Who are the top rated ZTNA Providers & Vendors?

Zero trust network access (ZTNA) is now a fundamental requirement for securing distributed enterprise environments. The global zero trust network access market is projected to grow from 1.34 billion dollars in 2025 to over 4 billion by 2030 (according to 2025 data from MarketsandMarkets).
Given this, in this article we'll examine the leading ZTNA providers and the critical role of zero trust as a model for modern network security.
What is ZTNA (Zero Trust Network Access)?
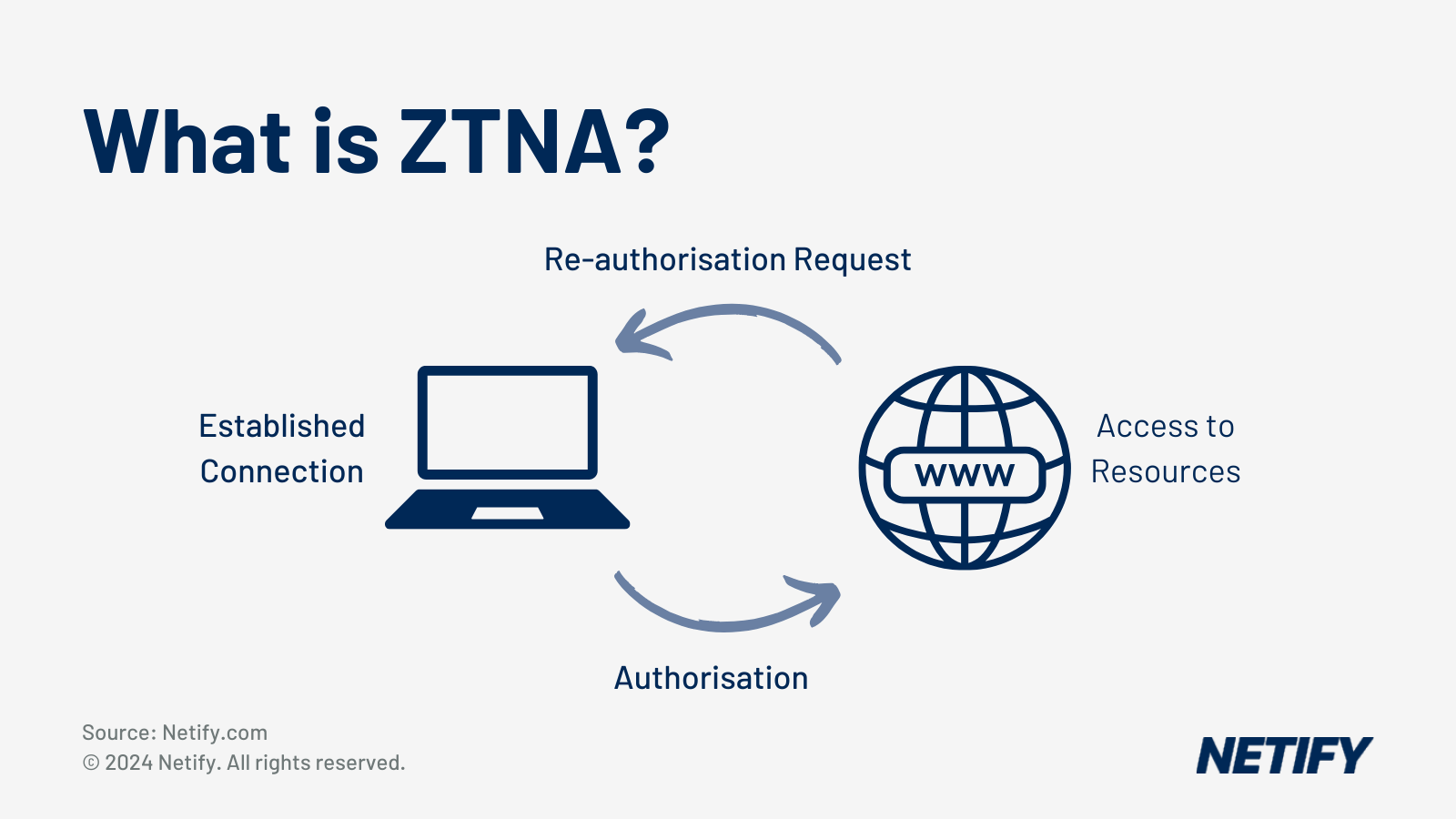
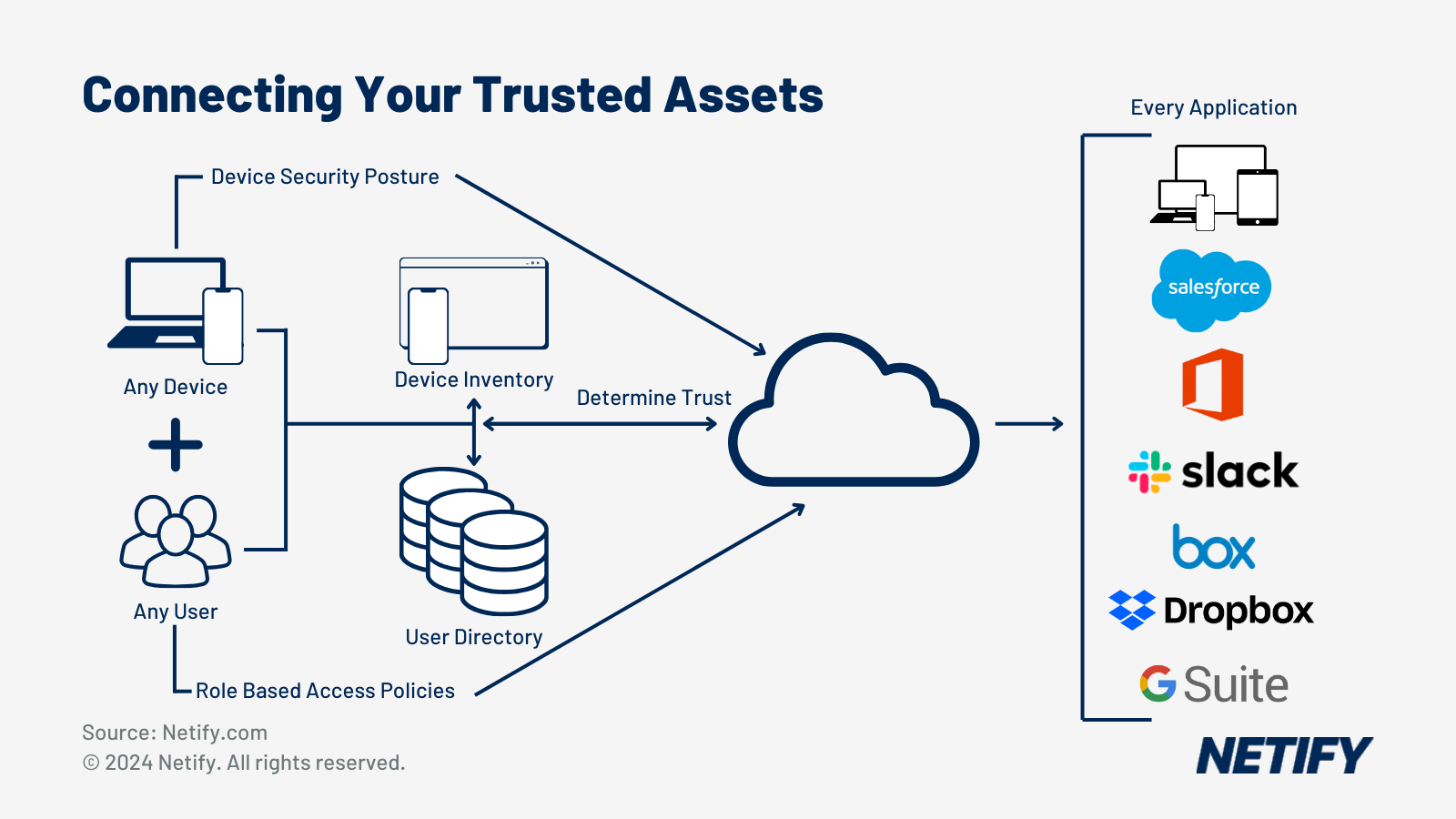
Zero Trust is about adding an additional layer of security. It means not fully trusting anything or anyone by default, and instead assuming that everything should be verified before being given access to a resource.
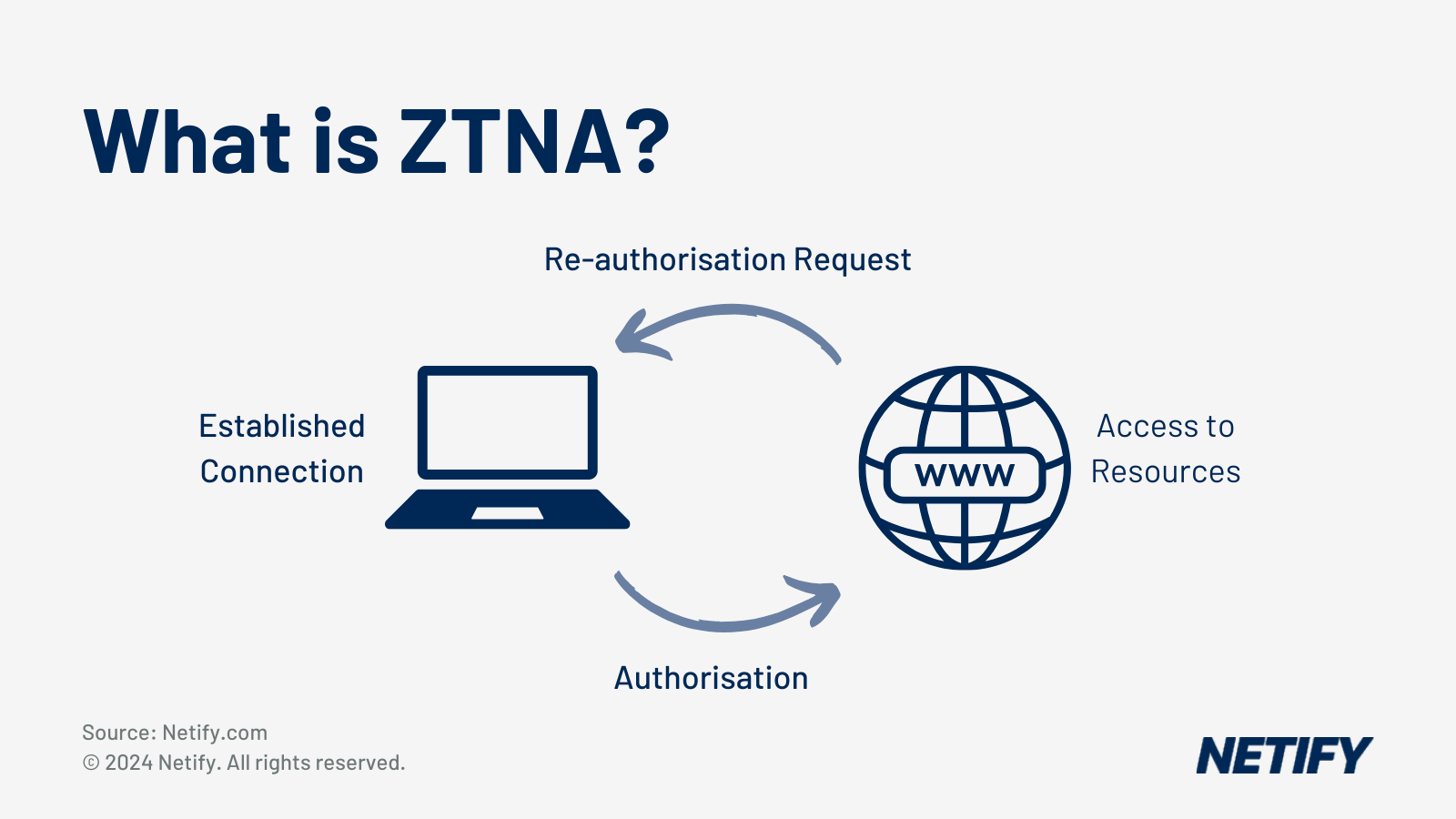
Enterprises are rethinking the access model for users and applications, ensuring that their business is safe from today’s threats while still providing seamless and reliable access from anywhere. This is where Zero Trust Network Access (ZTNA) comes in.
Explained: For more information on ZTNA check out our guide.
ZTNA is a security model designed to replace legacy models which made the assumption that anything inside a network was safe. This allowed bad actors to have free reign over data and infrastructure on the network should they gain access. Zero Trust intends to limit these issues with granular security steps throughout a network infrastructure. A complete Zero Trust implementation covers network infrastructure, users, workloads and applications. Choosing the right approach to Zero Trust for your company starts with choosing the right vendor. All vendors offer solutions designed specifically for their target demographic, so it is imperative to know which is the best option for each organisation’s path to Zero Trust.
Questions to help shortlist Zero Trust providers and vendors
- Is each request verified on a case-by-case basis? If so, how does this work?
- Does the vendor’s solution work with existing identity providers and Multi-Factor Authentication (MFA) solutions?
- Does the solution use artificial intelligence and/or machine learning to predict potential bad actors or behavioural actions?
- Can the vendor’s solution be managed from a single portal? Is it hosted in-cloud, on-premises or both?
- Does the solution integrate with Security Information and Event Management (SIEM) providers?
- Does the vendor’s solution support Single Sign-On (SSO) across all devices, users, departments and geographic locations using an open standard like Security Assertion Markup Language (SAML)?
- Is the vendor’s solution preventative or for visibility only? Can defensive actions be automated?
- What support model does the vendor offer? Is it included in subscription fees? Do they recommend professional services?
- What is the user experience like? Is it simple to implement and operate for users and administrators of all backgrounds?
- What level of visibility is provided by the vendor’s logs and context? Do they have logging APIs or syslog integration?
- What options are provided for integrations into the broader cybersecurity ecosystem?
The following table compares the capabilities of leading zero trust network access providers, highlighting the distinction between standalone products and SASE-integrated platforms. Pure-play standalone ZTNA vendors have become increasingly rare as the market has consolidated, with most enterprise procurement now involving ZTNA as part of a broader SASE or SSE platform and this distinction is critical for network architects deciding between a niche point solution and a unified security architecture.
| Vendor | Product Name | Delivery Model | SASE or Standalone | Agentless | Device Posture | UK PoPs | Pricing Model | Target Market |
| Zscaler | Zscaler Private Access (ZPA) | Cloud-native | SASE-integrated | Yes | Yes | Yes | Per-user | Enterprise |
| Palo Alto Networks | Prisma Access ZTNA | Cloud-delivered | SASE-integrated | Yes | Yes | Yes | Per-user | Enterprise |
| Cloudflare | Cloudflare Access | Cloud-native | Part of Cloudflare One (SSE) | Yes | Yes | Yes (extensive) | Free tier + per-user | SMB to enterprise |
| Fortinet | FortiZTNA | On-prem + cloud | SASE-integrated (FortiSASE) | Limited | Yes | Via FortiSASE PoPs | With FortiGate | Mid-market to enterprise |
| Cato Networks | Cato ZTNA | Cloud-native | SASE-integrated | Yes | Yes | Yes | Per-user | Mid-market |
| Appgate | Appgate SDP | On-prem or cloud | Standalone | No | Yes | Via customer deployment | Per-user licence | Enterprise, government |
| Netskope | Netskope Private Access (NPA) | Cloud-native | SASE-integrated | Yes | Yes | Yes | Per-user | Enterprise |
| Microsoft | Entra Private Access | Cloud-native | Part of Microsoft Entra SSE | Yes | Yes | Yes (Azure UK regions) | M365 bundled / per-user | Enterprise |
What is the Palo Alto ZTNA solution?
Palo Alto is a well-known industry leader with a broad product base. They are a good choice for large enterprises that have a need for a diverse mix of on-premise and SaaS requirements. Palo Alto also offers developing technologies such as DNS Security, which uses Machine Learning and Artificial Intelligence (AI)-supported URL filtering to detect and prevent zero-day web attacks.
What are the pros and cons of Palo Alto ZTNA?
What is the Akamai ZTNA solution?
Akamai is a leader in Zero Trust platforms with extensive experience in high-performance global content delivery, setting them apart from competitors. The company is a good choice for enterprises that host large amounts of sensitive data that has to be accessible 100% of the time from anywhere for customers and employees. Akamai provides excellent protection from downtime and known attacks.
What are the pros and cons of Akamai ZTNA?
What is the Zscaler ZTNA solution?
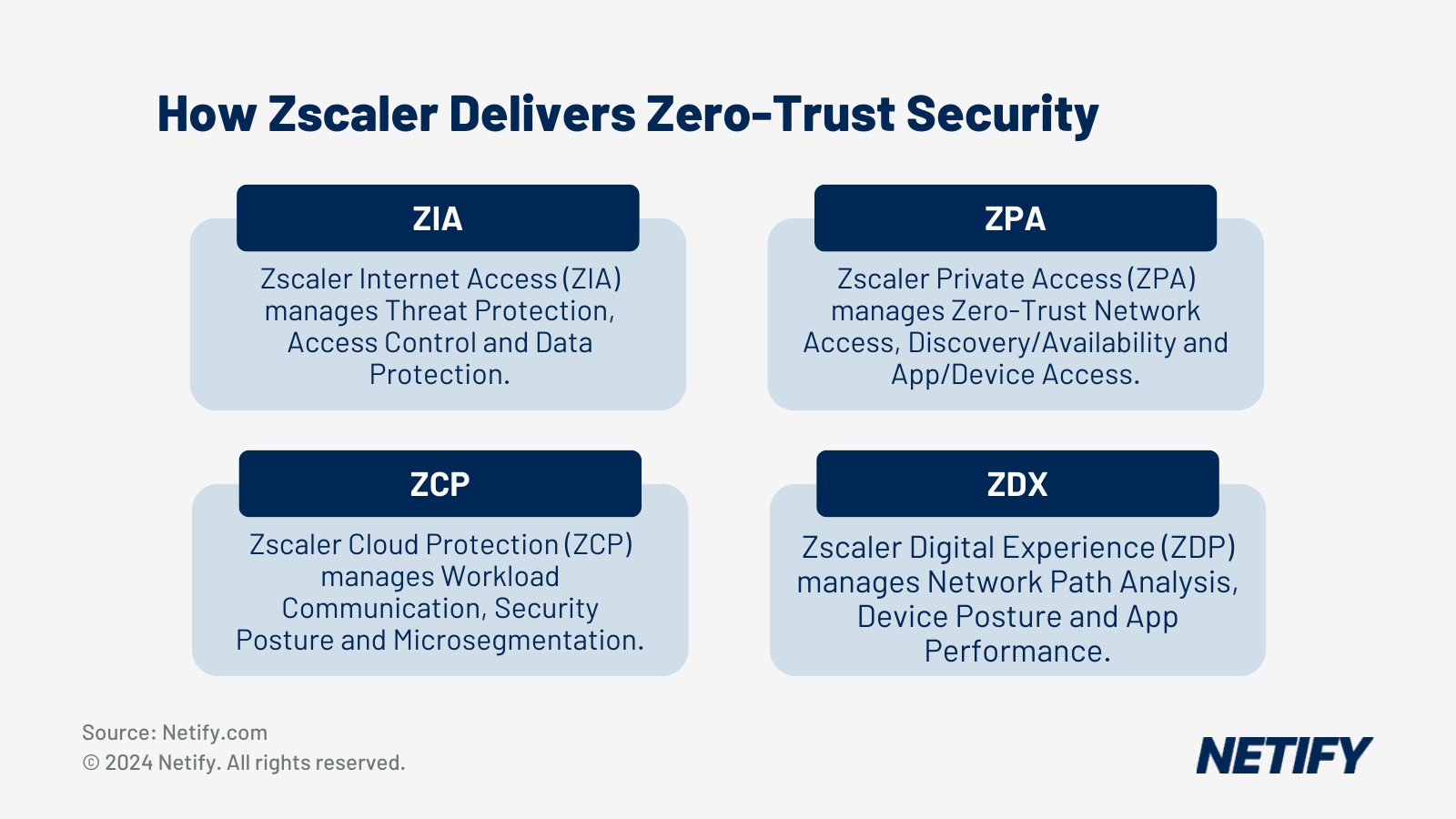
Zscaler is a cloud-native solution that has a large geographic footprint with over 150 data centres around the globe, offering reliable and high-performing services close to users no matter where they are. For very large enterprises looking for ease of use and a great user experience with a comprehensive solution that is easy to deploy and scale, Zscaler is a “must consider” solution.
What are the pros and cons of Zscaler ZTNA?
What is the Cato Networks ZTNA solution?
Cato Networks is an appropriate choice for those organisations with smaller IT teams and no need for on-premises deployments. The vendor offers managed services and is very efficient at bringing on new sites. Early adopters are also interested in Cato Networks as they are one of the first full-SASE platforms available and are entirely cloud-based, offering immediate deployment with little to no customer involvement.
What are the pros and cons of Cato Networks ZTNA?
What is the Cloudflare ZTNA solution?
Cloudflare's Zero Trust solution is high-performing, comprehensive and complex compared to other solutions on the market. It is suitable for clients with technical expertise and a robust IT team who is capable of deploying and managing complex solutions. Those with the capability to implement API integrations will benefit from the Cloudflare solution, as it makes it a good infrastructure solution for DevOps teams.
What are the pros and cons of Cloudflare ZTNA?
What is the Fortinet ZTNA solution?
Fortinet is an affordable solution for organisations who wish to simplify their network security stack without the need for brand new innovations. Fortinet’s product line is a comprehensive solution that allows the integration and addition of more products to increase feature sets not available in the core functionality provided by Fortinet out-of-the-box.
What are the pros and cons of Fortinet ZTNA?
What is the Forcepoint ZTNA solution?
Forcepoint is a leading Zero Trust platform focused on observability and data security. The solution is a good choice for organisations that require a deeper knowledge of what data users and applications are accessing and what they are using that data for. Context related to user and application actions is a driving factor in organisations that choose Forcepoint, as they are industry leaders in this area.
What are the pros and cons of Forcepoint ZTNA?
What is the Check Point ZTNA solution?
Check Point is one of the largest global network cybersecurity vendors and has a significant chunk of market share. Organisations looking for a well-rounded solution with innovative approaches to Zero Trust, including seamless integration, full automation and reliable core features that are constantly undergoing improvement, will get the most out of Check Point solutions.
What are the pros and cons of Check Point ZTNA?
What is the Cisco ZTNA solution?
Cisco’s solutions for ZTNA can be a good choice for any organisation that is already operating a Cisco environment. These organisations will already be familiar with the level of expertise required to properly design, deploy and manage Cisco products and will gain the most from Cisco’s offering.
What are the pros and cons of Cisco ZTNA?
Frequently Asked Questions
What is ZTNA?
Zero Trust Network Access (ZTNA) is a security model that provides application-level access based on user identity and device posture, without placing users on the corporate network. Unlike traditional VPNs, ZTNA verifies every access request individually and grants the minimum access required. It operates on the principle of “never trust, always verify,” ensuring that no user or device is granted implicit access based solely on their network location. This approach contrasts with legacy perimeter-based security models which often allow broad lateral movement once a user is inside the network. ZTNA is a critical component within the broader zero trust security framework.
Is ZTNA part of SASE?
Yes, ZTNA is one of the five core components of SASE, alongside:
- SD-WAN,
- Secure Web Gateway (SWG),
- Cloud Access Security Broker (CASB),
- Firewall-as-a-Service (FWaaS).
Organisations do not need to adopt a full SASE platform to deploy ZTNA, as many use it as a starting point before expanding their SASE adoption.
How much does ZTNA cost?
Pricing varies significantly based on deployment model and platform integration.
Which ZTNA vendors are best for UK organisations?
Several leading providers offer infrastructure within the UK to ensure data residency and low latency:
- Zscaler operates data centres in London and Manchester, relevant for meeting UK GDPR data residency requirements.
- Cloudflare maintains an extensive UK PoP network including London, suited to latency-sensitive deployments and organisations seeking a free entry point.
- Microsoft Entra Private Access is backed by Azure UK South (London) and UK West (Cardiff) regions, making it a strong fit for Microsoft 365-centric environments.
Cato Networks and Palo Alto Prisma Access also provide strong UK coverage, with Palo Alto recently expanding its compute locations to include UK West.

Harry holds a BSc (Hons) in Computer Science from the University of East Anglia and is ISC2 Certified in Cybersecurity (CC). He serves as a Cybersecurity Writer here at Netify, where he specialises in enterprise networking technologies. With expertise in Software-Defined Wide Area Networks (SD-WAN) and Secure Access Service Edge (SASE) architectures, Harry provides in-depth analysis of leading vendors and network solutions.
Fact-checked by: Robert Sturt - Managing Director, Netify