IT Decision Makers Guide to SD-WAN Security
SD-WAN security ensures that data remains protected whilst moving across diverse transport links such as broadband, 4G/5G, and MPLS. It provides a centralised way to manage encryption and access policies across a distributed organisation. Whilst SD-WAN improves flexibility, it also introduces risks by allowing direct internet access at branch sites.
This guide is written for IT decision makers responsible for evaluating and deploying secure network infrastructure. You must understand the distinction between basic connectivity features and the comprehensive security required for modern threats. We examine the current capabilities of leading vendors and the shift towards integrated security frameworks.
Looking to build your SD-WAN RFI? Why not give the Netify free SD-WAN RFI builder a go today?
What Does SD-WAN Security Actually Include?
Standard SD-WAN platforms focus primarily on network performance and connectivity. Security is often a secondary consideration, though basic features are typically included in the base licence. You should not assume that an SD-WAN appliance provides the same level of protection as a dedicated security stack.
Advanced Encryption Standard (AES) with 256-bit keys is the universal standard for securing data in transit. Every reputable vendor uses AES-256 to create secure tunnels between sites. Whilst this prevents eavesdropping, it does not inspect the traffic for malicious content.
Most vendors include a stateful firewall, but its capabilities vary. A basic firewall manages traffic based on ports and protocols, which is insufficient for blocking modern application-layer attacks. Enterprise-grade protection typically requires the addition of Secure Access Service Edge (SASE) or Security Service Edge (SSE) components.
SD-WAN Security Capabilities: What's Built In vs What Requires Add-Ons
AI's Role in Enhancing SD-WAN Security
Artificial Intelligence (AI) and Machine Learning (ML) are now used to manage the scale of modern network data. These technologies monitor traffic patterns in real time to identify anomalies that might indicate a security breach. This moves security beyond static rules to an adaptive model that responds to emerging threats.
Deep Dive: Netify explains how AI is affecting CyberSecurity
AIOps platforms automate routine troubleshooting and policy enforcement. By analysing telemetry data, these systems can predict link failures or detect unauthorised lateral movement within the network. This reduces the manual burden on IT teams whilst improving the speed of threat mitigation.
Juniper Networks is a prominent example of AI-first design with its Marvis Virtual Network Assistant. This system uses natural language processing and deep learning to provide insights into network health and security posture. Cisco also uses AI for encrypted traffic analytics, which identifies malware without needing to decrypt the data.
You should recognise that AI adds complexity to the network environment. Newly adopted AI features can introduce their own vulnerabilities if they are not configured correctly. These tools enhance human oversight but do not yet replace the need for skilled security administrators.
SD-WAN Vendors - Approach to Security
| Security Function | Built into SD-WAN? | Requires SASE/SSE Add-on? | Vendors with Native Support |
| Stateful firewall | Most vendors | No | Fortinet, Versa, Cisco |
| IPS/IDS | Some vendors | Often | Fortinet (FortiGuard), Versa |
| URL filtering | Rarely | Yes | Fortinet (partial) |
| CASB | No | Yes | Via Zscaler, Netskope, etc. |
| ZTNA | Rarely built-in | Yes | Fortinet (FortiZTNA) |
| DLP | No | Yes | Via SSE vendor |
| Sandboxing | Rarely | Yes | Fortinet (FortiSandbox) |
| Encryption (AES-256) | All vendors | No | All |
| Micro-segmentation | Some vendors | Sometimes | Versa, Fortinet |
Fortinet
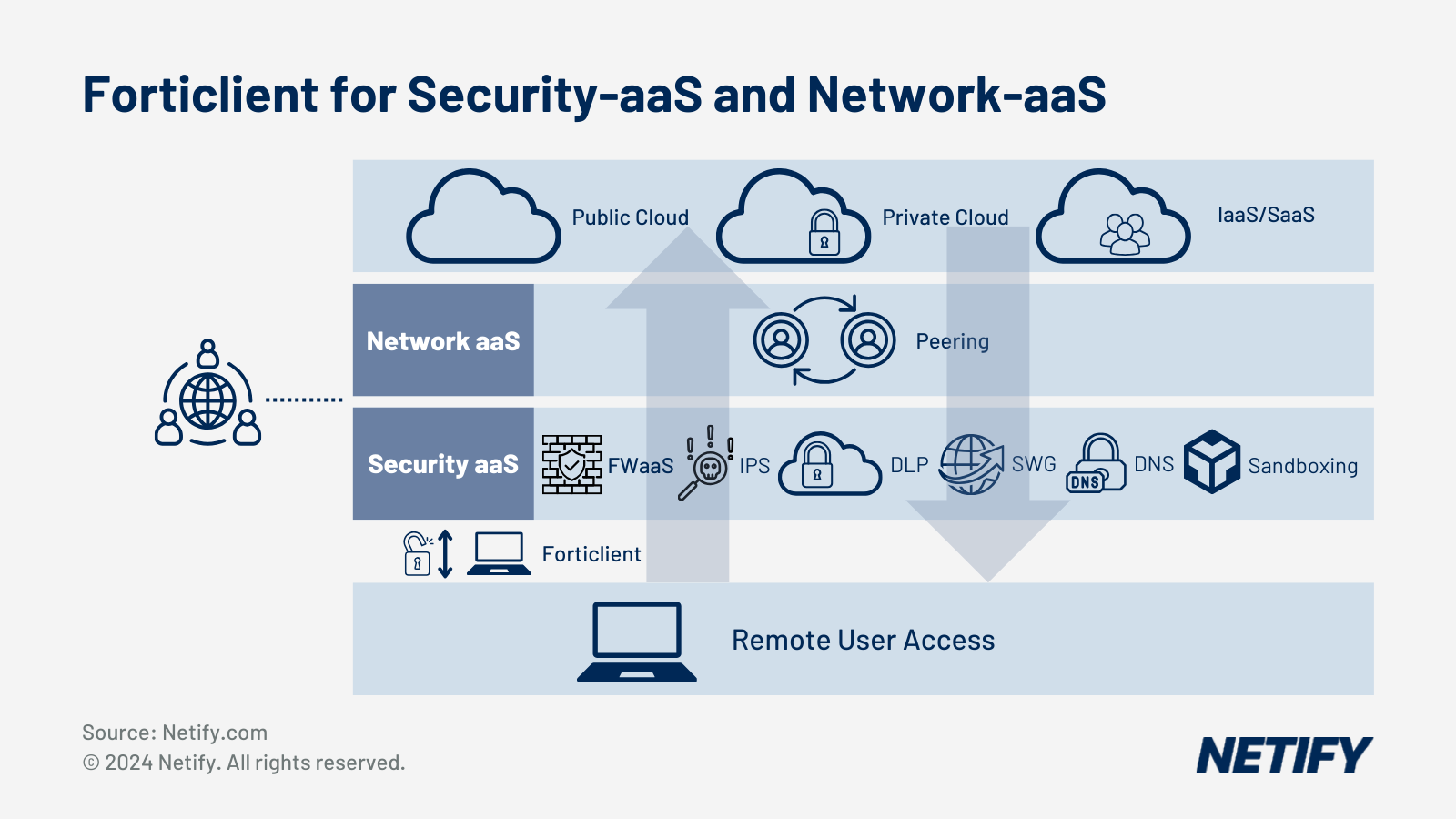
Fortinet integrates its security stack directly into the FortiOS operating system. Every FortiGate SD-WAN appliance includes a built-in Next-Generation Firewall (NGFW) with Integrated Intrusion Prevention System (IPS) and anti-virus capabilities. Their security is supported by FortiGuard Labs, which provides real-time threat intelligence updates. For organisations moving to a cloud-centric model, FortiSASE extends these protections to remote users, whilst FortiZTNA provides secure access to private applications.
Versa Networks
Versa Networks uses a multi-layered approach through its Versa Operating System (VOS). Security features like NGFW, UTM, and DNS security are embedded natively into the networking software rather than added as separate modules. This architecture allows for deep visibility across both branch and cloud traffic. Versa is also noted for its built-in micro-segmentation, which isolates different types of traffic to prevent threats from spreading across the network.
Cisco
Cisco Catalyst SD-WAN provides security through a distributed architecture that leverages Cisco Umbrella for DNS-layer protection. This integration allows IT teams to block malicious domains before a connection is ever established. For deeper inspection, Cisco offers NGFW integration and Cisco+ Secure Connect as a unified SASE path. Management is centralised through Catalyst Centre, formerly vManage, which ensures that security policies remain consistent across the entire fabric.
Comparative Analysis of SD-WAN Security
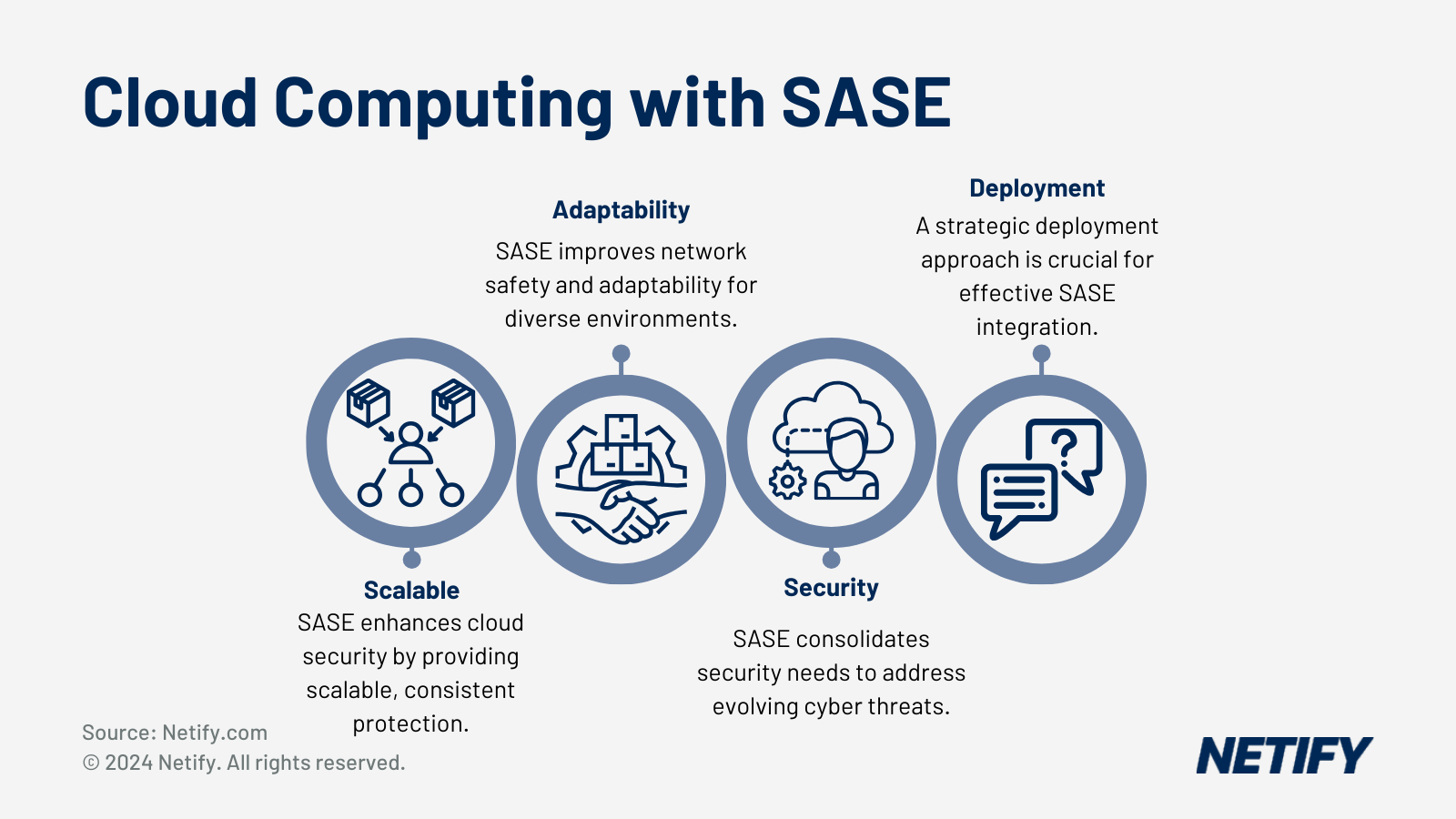
Enterprises are engaging in a digital transformation by adopting multicloud environments and software-as-a-service (SaaS) applications. Your company analysis of SD-WAN security mechanisms involves examining various implementations and their impact on factors such as latency, total cost of ownership (TCO), and security effectiveness.
Firewall devices offer protection and are typically selected by enterprises with existing comprehensive security measures. Basic firewall appliances are aimed at complementing rather than replacing in-depth security systems. On the other hand, devices with next generation firewalls deliver more refined protections and are often positioned as a mid-range option in terms of security capability comparison.
Companies opting for firewall appliances with embedded SD-WAN functions gain benefits from the depth of security features that firewall vendors have developed over time. The convergence of firewall and SD-WAN means that the majority of firewall vendors now offer comprehensive SD-WAN features to meet the needs of most requirements.
We are witnessing the growth and adoption of Secure SD-WAN as a Service, which merges SD-WAN and security into cloud services. The 'as a service' approach often entails advanced threat protection and intrusion prevention methods. Enterprises prioritising scalability and intelligence in their security strategies may also integrate with cloud-based security providers (AWS, Azure, Google Cloud etc).
The methodology in securing SD-WAN spans encryption of data in transit, using IPsec and SSL/TLS protocols to ensure data integrity. Alongside encryption, network segmentation (offered by specific vendors) aids in minimising attack vectors and maintaining compliance with continuous monitoring and real-time threat detection employed to safeguard direct Internet network traffic.
IT decision-makers must balance the trade-offs between security effectiveness, ease of management, and TCO. Each approach presents its unique attributes; comparative analysis of these mechanisms is fundamental to optimising the security of SD-WAN architectures.
As businesses send more traffic to cloud platforms (IaaS), the model of SD-WAN as a Service gains traction in partnership with cloud as a service solutions.
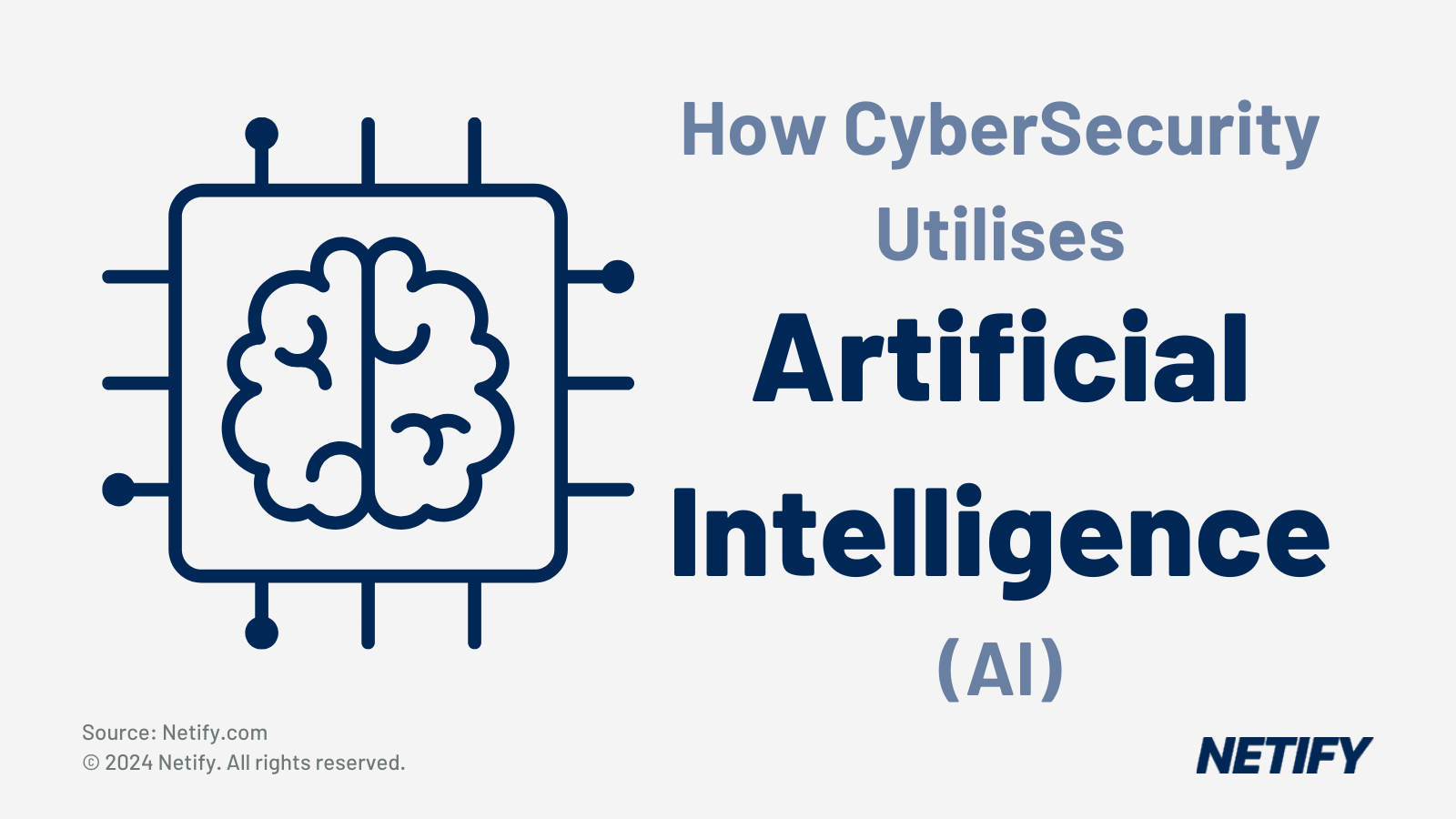
Zero Trust and SD-WAN
Zero Trust Network Access (ZTNA) is a security model that removes the concept of implicit trust. Every access request is verified based on identity, device posture, and context, regardless of the user's location. This differs from a traditional Virtual Private Network (VPN), which often grants broad access to the internal network once a user is authenticated.
VPNs are increasingly insufficient for modern distributed networks because they create a large attack surface. ZTNA restricts users to specific applications and continuously monitors the connection for changes in risk. In most SD-WAN deployments, ZTNA is delivered as a component of a SASE framework rather than a feature built into the branch hardware.
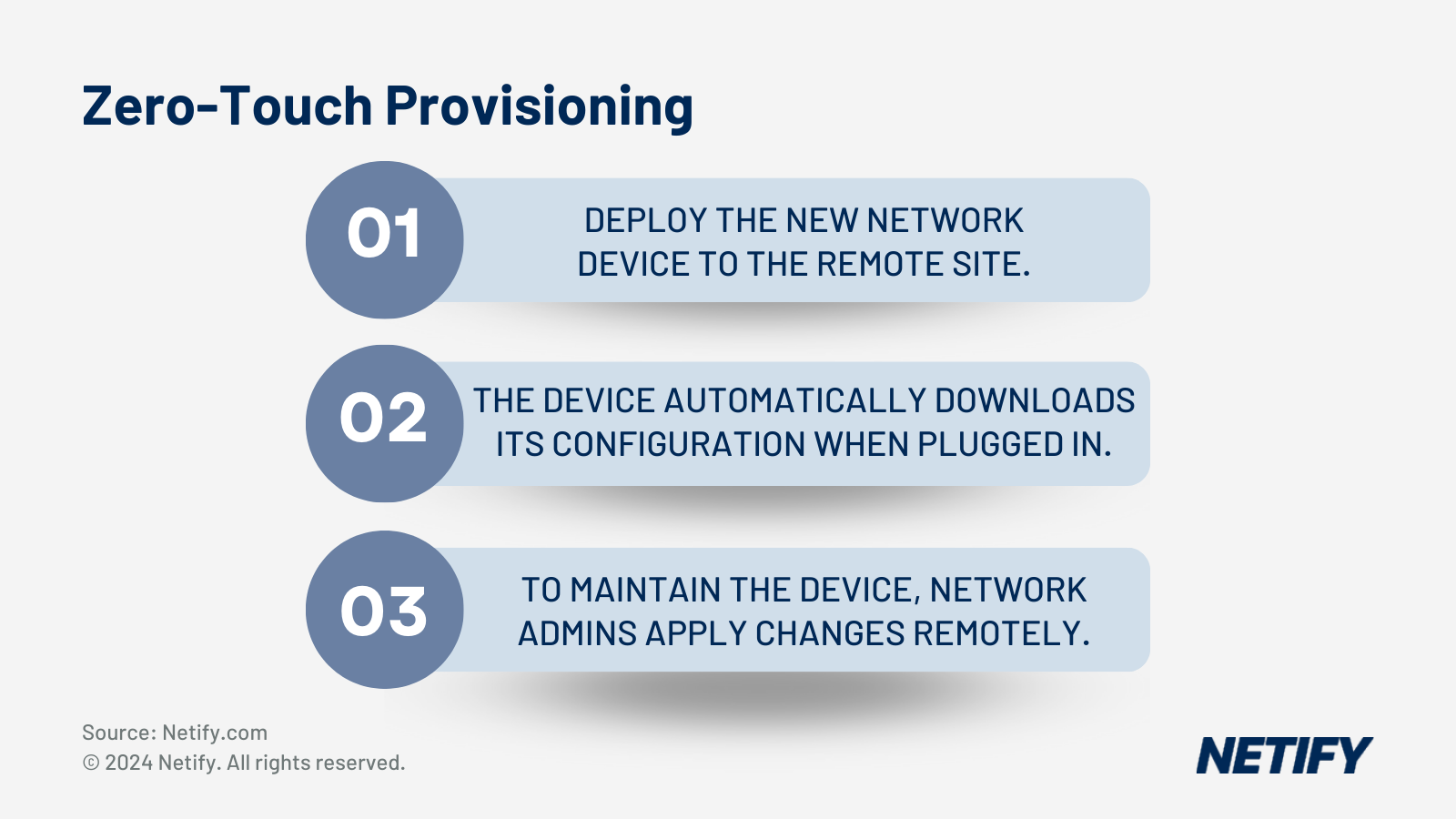
Zero Touch Provisioning (ZTP) is essential for maintaining a strong security posture during large-scale deployments. ZTP allows devices to be configured and authenticated automatically when they are first connected to the internet. This ensures that every new branch site adheres to corporate security policies from the moment it goes online, reducing the risk of human error.
What Are the Elements of SD-WAN Security?
The architecture of an SD-WAN solution lies at its foundation, enabling centralised management and support for applications across multicloud and software-as-a-service (SaaS)platforms.
Within this framework, encryption—often through IPsec—plays a critical role in protecting data as it travels across the network, whether that be through virtual or physical paths. Automation aids in the swift roll-out of updates to enhance the security posture, while scalability ensures that as the network grows, the security measures grow with it, without compromising on QoS or capacity.
The enterprise firewall and next-generation firewalls (NGFW) are needed to extend protection against intrusions and managing the security solution effectively. Secure Access Service Edge (SASE) is becoming integral to SD-WAN security, converging network and security functions to streamline service delivery. Secure web gateways offer another layer, deploying URL filtering and malware protection to thwart potential threats. A noteworthy mention is segmentation, or micro segmentation, which is available from specific vendors such as Cisco and Versa.
Cloud applications have placed demands on service delivery, with SD-WAN security providing the architecture to accommodate these applications securely. This allows businesses to maintain their agility and ensure users have the necessary access without compromising on security. The overall security solution of SD-WAN encompasses a layered approach, where integrated security and policy enforcement work in tandem.
Conclusion
The most important decision for IT teams is whether to rely on a vendor's native security stack or to complement SD-WAN with a separate SASE or SSE layer. Native stacks offer simpler management for some organisations, whilst separate layers may provide more specialised protection for complex environments.
Centralised management and visibility are just as important as the individual features on a data sheet. You must ensure that your team can monitor and update security policies across the entire network from a single interface. Without this oversight, even the most advanced security features can be undermined by inconsistent configuration.
SD-WAN security is moving towards greater convergence with SASE and increased use of AI-driven automation. As networks become more distributed, the ability to enforce consistent, identity-based security policies will be the defining factor in a successful deployment.

Robert Sturt is a leading expert in SD-WAN and enterprise network solutions with extensive experience in telecommunications and network infrastructure. As a Forbes Business Council member and contributor to TechTarget, he provides strategic insights on network transformation and digital connectivity solutions. His expertise spans SD-WAN implementation, network security, and enterprise digital transformation initiatives.
Fact-checked by: Harry Yelland - Cybersecurity Writer, Netify
Frequently Asked Questions
Is SD-WAN Secure?
SD-WAN encrypts all overlay traffic with AES-256 by default, but encryption alone does not make a network secure. Most SD-WAN platforms include a basic stateful firewall, but advanced security functions like IPS, CASB, ZTNA and DLP require either a SASE-integrated platform or a separate SSE add-on.
Do I need SASE if I have SD-WAN?
If your SD-WAN deployment includes direct internet breakout at branch sites, you need either a SASE platform or a separate SSE service to inspect and secure that traffic. Direct internet breakout creates a security gap because traffic bypasses the centralised security stack at the main data centre. SASE and SSE provide cloud-delivered security functions, such as malware scanning and data loss prevention, which are not typically available in a standard SD-WAN appliance.
Which SD-WAN vendors have the best built-in security?
Fortinet stands out because it uses a single operating system to provide a full suite of NGFW and ZTNA features natively on its SD-WAN hardware. Versa Networks is notable for its embedded security architecture and micro-segmentation, which provides high visibility into all traffic types. Cisco offers a strong integrated approach by combining its Catalyst hardware with Cisco Umbrella for DNS-layer security and cloud-delivered protection.