapsulate and encrypt packets before they leave the branch office or data centre.
Major vendors such as Cisco Meraki, Fortinet, and VMware SD-WAN utilise AES-256 to secure their overlay fabrics. While the underlying transport may be an insecure public wire, the AES-encrypted payload remains protected from interception.
Is SD-WAN traffic encrypted by default?
The majority of enterprise SD-WAN platforms encrypt all overlay traffic with AES-256 by default. Network architects should still verify these settings during the procurement process, as some legacy or lower-cost solutions may require manual configuration to reach maximum encryption levels.
Certain platforms allow administrators to disable encryption for specific, non-sensitive traffic classes to reduce processing overhead, though this is rarely recommended for enterprise environments. Verifying that encryption is active for all production segments is a critical step in the initial deployment phase.
SASE platforms extend these protections to remote users through the Security Service Edge (SSE) layer. Whether a user connects via Zero Trust Network Access (ZTNA) or a Secure Web Gateway (SWG), AES-256 ensures that the connection from the individual device to the SASE POP is as secure as a site-to-site tunnel.
What is AES-256?
AES-256 is a symmetric block cipher that uses a 256-bit key to encrypt and decrypt data. In a network security context, this means both ends of an SD-WAN tunnel use the identical secret key to process information. The 256-bit key length provides a massive number of potential combinations, making it practically unbreakable with current computing power.

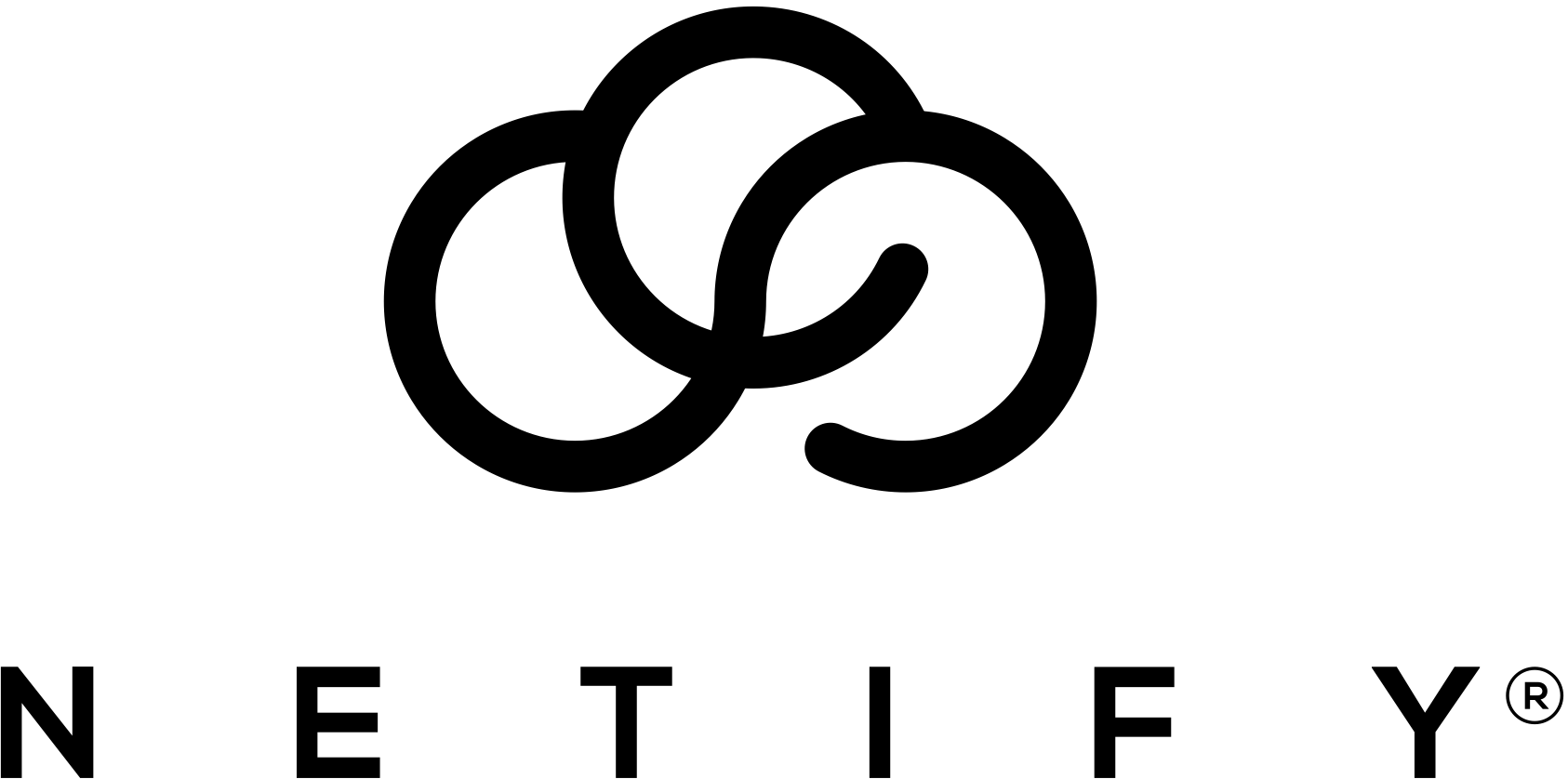
Deep Dive: What is AES?
The National Institute of Standards and Technology (NIST) recognises AES-256 as a standard for protecting sensitive and even top-secret data. For IT buyers, this certification provides assurance that the encryption method is mathematically sound and globally vetted. It remains the preferred choice for enterprises that must meet strict compliance requirements for data privacy and sovereignty.
How AES encryption works in practice
The encryption process begins by dividing plain text data into fixed-size blocks of 128 bits. The algorithm then performs a series of mathematical operations on each block using the 256-bit secret key to produce cipher text.
This process involves several distinct stages to ensure the data is thoroughly scrambled:
- Key Expansion: The system generates a series of subkeys from the original secret key for use in different rounds of the process.
- Round Function: A sequence of mathematical transformations is applied to the data blocks multiple times.
- Substitution-Permutation Network: The algorithm swaps specific data bits and shifts their positions to break any discernible patterns.
Once the cipher text reaches its destination, the receiving device uses the same secret key to reverse these operations. This returns the data to its original state for the end user or application.
Limitations and Future Considerations
The primary real-world risk to AES encryption is the compromise of the secret key rather than a failure of the algorithm itself. If an attacker gains access to the key through poor management or social engineering, they can decrypt the traffic without needing to break the cipher.
Quantum computing presents a theoretical future challenge to current encryption standards. Current consensus suggests that AES-256 is more resilient than AES-128 against quantum-based attacks. This is because Grover's algorithm can effectively halve the security strength of a key, leaving 256-bit encryption with a still-formidable 128 bits of security.
While quantum computers capable of such tasks do not yet exist for practical use, the potential risk is a factor in long-term security planning. Most organisations find that AES-256 provides a sufficient security margin for data that must remain protected for many years.

Robert Sturt is a leading expert in SD-WAN and enterprise network solutions with extensive experience in telecommunications and network infrastructure. As a Forbes Business Council member and contributor to TechTarget, he provides strategic insights on network transformation and digital connectivity solutions. His expertise spans SD-WAN implementation, network security, and enterprise digital transformation initiatives.
Fact-checked by: Harry Yelland - Cybersecurity Writer, Netify
Interested in CyberSecurity? Check out our guide to how AI has been utilised within CyberSecurity.