The 10 Best Managed SASE Providers for 2026
Compare the 10 best Managed SASE providers for 2026, including Cato Networks, Aryaka, and NTT. This guide evaluates single-vendor SASE, global PoP density, and security for hybrid work. Learn how leaders like Verizon and BT differentiate through AI-driven networking and multi-cloud optimisation.

Managed SASE has become the default network and security architecture choice for enterprises with distributed sites, hybrid workers or multi-cloud infrastructure, though it can often be difficult to differentiate providers that all appear to offer the same thing.
What's changed in 2026:
- Identity-first security has become an expectation, with most solutions offering ZTNA and is no longer a differentiator.
- Multi-cloud has become normal, with providers needing to secure and optimise traffic across the likes of AWS, Azure and GCP without routing everything back through a central hub.
- Data residency and sovereignty requirements are reshaping PoP selection, particularly for European and APAC customers.
- Enterprises expect phased implementations, not integrations that drag on for 12 months (or longer).
- More and more IT teams want greater policy control without managing infrastructure day-to-day, with the surge in co-managed models reflecting this.
- 24x7 SOC and NOC coverage is now expected at enterprise tier.
- Telcos are acquiring or partnering with SSE vendors to fill capability gaps
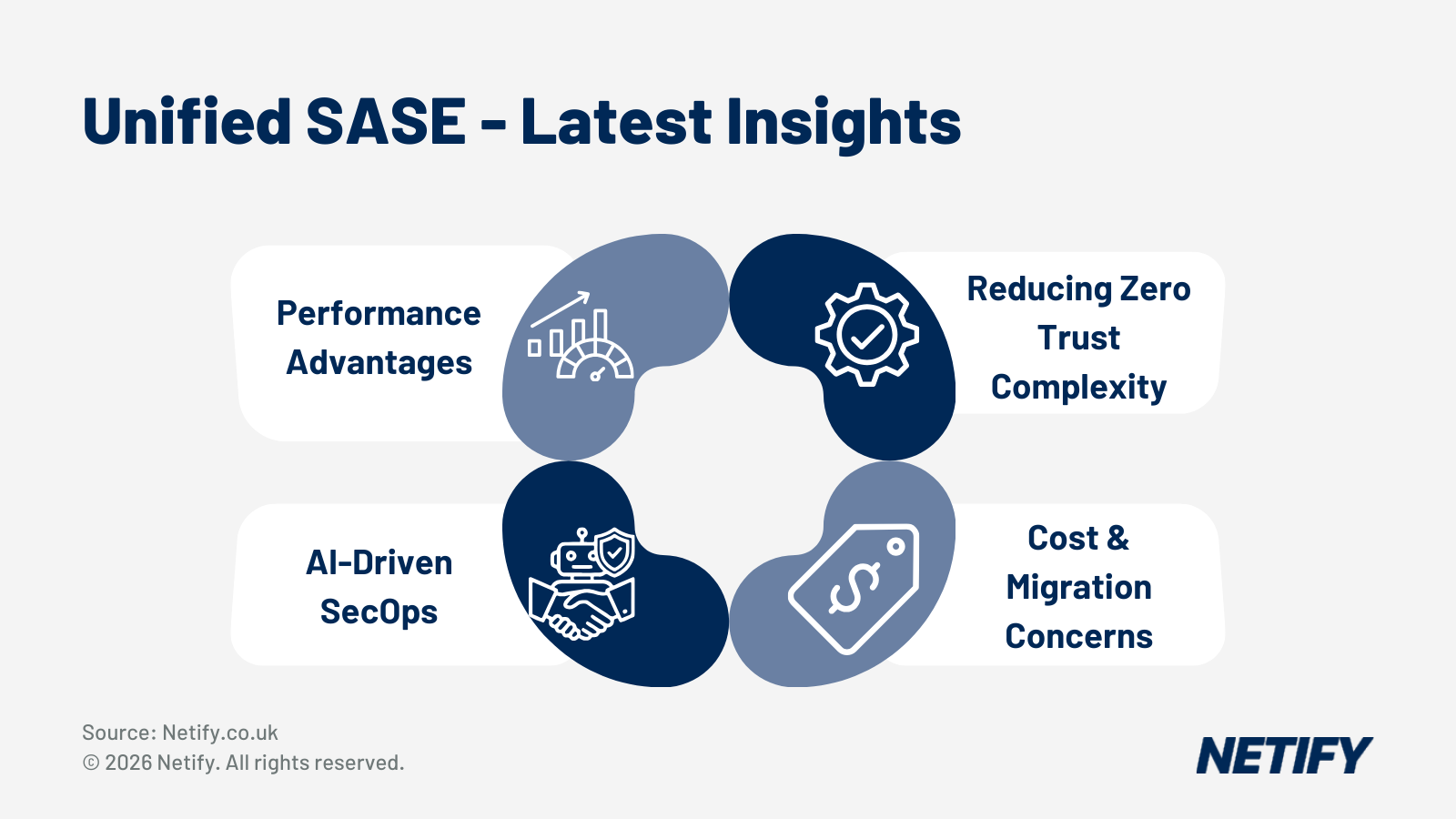
Deeper Dive: Unified SASE in 2026 and why it matters.
What are the leading SASE solutions for a global enterprise?
To help with deciding which provider to choose, we’ve created the following matrix to map the key selection criteria for global enterprise SASE procurement, with provider recommendations drawn from our 2026 managed SASE reviews. We’d recommend that you use the Evidence to Request column to guide your due diligence and the Questions to Ask column to pressure-test vendor claims during RFP responses and demo to assist with any SASE decision making.
Criteria | Our Recommendation | Evidence to Request | Questions to Ask |
Single Vendor Architectures | Cato Networks or Aryaka Both purpose-built single-vendor SASE platforms on private global backbones. One console, one policy engine, one data lake. Cato is the Gartner MQ Leader, Aryaka is #1 on G2 with Day 1 SLA enforcement. | Architecture diagram showing policy enforcement points Confirmation that SD-WAN and SSE run from the same codebase (not acquired and integrated) Number of management consoles required post-deployment | Are your SD-WAN and SSE built on a single codebase or integrated from separate acquisitions? How many consoles will our IT team need to operate day-to-day? If a new capability is required, can it be added to the existing platform or does it require a new product? |
Global PoP Coverage & Latency SLAs | Cato Networks (over 85 PoPs) or Aryaka (more than 40 PoPs, sub-30ms latency to 95% of the world’s business population) For APAC, Latin America and the Middle East coverage varies considerably across providers. Both offer private backbone PoPs - not public internet overlays. | PoP map specific to your target geographies (not a generic global map) SLA-backed latency commitments per region, not just average figures Customer references operating in your specific APAC or LATAM regions | Can you provide SLA-backed latency guarantees for our specific site locations - not just your headline 95th-percentile figure? Is traffic between PoPs carried on your private backbone or public internet transit? Which PoPs are owned vs. leased colocation? |
24x7 SOC & NOC Coverage at Scale | NTT Global or Verizon NTT operates 49 SOC facilities with more than 2,000 security professionals. Verizon's Threat Management Centres process over 1 trillion security events annually. Both provide integrated NOC and SOC under a single managed relationship. | Number of dedicated SOC analysts per customer account (not total headcount) Incident response SLA documentation for P1/critical events with escalation paths SOC locations and shift handover processes across time zones | Are your NOC and SOC integrated under one managed relationship or are they separate teams with separate SLAs? What is your committed response time for a P1 security incident at 3am in APAC? How many customers does each analyst manage on average? |
Zero Trust Network Access & Identity-First Security | Cato Networks, Aryaka, BT (via Palo Alto Prisma) or NTT Global (via Prisma Access) ZTNA is now table stakes, but depth of integration with your IdP (Entra ID, Okta) and device posture enforcement varies significantly. Verify Masergy separately - ZTNA is in development. | Documentation of IdP integrations (Entra ID, Okta, Ping) Device posture enforcement policy options and how they integrate with your MDM/UEM Reference deployment for ZTNA application onboarding timelines | How does your ZTNA enforce least-privilege access - by user identity, device posture or both? What is the typical timeline to onboard 100 private applications onto ZTNA? How do you handle users on unmanaged devices in regions where MDM rollout is incomplete? |
Deployment Speed & Phased Go-Live | Cato Networks or Aryaka Both cite sub-30-day go-lives per site using ZTP. Aryaka enforces SLAs from Day 1 with no stabilisation period. GTT and Globalgig also offer documented phased methodologies. | Reference deployment timeline from a comparable customer (site count, geography, complexity) ZTP documentation and CPE provisioning lead times for your target regions Phased migration playbook with rollback procedures | What is your documented go-live timeline for a site of our profile? Can you show us a comparable reference? Do you support a phased migration alongside existing infrastructure or is a cutover required? What is the stabilisation period before SLAs are enforced? |
Data Residency, Sovereignty & Regulatory Compliance | BT (EMEA/UK), NTT Global (global regulated sectors) or IBM (financial services, healthcare, public sector) Data residency and sovereignty are reshaping PoP selection for European and APAC customers. BT has deep UK/EMEA regulated sector experience, IBM brings Zscaler plus consulting depth for complex compliance programmes. | Data residency options per region - which PoPs can process and store your traffic logs GDPR, DPDP (India) and sector-specific compliance certifications (ISO 27001, SOC 2) Audit trail and change management documentation for regulated sectors | Which PoPs will process our UK and EU traffic and can you contractually commit to data residency? How do you handle data sovereignty requirements that differ between our operating regions? What compliance certifications are current and which are in progress? |
Co-Managed Flexibility & IT Team Oversight | Globalgig, Lumen, Aryaka or Cato Networks All four offer genuine three-tier management models. Globalgig's Orchestra portal provides granular co-managed controls, Lumen's model explicitly excludes bandwidth overage charges across all tiers. | Demo of co-managed portal showing which policy functions customer IT teams can control Documented delineation of responsibilities for co-managed deployments Escalation path if a customer policy change causes a network event | Which specific policy functions can our IT team control in the co-managed model and which remain with you? If we make a policy change that causes an outage, what is the escalation and resolution path? Can we move between management tiers during the contract without renegotiation? |
AI-Driven Management & GenAI Traffic Security | Aryaka (AI>Secure) or Cato Networks (native AI platform) Aryaka's AI>Secure is the most comprehensive GenAI security capability in this guide - blocking prompt injections, jailbreaks and token flooding for ChatGPT, Copilot and internal LLMs. Cato's unified data lake feeds AI models trained across all customers. Masergy offers AI-driven autonomous networking. | Technical documentation on how AI/ML models are trained and updated GenAI traffic inspection capabilities - which models and services are covered Autonomous response capabilities vs. alert-only capabilities | Can you inspect and enforce policy on employee traffic to ChatGPT, Microsoft Copilot and other GenAI services? Is your AI built natively into the platform or is it a bolt-on from a third party? What autonomous actions can the AI take without human approval and what requires authorisation? |
Owned Network Infrastructure (Tier 1 / Private Backbone) | GTT (Tier 1 global IP backbone) or Lumen (owned MPLS, DIA, broadband, Layer 2) GTT's Secure Connect sits on its own Tier 1 backbone, reducing public internet transit for SASE traffic. Lumen includes the underlay in the SASE subscription with no bandwidth overage charges - a significant TCO differentiator. | Network topology documentation showing owned vs. third-party transit paths for your regions Confirmation of whether bandwidth overages are included in the subscription SLA scope - does uptime coverage extend to the full path or only the last mile? | What percentage of our traffic will traverse your owned infrastructure vs. third-party transit? Are bandwidth overage charges included in our subscription or billed separately? Who is accountable for SLAs when a failure occurs on a third-party transit segment? |
Multi-Vendor SSE Flexibility (Protect Existing Investments) | Verizon or NTT Global Verizon maintains active SSE partnerships with Palo Alto, Zscaler, Versa, Cisco and Netskope. NTT supports six SD-WAN vendors alongside Prisma Access. Both can accommodate existing vendor investments rather than requiring rip-and-replace. | Full list of supported SSE and SD-WAN vendors with version support matrix Reference deployment that retained an existing SSE vendor Roadmap for SSE vendor additions or deprecations | We have existing [Zscaler/Palo Alto/Cisco] investments - can your managed service incorporate these rather than replacing them? If we want to change SSE vendor mid-contract, what is the migration process and cost? Do you have preferred SSE partners who receive more development investment than others? |
How do you choose scalable SASE providers for multinational organisations?
Shortlisting a provider that performs well against the criteria above is only part of the challenge, we’d recommend that you are also confident it can deliver that same performance consistently across all sites (especially when considering multinationals). For these instances we’d suggest considering the below scalability challenges for organisations operating across multiple countries.
Key scalability challenges for multinationals:
- PoP coverage gaps in secondary markets. Global coverage isn’t always equal and in APAC, LATAM and the Middle East PoP coverage varies significantly across providers, it's therefore worth verifying coverage in your specific target regions.
- Data sovereignty and regulatory compliance. Depending on your operating regions, there may be data sovereignty/regulatory compliance considerations (such as GDPR in Europe) - not all providers can make contractual commitments to every regulation, making this worth checking early into procurement.
- Deployment speed across multiple countries. Rolling out SASE across 50, 100 or 500 sites requires a repeatable provisioning process, with predictable CPE lead times and documented cutover methodologies to ensure potential issues are minimised. Alongside this, for businesses concerned over rollout speeds, we’d recommend insisting on Zero Touch Provisioning capabilities from any chosen provider.
- Consistency of managed service quality across regions. Global managed service quality is rarely uniform and a provider with NOC and SOC offerings may operate differing levels of operations across regions - often delivered through local partners rather than a centralised operation. We’d recommend clarifying whether global SLAs leverage a single management plane or if multiple separate regional teams are used, with this having direct implications for incident response times and service consistency.
- Multi-vendor security stack integration. For organisations that already have existing investments in vendor security stacks (such as Zscaler, Palo Alto or Cisco), a full rip-and-replace of architecture may not actually be desirable or practical. Providers that require a single SSE vendor introduce lock-in risk and can force a costly security migration on top of the network transformation itself therefore it’s worth considering which is more applicable to your use case.
What to look for:
Scalability in managed SASE isn't just about PoP count - we'd recommend evaluating these five key factors:
- The architecture of the provider's global backbone (owned vs leased),
- The specificity of regional latency SLAs,
- The maturity of zero-touch provisioning for multi-site rollouts,
- The strength of data residency controls per jurisdiction
- How consistently the managed service model holds up across geographies.
The table below maps each of these to the evidence we'd suggest requesting during due diligence.
Requirement | Why | Verify | Notes |
Private backbone or owned PoPs | Public internet overlays introduce latency variability that SLAs cannot reliably compensate for. Owned backbone ensures predictable performance across regions. | Architecture diagram showing which PoPs are owned vs. leased colocation. Ask for a percentage of SASE traffic that traverses owned infrastructure. | Cato (more than 85 PoPs) and Aryaka (more than 40 PoPs, sub-30ms SLA) both operate private backbones. GTT and Lumen bring owned network underlay. NTT and Verizon use a mix of owned and leased infrastructure. |
SLA-backed latency per region (not global averages) | Headline global latency figures disguise significant regional variation. Latency to your sites in APAC, LATAM or the Middle East may be materially higher than the headline number. | Contractual latency SLA for each of your target site locations, not just a global 95th-percentile figure. Customer references in the same geographies. | Aryaka’s sub-30ms SLA covers 95% of the world’s business population. Cato has more than 100 PoPs across six continents. Coverage in APAC, LATAM and the Middle East varies significantly across providers. |
Zero-touch provisioning (ZTP) and phased deployment methodology | Multi-country rollouts across 50+ sites require repeatable, documented deployment processes. Manual CPE provisioning at scale introduces delay, inconsistency and risk. | ZTP documentation and CPE provisioning lead times for your target regions. A reference deployment timeline from a comparable customer (site count, geography, complexity). | Cato and Aryaka both cite sub-30-day go-lives per site using ZTP. Aryaka enforces SLAs from Day 1. GTT and Globalgig offer documented phased methodologies. BT uses a 100-point deployment checklist. |
Data residency and sovereignty controls per region | GDPR, DPDP and other regional data protection frameworks require that traffic logs and inspection data are processed and stored within specific jurisdictions. Not all providers can contractually commit to this. | Contractual data residency commitments per region. A list of which PoPs can process and store your traffic logs. Current compliance certifications (ISO 27001, SOC 2, sector-specific). | BT has the strongest UK/EMEA regulated sector track record. NTT covers global regulated sectors. IBM brings deep compliance consulting capability alongside its Zscaler-based managed service. |
Multi-vendor SSE support (protect existing investments) | Enterprises with existing Zscaler, Palo Alto or Cisco security investments may not want a full rip-and-replace. Some providers are platform-agnostic, others mandate a specific SSE vendor. | Full list of supported SSE and SD-WAN vendors with version support matrix. A reference deployment that retained an existing SSE vendor. | Verizon and NTT support the widest SSE vendor ecosystems. Globalgig spans Palo Alto, Cisco, Fortinet, Peplink and Cradlepoint. IBM (Zscaler only) and BT (Palo Alto only) are single-vendor SSE. |
24x7 SOC and NOC at enterprise scale | At enterprise scale, 24x7 SOC and NOC coverage is not optional. What matters is analyst-to-customer ratio, incident response SLA and whether NOC and SOC are integrated or separate. | Number of dedicated SOC analysts per customer account. P1 incident response SLA with escalation path. SOC locations and shift handover processes across time zones. | NTT operates 49 SOC facilities with more than 2,000 security professionals. Verizon processes over 1 trillion security events annually. Masergy runs three global 24x7 SOCs. All with integrated NOC and SOC. |
Who are the most affordable SASE providers for global enterprise networks?
For most businesses, one of the key considerations is the cost of SASE, though we’d suggest that affordability isn’t necessarily just about the lowest headline price, as the full cost of ownership is often determined by many variables and this can make comparing quotes harder. The cost drivers and savings opportunities below give procurement teams a framework for doing exactly that.
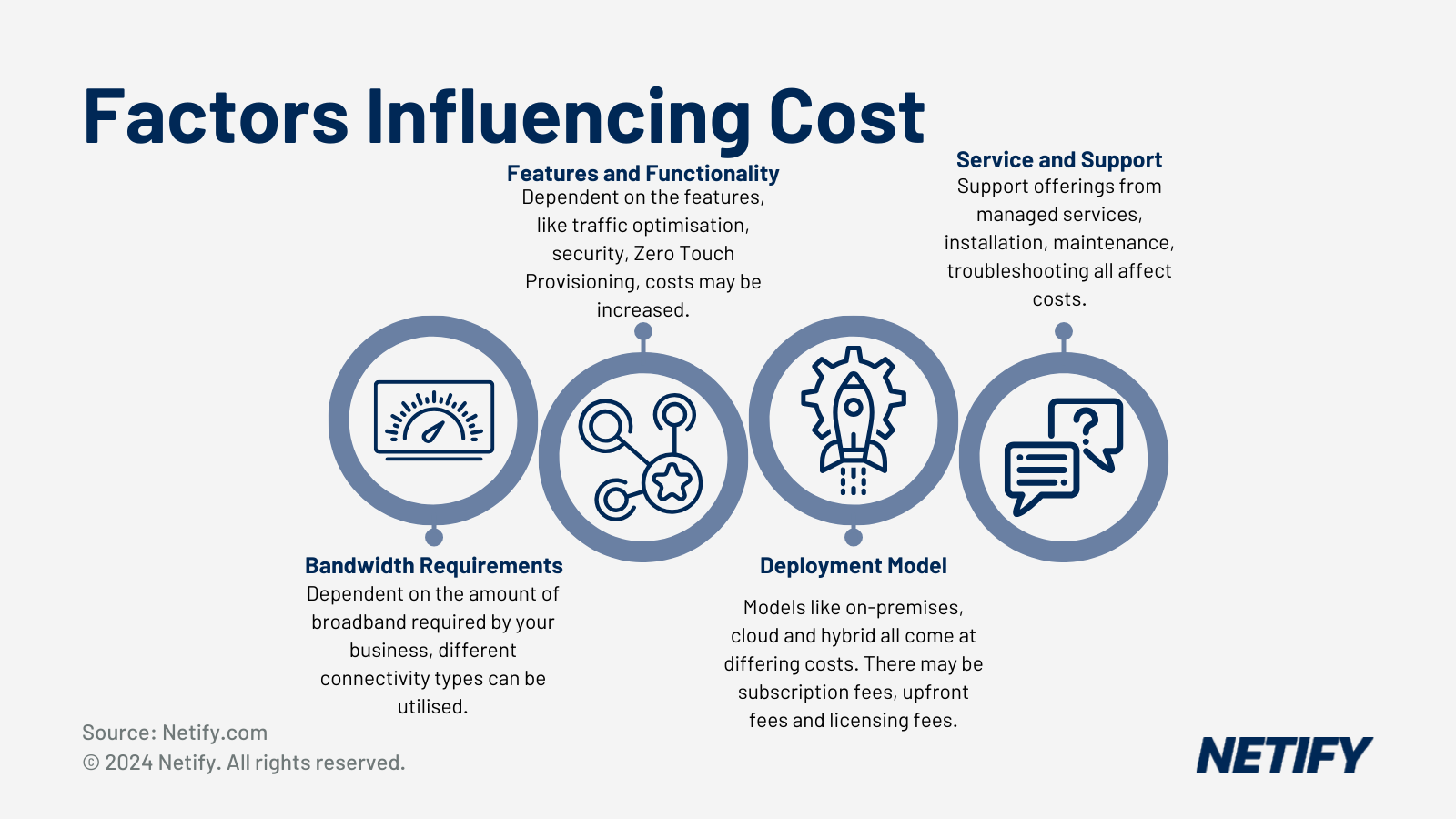
Key cost drivers:
For organisations with thousands of users, per-user licensing tends to be the largest line item (for user-based pricing models), with most SSE components (ZTNA, SWG and CASB) priced per user per month. This, therefore, makes it worth negotiating volume tiers and multi-year commitments early in the procurement cycle.
For SASE implementations that utilise hardware appliances, vCPE licences and per-site installation fees can also add up quickly across a global estate and since some providers bundle CPE into the monthly service fee whilst others charge separately, we'd suggest normalising these costs across shortlisted vendors to make TCO comparisons more straightforward.
The managed service uplift for NOC/SOC management, 24x7 monitoring and incident response typically adds a significant overhead on top of self-managed licensing costs. This is often where the real differentiation between providers lies and where reference calls are particularly useful. It's also worth clarifying early on how underlay connectivity is scoped, as some providers include MPLS, broadband and LTE within the managed SASE price whilst telco-backed providers such as BT, Verizon and NTT tend to bundle underlay into a single invoice, which simplifies procurement but can increase lock-in. Design, migration and cutover services are usually charged separately and can represent a meaningful share of year-one total cost, so where possible we'd recommend pushing for fixed-price onboarding commitments, as time-and-materials engagements can escalate on complex global deployments.
Where savings typically come from:
Replacing expensive MPLS circuits with broadband, LTE or SD-WAN overlays is consistently the largest source of recurring savings, with organisations in APAC and LATAM frequently reporting WAN spend reductions of 40-60% within two to three years of migration. Further to this, consolidating point security products (like standalone firewalls, proxy appliances, DLP tools and VPN) onto a single SSE platform can also deliver meaningful savings by removing per-product licensing costs, reducing maintenance overhead and cutting the number of vendor relationships to manage.
Outsourcing NOC and SOC functions is another area worth considering, as it frees internal networking and security engineers from reactive break-fix work and allows them to focus on architecture, policy and more strategic priorities. For organisations already finding it difficult to recruit and retain security staff, this is often the most compelling part of the ROI argument.
Finally, for cloud-first organisations still backhauling internet traffic through a central data centre, shifting to local internet breakout at the PoP edge can reduce latency, lower egress costs and improve user experience, with savings that tend to grow as cloud application usage increases.
The 2026 Top 10 Managed SASE Provider Reviews
The reviews below cover the ten managed SASE providers Netify considers best positioned for enterprise procurement in 2026, assessed across network architecture, SOC and NOC capability, deployment methodology, identity integration, co-managed flexibility and SLA commitments, giving you a basis to easily compare different provider offerings.

Globalgig
Globalgig is a technology-agnostic managed SASE and SD-WAN provider headquartered in San Antonio, Texas, delivering fully managed and co-managed services globally. Where many managed SASE providers lock you into their preferred vendor stack, Globalgig builds environments from whichever combination of hardware and software best fits your requirements, with their portfolio spanning Palo Alto Prisma, Cisco (both Catalyst and Meraki), Fortinet, Peplink and Cradlepoint, with everything managed through its Orchestra Insight AI platform.
Best for: Technology-agnostic enterprises wanting a deeply customised managed SASE service with strong co-managed flexibility.
Key Strengths:
- Technology-agnostic design: Spans Palo Alto Prisma, Cisco Catalyst, Cisco Meraki, Fortinet, Peplink and Cradlepoint - no forced vendor lock-in.
- Orchestra Insight AI platform: Provides real-time traffic monitoring, application visibility and performance analytics with proactive alerting.
- Co-managed option: Gives customer IT teams access to specific policy controls via the Orchestra portal while leaving infrastructure management to Globalgig.
- GDPR-compliant data handling: Via DLP and CASB, with documented healthcare-specific ZTNA configurations.
- Three service tiers: (Essential, Plus, Premier) let organisations scale the managed service as capability changes.
Offered SLAs:
100% uptime guarantee for all High Availability (HA) configurations. <50ms latency guaranteed for the core inter-regional IP VPN network within the U.S.
Platform Review
Globalgig's managed SASE platform is orchestrated through Orchestra Insight, an AI-driven management layer that sits above the underlying vendor hardware. This architecture gives Globalgig the flexibility to deploy whichever combination of SD-WAN and SSE technology best fits the customer's requirements, whilst maintaining a consistent management and monitoring experience.
Service Tiers
Globalgig offers three service tiers - Essential, Plus and Premier. Essential provides baseline monitoring and support, Plus adds proactive management and enhanced SLAs, Premier covers full end-to-end managed operations including proactive threat response and dedicated service management.
Security Posture
Globalgig's managed SASE security is delivered primarily via Palo Alto Networks Prisma Access for SSE functions (ZTNA, SWG, CASB), as well as Fortinet for NGFW, SWG and UTM. GDPR-compliant DLP and CASB controls are included as standard.
Recent Integrations
In March 2025, Globalgig added Palo Alto Networks Prisma SASE to its managed portfolio, giving customers a single-vendor SASE option alongside its established multi-vendor approach.

Masergy (Comcast Business)
Masergy is a fully managed SASE provider, now operating under the Comcast Business umbrella following its acquisition. Delivered from three global 24x7 SOCs and built on Fortinet SD-WAN and Forcepoint CASB, the service is designed for enterprises that required entirely managed operations, all of which is supplemented with AI-driven autonomous networking at its core.
Best for: Enterprises with limited internal network operations resource that need a fully managed, AI-driven SASE service with end-to-end SOC accountability.
Key Strengths:
- Early SD-WAN innovator and Comcast Business acquisition has significantly improved AI and autonomous networking capability.
- Three global 24x7 SOCs providing fully managed turnkey service with end-to-end accountability (no handoff between separate network and security operations teams).
- AI-driven SASE on Fortinet SD-WAN and Cloud Firewall combined with Forcepoint CASB, with autonomous network management capabilities.
- Available as security-driven SD-WAN, as part of a broader SASE strategy or as a standalone managed security service - three distinct entry points.
Trade-offs and Considerations:
- ZTNA is on the roadmap but not yet fully delivered. If zero trust network access is a near-term requirement rather than a 12 - 24 month objective, we’d recommend that you verify current availability explicitly before shortlisting.
- Multi-vendor SSE stack (Fortinet & Forcepoint) means policy management spans more than one console.
Offered SLAs:
- 100% service availability for sites configured with High Availability.
- 5-minute proactive notification guarantee in the event of a circuit or device outage.
SOC & NOC Geographic Presence:
Operations are supported by three global 24/7 Security Operations Centers with primary headquarters in Frisco, Texas.
Platform Review
The core of Masergy's platform is its AI-driven network management layer, which sits above the underlying Fortinet SD-WAN and Forcepoint CASB infrastructure. The AI capability is what makes the fully hands-off model ideal for use at scale - rather than relying on human intervention for routine routing decisions and policy adjustments, the platform handles these autonomously, with SOC engineers focused on escalations and threat response rather than day-to-day network management tasks. For enterprises that want a managed service that genuinely reduces operational burden rather than simply outsourcing the same work, this is a key differentiator. With this, the three global SOCs provide follow-the-sun coverage with end-to-end accountability - one provider owns detection, response and remediation rather than splitting responsibility between a network operations team and a separate security operations function.
Service Tiers
Masergy offers the service as a fully managed deployment - there is no co-managed or self-managed option (in the traditional sense). With regards to different service tiers, there is a more entry positioned solution with Masergy's AI-driven managed SD-WAN, which can be extended with SASE security functions or delivered as a standalone managed security service. Organisations with an existing network infrastructure can add the security layer without replacing their WAN or take the full converged SD-WAN plus security stack depending on where they are in their network lifecycle.
Security Posture
Masergy’s security offering leverages the likes of Fortinet's FWaaS and SWG alongside Forcepoint CASB for cloud access controls – though it’s worth noting the current exclusion of ZTNA capabilities, which are currently in development on Masergy's roadmap. Given this, if zero trust network access is a near-term requirement rather than a longer-term objective, this is worth considering when shortlisting. For wider security, the three global SOCs provide 24x7 threat monitoring, incident response and escalation, with defined SLAs for response times across all tiers.
Recent Integrations
The most significant recent development for Masergy is the ongoing integration into Comcast Business's broader enterprise portfolio. This brings additional network infrastructure investment and AI research capability to the platform, but it also means commercial and support structures are in transition. Organisations entering multi-year contracts should clarify which entity they are contracting with and how service continuity is guaranteed across the transition period.

NTT Global
NTT Global offers managed SASE utilising Palo Alto Networks Prisma Access, combining its own threat intelligence and SOC capability with one of the most widely recognised SASE platforms in the Gartner Magic Quadrant. The service covers fully managed and co-managed models, supported by over 2,000 security professionals across six 24x7 SOCs and differentiates itself from other Prisma-based managed services with its offerings of SPEKTRA for analytics and service management, Cortex XSIAM for AI-driven detection and response and a structured ITIL-aligned change management process that governs every policy modification.
Best for: Large enterprises needing deeply integrated managed SASE with enterprise-grade threat detection on top of Palo Alto Networks Prisma.
Key Strengths:
- NTT's Enhanced Advanced Threat Detection (EATD) adds proactive threat hunting, advanced analytics and incident validation on top of Prisma Access via SPEKTRA and Cortex XSIAM.
- Security Device Management handles all Prisma Access policy changes to ITIL change management best practices.
- Six SD-WAN vendor options: Cisco Catalyst, Fortinet, VMware, Cisco Meraki, Versa Networks and HPE Aruba EdgeConnect.
Trade-offs and Considerations:
- Palo Alto-only SSE dependency – creates complexity and increases TCO if you have existing investments in other SSE vendors.
- Enterprise scale means longer sales cycles and more complex commercial negotiations than smaller specialist providers.
Offered SLAs:
- 100% service availability goal across the Global IP Network backbone.
- Packet loss is guaranteed not to exceed 0.1% with an average jitter of <250 microseconds.
SOC & NOC Geographic Presence:
Features a massive global support footprint with 49 SOC facilities and specialised regional NOCs in Bengaluru, Barcelona and Birmingham.
Platform Review
NTT's managed SASE platform is built on Palo Alto Networks Prisma Access, delivering ZTNA, SWG, CASB and FWaaS through a single cloud-native SSE platform. What differentiates NTT's delivery from a directly-bought Prisma deployment is the layer of proprietary intelligence and automation it adds on top: SPEKTRA for analytics and service management and Cortex XSIAM integration for AI-driven detection and response. All Prisma Access policy changes are handled through NTT's Security Device Management service, following ITIL best practices - meaning configuration changes are tested, documented and tracked rather than applied ad hoc and for large enterprises with complex change control requirements, this structured approach reduces the risk of policy drift or misconfiguration at scale.
Service Tiers
NTT offers fully managed and co-managed models. In the fully managed model, NTT takes responsibility for Prisma Access policy management, threat detection, monitoring and incident response end-to-end. The co-managed option gives customer IT teams access to specific operational functions whilst NTT retains infrastructure management and both models are supported by NTT's 24x7 SOC coverage across six global locations.
Security Posture
Whilst the solution utilises the in-built security delivered through Palo Alto Networks Prisma Access, (covering ZTNA, SWG, CASB and FWaaS in a unified cloud-native stack), the key differentiator is the aforementioned NTT overlays. The Enhanced Advanced Threat Detection capability providing proactive threat hunting, predictive analytics and automated incident validation, Cortex XSIAM integration enables faster response than standard Prisma management alone and NTT's Security Device Management service ensures all policy changes meet ITIL-aligned change control standards – which is particularly relevant for organisations in regulated sectors where audit trails are a compliance requirement.
Recent Integrations
NTT's most notable recent development is the SPEKTRA platform and Cortex XSIAM integration, which brings AI-driven predictive analytics and automated response to its managed Prisma deployments.

GTT
GTT is a fully managed SASE provider that delivers its Secure Connect service over its own Tier 1 global IP backbone - one of the key differentiators for organisations that want SASE traffic to stay off public internet transit for as much of its journey as possible. The service supports both Palo Alto Networks Prisma SASE and Fortinet and is delivered globally from GTT's headquarters in Arlington, Virginia, with strong coverage across North America and EMEA.
Best for: Multinational enterprises wanting a fully managed SASE solution delivered over a provider-owned Tier 1 global network.
Key Strengths:
- GTT Secure Connect delivered over GTT's own Tier 1 global backbone, reducing reliance on third-party transit for SASE traffic.
- Available with Palo Alto Networks Prisma SASE (added July 2025) and Fortinet, covering SD-WAN, FWaaS, SWG, CASB and ZTNA.
- Named a Leader in both Managed SD-WAN and SASE in the 2025 ISG Provider Lens Report for the US and UK.
- EnvisionDX portal provides real-time network visibility, performance insights and management controls.
- DDoS mitigation via 10 global scrubbing centres.
Trade-offs and Considerations:
- Private company post-restructuring - review financial stability documentation during due diligence.
- Palo Alto Prisma SASE addition (July 2025) is relatively recent - verify maturity with reference deployments on this specific stack.
Offered SLAs:
- 100% uptime guarantee on its Tier 1 global IP backbone infrastructure.
- 30-minute target response time for all initial service desk requests.
SOC & NOC Geographic Presence:
Provides 24/7 management from core centres in Arlington, London and Frankfurt, backed by 10 global scrubbing centres.
Platform Review
GTT's Secure Connect platform sits on top of its own Tier 1 global IP backbone, which means SASE traffic stays on GTT-owned infrastructure for more of its journey compared to providers that rely on third-party transit. The EnvisionDX portal provides customers with real-time visibility into network performance, security events and operational status and is worth evaluating via a live demo during procurement to assess reporting depth and usability. GTT's Professional Services and NOC/SOC teams handle solution design, deployment, ongoing policy management and incident response.
Service Tiers
GTT delivers Secure Connect as a fully managed service - design, deployment, policy management and 24x7 NOC/SOC coverage are all included. There is no self-managed option, the model is built around GTT's operational teams taking end-to-end accountability. Customers can choose between the Palo Alto Networks Prisma SASE stack (single-vendor, unified cloud-native) or the Fortinet-based option, which can be paired with third-party SD-WAN from HPE Aruba or Broadcom VMware for organisations that want dual-vendor architecture flexibility.
Security Posture
GTT's security capability is delivered through either Palo Alto Networks Prisma SASE (covering SD-WAN, FWaaS, SWG, CASB and ZTNA in a unified stack) or Fortinet SSE on GTT's network. DDoS mitigation is available through 10 global scrubbing centres, providing protection at the network edge before traffic reaches customer environments. Both SSE options include full traffic inspection, with Prisma SASE offering the additional benefit of a single policy engine and console across all security functions.
Recent Integrations
The most significant recent development is GTT's expansion of its Secure Connect portfolio with Palo Alto Networks Prisma SASE in July 2025. This adds a single-vendor SASE option to GTT's existing Fortinet-based offering, giving organisations the choice between a unified cloud-native stack (Prisma) or a more flexible dual-vendor architecture (Fortinet plus third-party SD-WAN).

IBM
IBM delivers managed SASE as a consultancy-led, fully managed service built on Zscaler - wrapping Zscaler Internet Access (ZIA) and Zscaler Private Access (ZPA) in IBM's global professional services capability. The service is designed for large enterprises with complex multi-cloud environments, existing IBM security investments or significant compliance and regulatory requirements. IBM is headquartered in Armonk, New York and operates in over 170 countries.
Best for: Large enterprises with complex multi-cloud environments and existing IBM security investments needing managed SASE with deep consulting capability.
Key Strengths:
- IBM Security Services for SASE delivers a fully managed Zscaler platform from initial strategy through to continuous policy management.
- Deep consulting capability: readiness workshops, zero-trust strategy and ZTNA application onboarding.
- IBM stack integration - IBM Security Verify (identity), MaaS360 (endpoint), QRadar (threat operations) - providing unified policy across the security estate.
- Strong regulated sector experience in financial services, healthcare and public sector.
Trade-offs and Considerations:
- Zscaler-only SSE dependency - IBM's current managed SASE offering is specifically built on Zscaler.
- Consultancy-led model adds significant value for complex programmes but increases cost and timelines.
- Enterprise-tier pricing - unlikely to be the most competitive option for mid-market organisations.
Offered SLAs:
- Managed SASE platform availability ranges from 99.9% to 99.999% depending on the specific vendor partner (e.g., Zscaler).
- 15-minute response time commitment for critical (P1) security incidents via Managed Security Services.
SOC & NOC Geographic Presence:
Operates one of the largest global security networks with major SOCs in Bengaluru, Wroclaw, Sydney and Tokyo.
Platform Review
IBM's managed SASE service doesn't operate a proprietary SASE platform - it delivers a fully managed Zscaler environment, with IBM's professional services organisation handling strategy, design, migration and ongoing management. ZIA covers internet access security (SWG, CASB, FWaaS, DLP) and ZPA covers private application access (ZTNA). What IBM brings on top is its consulting depth and its integration with the broader IBM security portfolio. The result is a managed SASE service that is particularly well-suited to organisations that need significant programme management, legacy dependency mapping or integration with existing IBM security tooling - rather than a provider that primarily competes on deployment speed or price.
Service Tiers
IBM operates a single fully managed model - there is no co-managed or self-managed option in IBM's SASE service. Engagement typically begins with a discovery and readiness assessment, followed by design, migration, application onboarding and transition to ongoing managed operations. The scope of the initial programme varies significantly depending on the complexity of the existing environment, so timelines and costs are scoped individually rather than offered as standardised tiers.
Security Posture
Security is delivered through Zscaler Internet Access (ZIA) for internet-bound traffic (SWG, CASB, FWaaS, DLP, threat prevention) and Zscaler Private Access (ZPA) for private application access (ZTNA). Integration with IBM Security Verify provides identity governance and SSO, MaaS360 handles endpoint posture and QRadar provides SIEM and threat intelligence correlation. For organisations already running this stack, the integration depth is a genuine advantage. However, for organisations evaluating Palo Alto Prisma, Cato or Aryaka as their preferred SSE platform, IBM's managed SASE service won't accommodate them.
Verizon
Verizon is a fully managed SASE provider with over 20 years of enterprise network management experience, delivering its SASE Management service through an integrated NOC and SOC covering both connectivity and security under one managed relationship. The service supports a multi-vendor SSE ecosystem including Palo Alto Networks, Zscaler, Versa Networks, Cisco and Netskope. Verizon is headquartered in New York City with strongest coverage in North America.
Best for: US-headquartered multinationals needing a fully managed SASE service over an established global network with a mature multi-vendor SSE ecosystem.
Key Strengths:
- Over 20 years of enterprise network design and management experience.
- SASE Management merges SD-WAN and cloud security under a single integrated NOC and SOC - one service relationship for both.
- Multi-vendor SSE ecosystem: partnerships with Palo Alto Networks, Zscaler, Versa Networks, Cisco and Netskope.
- Named a Leader in the IDC MarketScape for Worldwide Managed SD-WAN/SASE Services 2023 and in the Gartner Magic Quadrant for Global WAN Services 2025.
Trade-offs and Considerations:
- Coverage is strongest in North America - verify EMEA and APAC PoP depth against your specific footprint.
- Enterprise-scale commercial structures, mid-market organisations may find better value elsewhere.
Offered SLAs:
- 100% for high-priority sites, 99.9% availability for standard branch tiers.
- Time to Repair (TTR) guarantee of 3.5 hours for US sites and 4 hours for international locations.
SOC & NOC Geographic Presence:
Verizon's Threat Management Centres (TMCs) are distributed globally, processing over 1 trillion security events annually.
Platform Review
Verizon's SASE Management service is built on top of one of North America's largest enterprise networks, giving the platform a strong underlay foundation for US-heavy deployments. The key operational differentiator is the integration of NOC and SOC functions - rather than managing network performance and security operations separately, Verizon handles both through a single managed service structure with unified visibility across the estate. SSE flexibility is also notable: Verizon doesn't mandate a single SSE vendor, instead maintaining active partnerships with Palo Alto Networks, Zscaler, Versa Networks, Cisco and Netskope - which means it can accommodate existing SSE investments or help select the right platform based on requirements.
Service Tiers
Verizon's SASE Management is delivered as a fully managed service. The integrated NOC and SOC provide 24x7 monitoring, performance management and incident response for both connectivity and security. Organisations with existing Verizon network relationships can extend those into SASE without replacing the underlying network contract.
Security Posture
Verizon's SSE is delivered across a multi-vendor ecosystem rather than a proprietary stack. Active partnerships with Palo Alto Networks, Zscaler, Versa Networks, Cisco and Netskope mean security policy can be built around the platform most appropriate for the organisation's requirements - or around existing investments already in place. SD-WAN is delivered via Versa Networks or Cisco cEdge/vEdge, with the security and network layers managed as a unified service through the integrated NOC/SOC.
Recent Integrations
Verizon's recent focus has been on expanding its SSE partner ecosystem and deepening its SASE Management capabilities as the market moves towards converged networking and security. The Gartner Magic Quadrant for Global WAN Services 2025 recognition reflects Verizon's positioning as a global managed network provider with integrated security capabilities, rather than a pure-play SASE vendor.
Lumen
Lumen is a managed SASE provider offering three distinct management models - pro-managed, co-managed and self-managed - built on Fortinet and Versa Networks, with Lumen's own network (MPLS, DIA, broadband, wireless, Layer 2) as the underlay. The service removes bandwidth overage charges by including the underlay as part of the managed SASE subscription. Lumen is headquartered in Monroe, Louisiana, with strong North American coverage and global reach via partnerships.
Best for: Enterprises wanting a flexible, cloud-first managed SASE service with a genuine choice of management model and no bandwidth overage charges.
Key Strengths:
- Three management models - pro-managed, co-managed and self-managed - genuine flexibility for varying IT capabilities.
- SASE platform on Versa Networks and Fortinet, covering SD-WAN, NGFW, SWG, ZTNA, CASB, DLP, remote browser isolation and DDoS mitigation.
- Lumen's own network as the underlay (MPLS, DIA, broadband, wireless, Layer 2) - simplifies procurement and removes bandwidth overage charges.
- Named Frost & Sullivan's 2024 Customer Value Leader in the Global Managed SASE Service Industry.
Trade-offs and Considerations:
- Geographic strength is predominantly North American - verify EMEA and APAC underlay and PoP availability for your specific footprint.
- Self-managed option places significant operational burden on the customer's IT team.
Offered SLAs:
- 100% availability for High Availability configurations and 99.99% for standard setups.
- <15-minute response time and <4-hour restoration target for critical (Severity 1) tickets.
SOC & NOC Geographic Presence: Global operations are anchored in Monroe, LA, with primary regional support centers in Singapore, Tokyo and Sydney.
Platform Review
Lumen's SASE platform combines Fortinet and Versa Networks for SD-WAN and NGFW functions, with a full SSE capability set including SWG, ZTNA, CASB, DLP, remote browser isolation and DDoS mitigation. The important operational distinction is that Lumen provides the underlay network as part of the managed service - not just the SASE software layer. This means organisations get MPLS, DIA, broadband, wireless and Layer 2 Ethernet through a single contract, without bandwidth overage charges that often appear as a surprise cost in managed SASE quotes. The dual-vendor approach (Fortinet & Versa) does mean policy management spans more than one console, which is worth factoring into the operational overhead comparison.
Service Tiers
Lumen offers three management models. Pro-managed is fully outsourced - Lumen handles design, implementation, configuration, monitoring and support for the full contract term. Co-managed lets customer IT teams retain control of specific policy functions whilst Lumen manages infrastructure. Self-managed uses Lumen's platform but places all operational responsibility with the customer - this option is primarily suited to organisations with strong internal networking capability that want access to Lumen's network without paying for managed operations.
Security Posture
Security is delivered through Fortinet and Versa Networks covering NGFW, SWG, ZTNA, CASB and DLP. Remote browser isolation is included for high-risk browsing scenarios and DDoS mitigation is built into the underlay network layer. The full SASE security stack is available across all three management models, though in the self-managed model the operational responsibility for configuration and policy management rests with the customer's IT team.
BT
BT is a fully managed SASE provider built on Palo Alto Networks Prisma SASE, delivering end-to-end managed networking and security from one of Europe's largest telecoms providers. The service combines Prisma SD-WAN and Prisma Access into a single-vendor managed stack, handled by BT's NOC and SOC teams, with particular strength across the UK and EMEA.
Best for: UK-headquartered and EMEA-focused multinationals, particularly in regulated industries, wanting a fully managed SASE service from one of Europe's largest telecoms providers.
Key Strengths:
- Fully managed SASE on Palo Alto Networks Prisma SASE: Built on a platform named a Leader in the Gartner Magic Quadrant for SASE Platforms for three consecutive years (2023-2025).
- Strong EMEA and UK market depth: BT's regional infrastructure and enterprise heritage provide capability that North American telcos struggle to match in Europe.
- Rigorous delivery process: Utilises a 100-point deployment checklist and thorough security testing before go-live to ensure a structured, repeatable rollout.
Trade-offs and Considerations:
- Commercial structures are designed for enterprise-tier accounts; mid-market organisations may find the engagement process heavyweight.
- Global coverage outside of EMEA relies more heavily on network partnerships than owned infrastructure.
Offered SLAs:
- 100% target availability for premium "BTnet" and managed SASE service tiers.
- 5-hour target fix time for dedicated fiber lines used in SASE deployments.
SOC & NOC Geographic Presence:
Support is primarily managed from the UK with specialized EMEA-focused SOCs and technical staff in 100+ global locations.
Platform Review
BT's managed SASE service is built on Palo Alto Networks Prisma SASE, combining Prisma SD-WAN and Prisma Access in a single-vendor stack managed end-to-end by BT's teams. The architecture gives customers a unified platform across networking and security - one console, one policy engine, one support relationship. BT's delivery model is structured around a 100-point deployment checklist and pre-go-live security testing, which provides a documented, repeatable process particularly valued in regulated sectors where change control and audit evidence are procurement requirements. VMware SASE (Broadcom) is also available as an alternative platform for organisations with existing VMware investments.
Service Tiers
BT delivers SASE as a fully managed service - design, hardware and policy configuration, deployment, ongoing management, monitoring and incident response are all included. There is no self-managed tier; the model is based on BT's teams taking full operational accountability. Co-managed arrangements can be discussed for specific policy elements, but the default and primary commercial model is fully managed. Enterprise accounts are BT's primary market; mid-market organisations should expect a heavyweight commercial engagement.
Security Posture
Security is delivered through Palo Alto Networks Prisma Access, covering ZTNA, SWG, CASB, FWaaS and NGFW in a unified cloud-native stack. Palo Alto was named the only three-time Leader in the Gartner Magic Quadrant for SASE Platforms in 2025, providing strong independent validation of the platform's security capabilities. BT's SOC provides 24x7 threat monitoring, incident response and escalation for all managed SASE customers, with defined SLAs and BT's enterprise service management processes.
Recent Integrations
BT's managed SASE service is built on Palo Alto Networks Prisma SASE and the ongoing strengthening of that platform - including Palo Alto's third consecutive Gartner Magic Quadrant Leadership recognition in 2025 - directly benefits BT's managed service customers. BT has also continued to expand its EMEA professional services capability around SASE deployments, particularly for regulated sectors including financial services and public sector where BT has long-standing enterprise relationships.

Cato Networks
Cato Networks is a cloud-native, single-vendor SASE provider that purpose-built its platform before Gartner formally defined the category. Every function - SD-WAN, ZTNA, SWG, CASB, FWaaS, DLP, IPS and AI-driven MDR - runs from a single codebase through one console on a private global backbone with more than 85 PoPs. The service is available fully managed, co-managed and self-managed via Cato's MSASE Partner Platform or direct. Cato is headquartered in Tel Aviv.
Best for: Enterprises wanting a genuinely cloud-native, single-vendor SASE platform with AI-native management.
Key Strengths:
- Cato SASE Cloud built on a single codebase, policy engine and data lake for genuine convergence.
- Private global backbone connecting over 85 PoPs without traversing the public internet for core transit.
- Mature single-vendor stack with every security function native to the platform (no acquired/integrated products).
- Agentic AI used for autonomous threat detection and policy optimisation across the global customer base.
- Strong track record for deployment speed, with many customers citing sub-30-day go-lives per site.
Trade-offs and Considerations:
- Single-vendor dependency – there is no option to "bolt-on" third-party SSE components within the Cato architecture.
- Managed service quality can vary depending on the specific MSASE partner; operational capability should be verified independently of the platform.
Offered SLAs:
- 99.999% service availability guarantee for the Cato SASE Cloud backbone.
- 15-minute response time for Priority 1 cases under the premium support tier.
SOC & NOC Geographic Presence:
The private global backbone is monitored 24/7 by the Cato NOC, with optional managed SOC services provided via their MDR partner ecosystem.
Platform Review
Cato's platform has a single codebase, a single policy engine and a single data lake - which is architecturally different from providers that have assembled their SASE offering by acquiring and integrating separate products. The practical benefit is that every security and networking function shares the same traffic visibility and policy context, enabling genuine convergence rather than just consolidated billing. The global private backbone connects over 85 PoPs without traversing public internet between locations, delivering an SLA-backed 99.999% uptime commitment and consistent latency performance for distributed enterprises. AI capabilities are embedded across the platform - from threat detection and policy optimisation to agentic AI for autonomous management - trained on traffic data from the entire customer base across all PoPs.
Service Tiers
Cato's management model is offered in three tiers: Fully Managed, Co-managed and Self-managed. In the fully managed model, a certified MSASE partner handles 24/7 operations, monitoring and policy changes. Co-managed allows customer IT teams to retain specific policy controls while the partner manages infrastructure. Self-managed gives the customer full direct control over the Cato management console. All three models leverage the same underlying cloud platform and single-pane-of-glass management interface.
Security Posture
Security is native to the Cato SASE Cloud, with SWG, CASB, DLP, IPS and ZTNA all running as a single service on every PoP. This means policy is applied once, regardless of where the user is connecting from (office, home or roaming). The platform’s MDR service provides managed detection and response, utilising the unified data lake to identify threats that might be missed by standalone point products that lack full network visibility.
Recent Integrations
Cato's most recent significant capability additions include agentic AI for autonomous policy management and endpoint protection integration within the SASE Cloud, further consolidating security functions into the single codebase architecture.

Aryaka
Aryaka delivers Unified SASE as a Service from its own private global backbone – more than 40 PoPs delivering sub-30ms latency to 95% of the world's business population. The platform covers SD-WAN, Universal ZTNA, SWG, FWaaS, CASB, Next-Gen DLP and AI>Secure for GenAI traffic protection, delivered fully managed, co-managed or self-managed with Day 1 SLA enforcement. Aryaka is headquartered in Santa Clara, California.
Best for: Global enterprises where WAN performance is non-negotiable and generative AI security is a growing priority.
Key Strengths:
- Unified SASE 2.0: Launched November 2025, adding Universal ZTNA, AI>Secure for GenAI protection, and Next-Gen DLP with AI-powered NLP.
- Private Global Backbone: Over 40 PoPs delivering sub-30ms latency to 95% of the world’s business population; avoids the unpredictability of public internet overlays.
- GenAI Security (AI>Secure): Blocks prompt injections, jailbreaks, and token flooding—currently the most comprehensive GenAI security suite in the sector.
- Market Recognition: Ranked #1 in SASE on G2 in Summer 2025, noted for support quality and ease of doing business.
- Financial Predictability: All-in-one subscription eliminates hardware refresh capex and includes Day 1 SLA enforcement with no "stabilisation" period.
Trade-offs and Considerations:
- Proprietary ANAP appliances offer fewer granular user-configurable routing options than some legacy hardware competitors.
- Premium positioning: While performance is industry-leading, organizations with basic security-only needs may find lower-cost alternatives.
Offered SLAs:
- 99.999% uptime guarantee for the global private core network.
- Guaranteed <30ms latency for 95% of the global business population connecting to the core.
SOC & NOC Geographic Presence:
Operates a 24/7/365 NOC presence across 40+ global Points of Presence (PoPs) including hubs in Ashburn, London and Singapore.
Platform Review
Aryaka's platform is built around a private global backbone rather than a software overlay on the public internet. Its over 40 PoPs are interconnected by Aryaka's own network, delivering sub-30ms latency to 95% of the world's business population - which matters for latency-sensitive SaaS applications, real-time collaboration and multinational enterprises with demanding user experience SLAs. The Unified SASE 2.0 platform covers SD-WAN (SmartCONNECT), Universal ZTNA, SWG, FWaaS, CASB, Next-Gen DLP and AI>Secure for GenAI traffic protection - all in a single converged platform. SmartManage provides 24x7x365 NOC operations with predictive analytics and automation via EagleEye and ANMC and SLAs are enforced from Day 1 with no stabilisation period.
Service Tiers
Aryaka offers three management models. SmartManage (Fully Managed) provides 24x7x365 NOC coverage, predictive analytics and Day 1 SLA enforcement. Co-managed allows customer IT teams to retain specific policy controls via the EagleEye portal whilst Aryaka handles underlying infrastructure. Self-managed allows customers to utilise the platform independently. The subscription model includes the underlying backbone and hardware, removing the need for periodic CAPEX-heavy refreshes.
Security Posture
Security is native to the platform, with SWG, Universal ZTNA, FWaaS and Next-Gen DLP all running on the global backbone. AI>Secure provides specific protection for GenAI traffic (ChatGPT, Microsoft Copilot, etc.), blocking prompt injections and token flooding. Because security is converged with the network, Aryaka provides a single data lake for all traffic, allowing for more accurate threat detection than multi-vendor solutions that require separate data sources to be integrated.
Recent Integrations
Aryaka launched Unified SASE as a Service 2.0 in November 2025, adding Universal ZTNA, AI>Secure and Next-Gen DLP to the platform. The release was driven by customer demand for GenAI security and expanded hybrid workforce support - with over 100 enterprise customers already live on Unified SASE 1.0 at launch. AI>Secure became available in Q1 2026. G2's Summer 2025 rankings placed Aryaka #1 in SASE, reflecting strong customer satisfaction scores for support quality and ease of doing business.
How we assessed managed SASE providers (2026)
The ten providers in this guide were selected based on a multitude of factors that leads us to the opinion that they can be considered ‘the best’ SASE providers on the market - the methodology below sets out the criteria, evidence types and inclusion rules we used to build and assess the comparison set.
Editorial policy:
Netify operates as an independent marketplace and research platform and we don't accept payment from vendors in exchange for inclusion in or favourable positioning within, our market guides. All providers in this guide were selected based on their capability to deliver managed SASE at enterprise scale across multiple countries (rather than based on any commercial relationship with Netify).
Provider assessments are based on publicly available information, vendor-provided documentation, product briefings and Netify's ongoing review of procurement outcomes and where vendor claims couldn't be independently verified, we've noted this in the relevant review section.
Given that the managed SASE market is constantly changing, we'd recommend independently verifying current product capability, pricing and SLA terms directly with any shortlisted providers before making procurement decisions and should you spot any inaccuracies or have additional evidence that should inform a vendor assessment, please get in touch with the Netify research team.

Harry holds a BSc (Hons) in Computer Science from the University of East Anglia and is ISC2 Certified in Cybersecurity (CC). He serves as a Cybersecurity Writer here at Netify, where he specialises in enterprise networking technologies. With expertise in Software-Defined Wide Area Networks (SD-WAN) and Secure Access Service Edge (SASE) architectures, Harry provides in-depth analysis of leading vendors and network solutions.
Fact checked by: Robert Sturt - Managing Director, Netify
Frequently Asked Questions
The questions below address the most common points of confusion that Netify have noted typically arise during managed SASE procurement.
What is managed SASE?
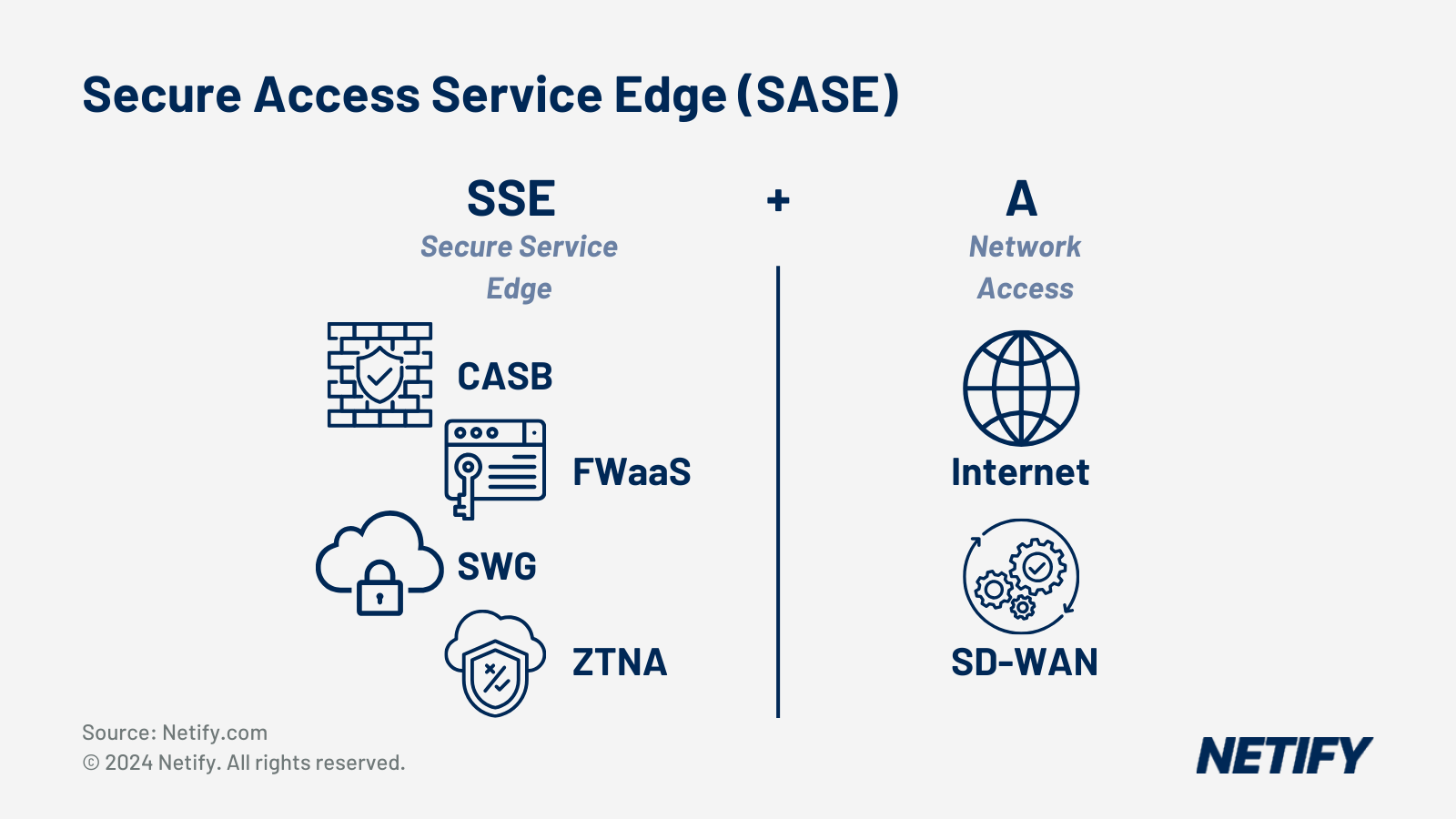
Managed SASE is a fully outsourced service where a provider designs, deploys and runs your networking and security platform on your behalf. SD-WAN, ZTNA, SWG, CASB, FWaaS and the underlying fabric are all managed by your provider's engineers rather than yours, typically consumed on a per-user or per-site subscription.
What is the difference between SASE and SSE?
SSE is the security half of SASE, covering ZTNA, SWG, CASB and FWaaS delivered from the cloud. SD-WAN is the networking half, handling how traffic routes between sites, users and cloud applications. Many organisations start with SSE and add SD-WAN as their network refresh cycle allows, with full SASE converging both into a single platform through one console.
How do providers deliver SASE as a service today?
Three models are most common - fully managed, co-managed and DIY/self-managed.
- Fully managed means the provider owns design, deployment, policy, monitoring and incident response.
- Co-managed means the customer retains control of specific elements (typically identity or application policies) whilst the provider handles infrastructure.
- Self-managed means the provider supplies the platform and the customer manages configuration.
In 2026, most enterprise procurement is focused on fully managed and co-managed.
What does 'single-vendor SASE' mean?
Single-vendor SASE is the combination of SD-WAN and SSE, delivered from one platform through one console, which benefits organisations by reducing integration complexity, enforcing policy consistently and providing a single accountability point - Gartner projects that by 2028, 70% of SD-WAN purchases will be part of a single-vendor SASE offering, up from 25% in 2025. Two examples of single-vendor SASE are Cato Networks and Aryaka, where SASE is natively offered all under their management.
Which SASE providers have the best global PoP coverage?
Whilst many organisations will instantly look for the best global PoP coverage, we’d suggest that PoP coverage only actually matters relative to where your users and sites actually are. We'd therefore recommend asking for a PoP map specific to your target geographies and SLA-backed latency commitments for those regions rather than relying on global averages.
Cato (over 85 PoPs on a private backbone) and Aryaka (over 40 PoPs with a sub-30ms SLA to 95% of the world's business population) tend to offer the strongest depth outside North America and Europe, though we'd always suggest verifying via architecture documentation and customer references rather than marketing materials.
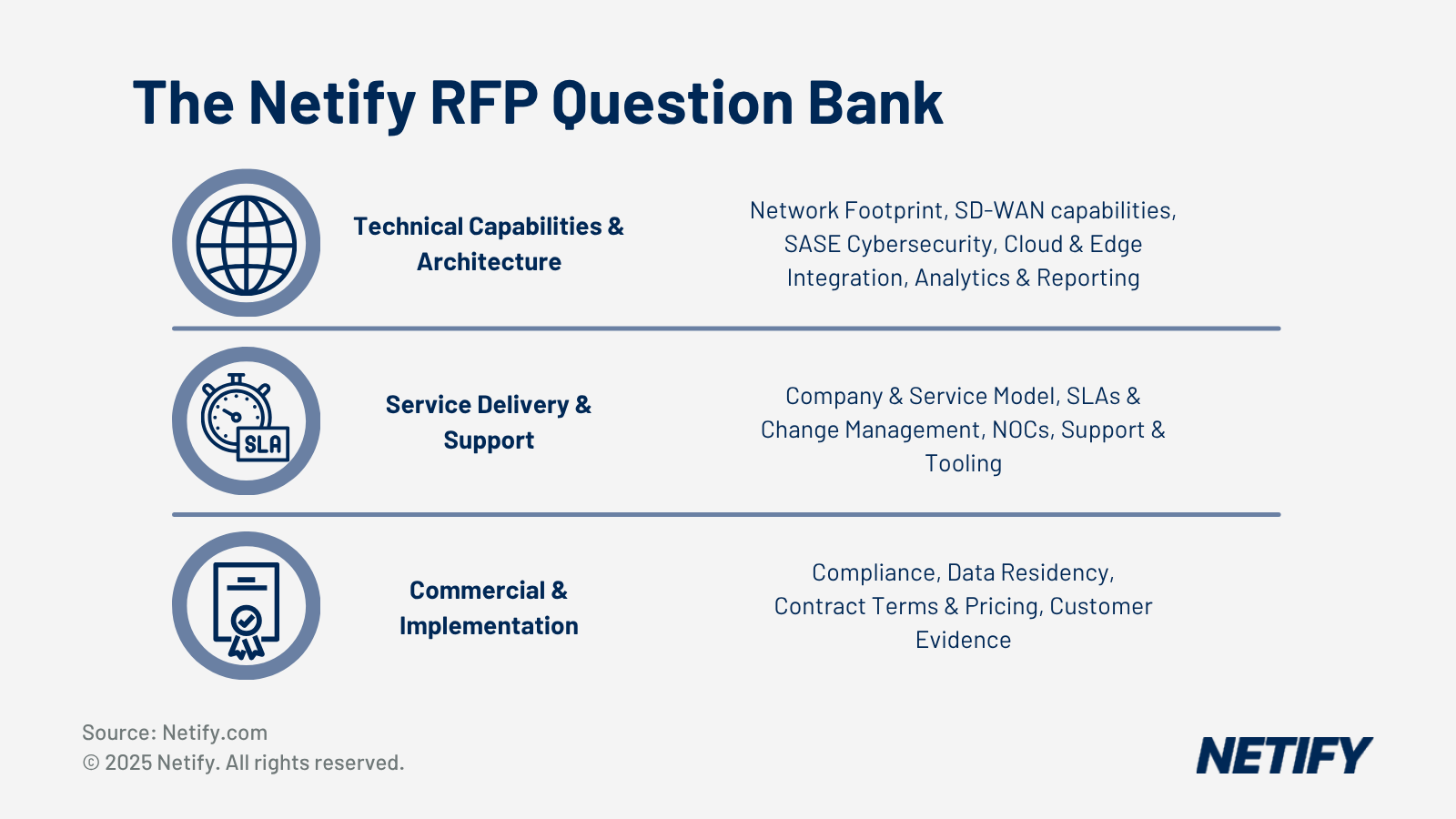
What should a global enterprise include in a managed SASE RFP?
At minimum your RFP should cover your current WAN technology, site count, user count and cloud platforms, security and compliance requirements, geographic footprint and data residency needs, preferred managed model, SLA requirements for uptime, latency and incident response and SIEM, as well as ITSM integration requirements. It's also worth including a request for a reference customer of comparable size and geography.
Whilst this might sound like quite a lot to include and knowing where to start can quickly become confusing, Netify's RFP builder is the ideal solution as it generates a structured template from your answers and offers a market full of SASE (& SD-WAN) providers, making it not only a much simpler way to create an RFP but also the perfect starting point in your procurement journey.
How long does a multinational SASE rollout typically take?
In our experience, for a mid-sized rollout with ZTP-capable hardware, a few months is a realistic expectation for most organisations. For complex multinationals operating across multiple regulatory jurisdictions, 12 months or more is common. The fastest deployments tend to use documented ZTP and standardised playbooks, with Cato and Aryaka both citing sub-30-day go-lives per site - though we'd always recommend asking for a reference deployment timeline from a comparable customer before committing.
What are common pitfalls when replacing VPN and branch firewalls with SASE?
The most common pitfall is underestimating dependency mapping. Legacy VPN environments tend to have informal access rules that only surface when they break, which is why a phased migration is significantly lower risk than a single cutover. Organisations also frequently underestimate the identity infrastructure requirements for ZTNA, as your IdP needs to be in good shape before access policies can be enforced consistently. End-user change management is also worth planning carefully, as staff used to always-on VPN will notice any disruption during the transition.
Want to create your own SASE RFP for free? The Netify SASE RFP builder is the best place to start!